past few days ive been pulling apart the verifiable credentials trust model and there is a question buried in it that the documentation answers technically but not fully 😂
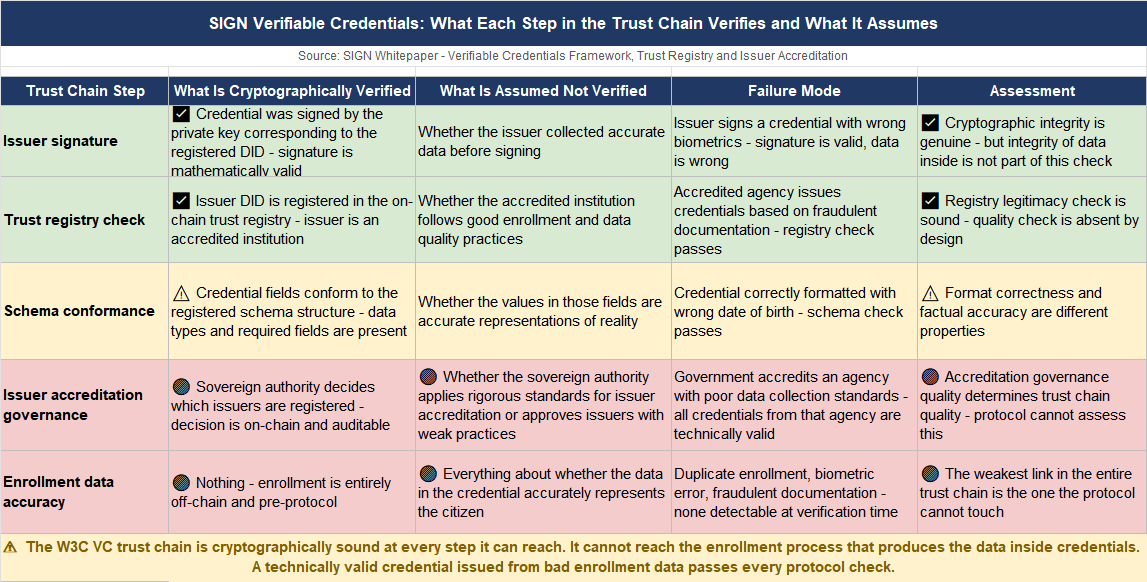
honestly? the W3C VC flow looks clean on paper. an issuer creates a credential. a holder stores it. a verifier checks it. the trust registry on-chain confirms the issuer is legitimate. nobody needs to call a central authority at verification time. the whole thing is cryptographically self-contained.
but i kept asking one question the whole time i was reading it.
who decides who gets to be an issuer.
the answer is the trust registry. issuers register their DIDs and public keys on-chain. verifiers query the registry to confirm an issuer is legitimate before accepting a credential. a credential from an unregistered issuer fails verification. clean gate.
the part underneath that gate is where i got stuck.
the trust registry has a governance framework. the docs describe it as clear policies defining issuer accreditation, credential standards, and dispute resolution - implemented through blockchain-based governance mechanisms. that sentence does a lot of work.
who runs those governance mechanisms. in a national deployment the answer is the sovereign authority. the government decides which agencies can issue credentials. the government decides which institutions are accredited. the government decides which credential schemas are valid. the blockchain makes those decisions immutable and auditable. it does not make them correct.
here is the concrete version of the problem.
a government registers three agencies as legitimate credential issuers. one of those agencies issues credentials based on flawed enrollment data - wrong biometrics, duplicate records, fraudulent documentation. the credentials are cryptographically valid.
they conform to the schema. they pass verification. the trust registry says the issuer is legitimate. every technical check passes.
the problem is not in the cryptography. it is not in the protocol. it is in the data the issuer put into the credential at enrollment time. and the protocol has no mechanism to detect that.
what the design gets right is the separation of verification from trust.
a verifier doesnt need to call the issuing agency to check a credential. the on-chain registry handles that. the cryptographic signature handles integrity. for a national system operating at scale across thousands of verifiers that is a genuine architectural win.
the gap is that issuer legitimacy and issuer quality are two different things. the registry confirms an issuer is registered. it says nothing about whether the issuer follows good enrollment practices, maintains accurate data, or catches its own errors before credentials reach citizens.
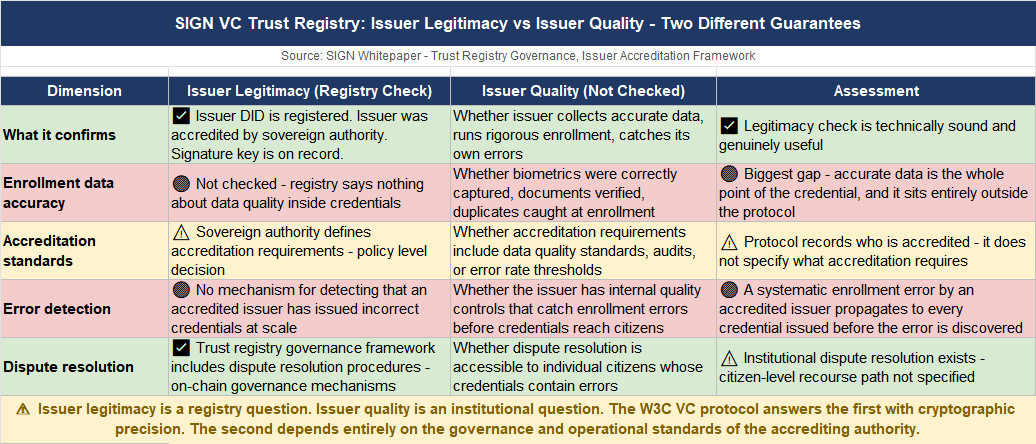
honestly dont know if the W3C VC trust model is strong
enough for sovereign identity at national scale, or whether it solves the verification problem cleanly while leaving the data quality problem entirely to the institutional layer it sits on top of.
trustless verification built on a trust registry that assumes the issuers it registers are doing their job correctly — or a cryptographic system whose strength ends exactly where the human enrollment process begins?? 🤔
#SignDigitalSovereignInfra @SignOfficial $SIGN
