been deep in the border control section for the past couple days and the design claim here is one of the more ambitious ones in the whole whitepaper 😂
honestly? the problem it is trying to solve is real and genuinely hard.
countries want to share security threat information at borders. they also dont want to hand their sensitive citizen and watchlist data to foreign governments. those two goals have be en in tension for decades.
bilateral data sharing agreements are slow, politically complex, and create security risks on both sides.
the SIGN approach flips the model.
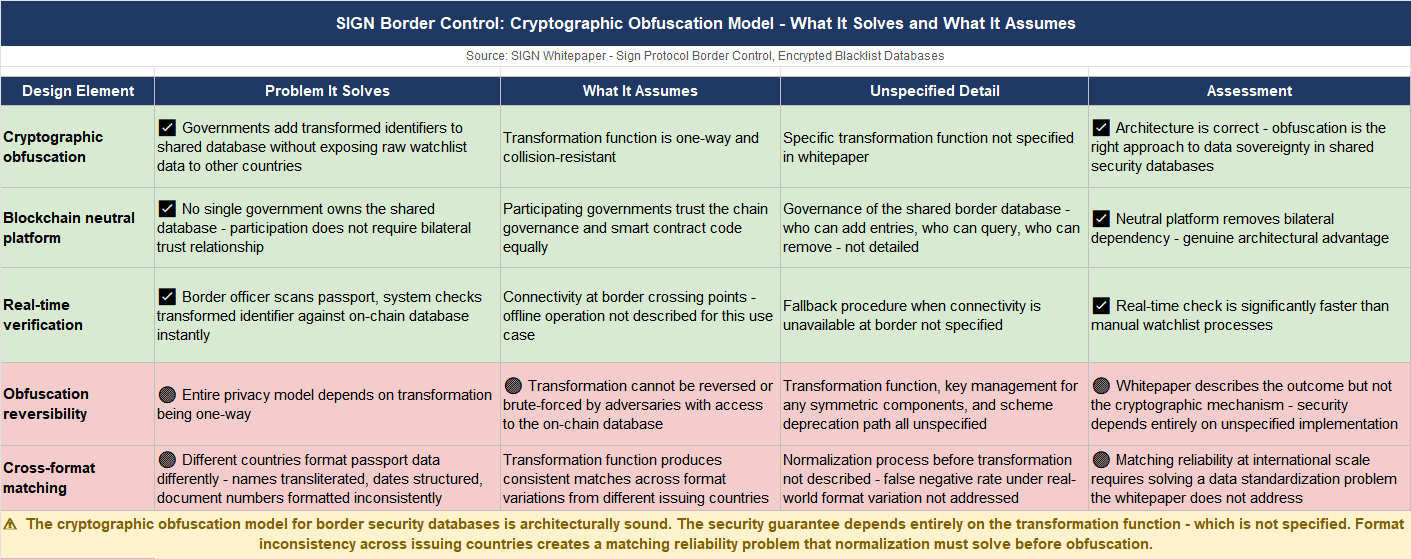
instead of sharing the underlying data, governments share cryptographically obfuscated identifiers on-chain. personal identifiers go through a hashing or encryption process before they hit the chain...
what sits on-chain is not a name, a paSsport number, a date of birth. it is a transformed version that cannot be reversed to reveal the underlying identity without the appropriate key.
when a border control officer scans a passport, ,the system generates the same transformed identifier for that document and checks it against the on-chain database. match found - security flag raised. no match - cleared. the officer never sees the underlying data from the other country.
the other country never handed over its raw watchlist. both sides cooperated without either side losing control of their sensitive data.
what that gets right is the architecture of the trust problem.
the blockchain provides a neutral platform - no single government owns it, no bilateral trust relationship is required to use it. a government adds its obfuscated identifiers to the shared database. any other participating government can check against them.
the cooperation happens at the cryptographic layer, not the diplomatic one.
the part i kept working through is the transformation function itself.
the security of this entire model rests on the obfuscation being one-way. if the transformation can be reversed - or if the transformed identifier leaks enough information to allow correlation back to the original - the privacy guarantee collapses.
the whitepaper describes personal identifiers as cryptographically obfuscated and stored on-chain.
it does not specify the transformation function, the key management model for any symmetric components, or what happens if the obfuscation scheme is broken or deprecated.
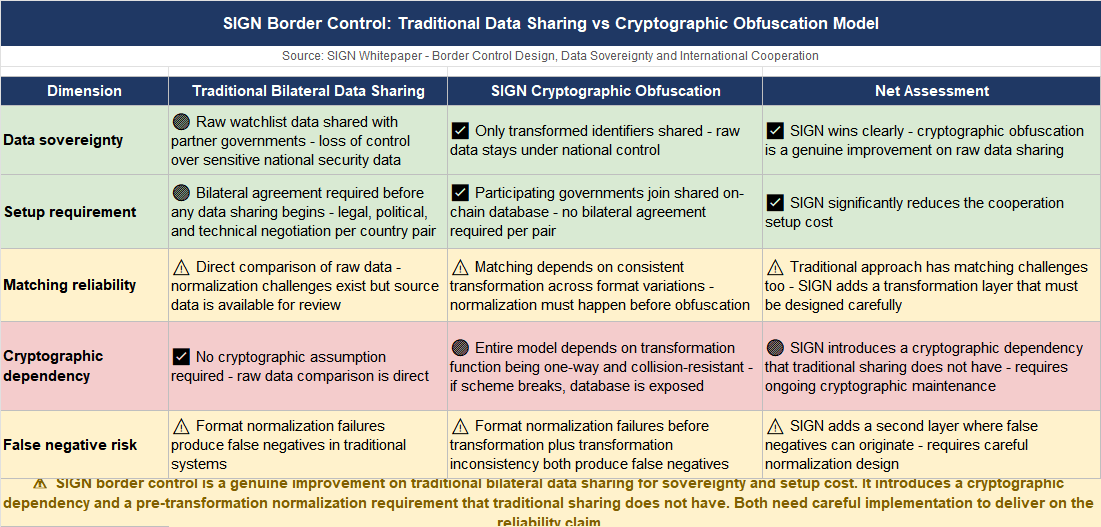
there is also a matching problem.
passport data contains fields that vary in format across issuing countries. names transliterated differently. dAtes formatted differently.. document numbers with different structures. the transformation function has to produce consistent matches across these variations or the false negative rate - cleared when it should flag - becomes a real operational problem.
honestly dont know if the cryptographic obfuscation model for border security databases is a genuine solution to the data sovereignty problem in international security cooperation, or a design that works elegantly in the clean case and accumulates eDge cases wherever real passport data meets format inconsistency.
data sovereignty preserved thrOugh cryptography that makes international security cooperation possible without data sharing - or a matching model whose reliability depends on implementation details the whitepaper leaves unspecified?? 🤔
#SignDigitalSovereignInfra @SignOfficial $SIGN
