Let me be straight with you—proxy contracts sound like the most boring topic in crypto… until you realize they’re quietly one of the most powerful (and dangerous) tools out there.
At the heart of it is the Sign Protocol hooked up with upgradeable proxy patterns. What that really means is simple: the system you’re trusting today can completely change its rules tomorrow, and your wallet would never even notice.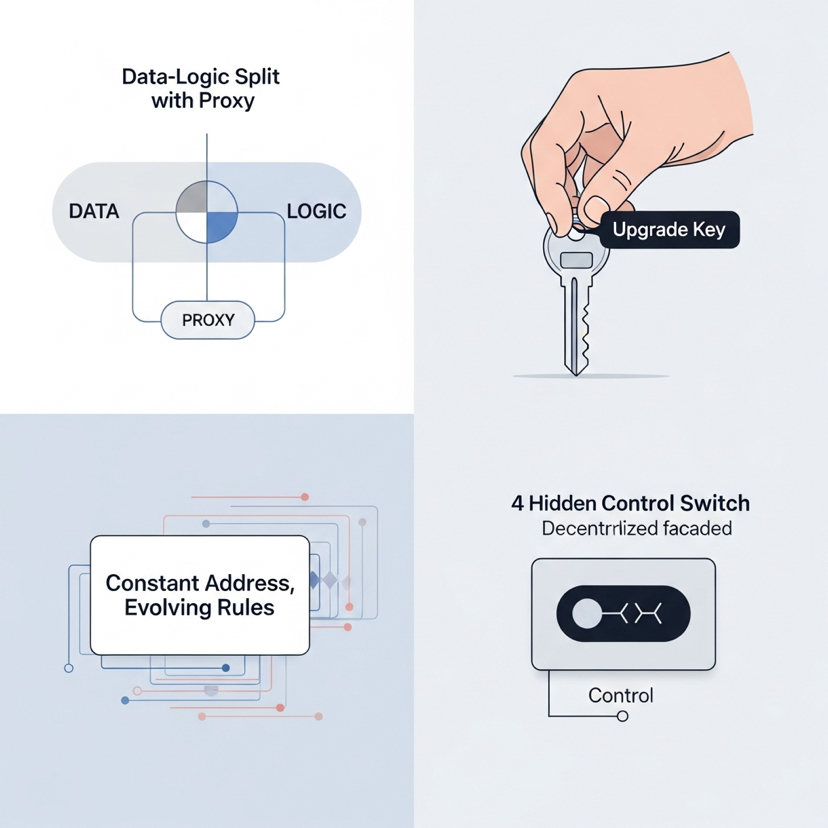
Here’s how the trick works.
Instead of putting everything—data, balances, identity, history—into one rock-solid, unchangeable contract, developers split it in two. One contract just holds your data. The other holds the actual logic and rules. Then they put a proxy contract in front of it all. You never talk directly to the real logic; you only ever interact with the proxy.
The killer feature? The logic contract can be swapped out at any time. Same proxy address. Same user accounts. Completely different rules. That’s what they call an “upgrade.”
On paper it sounds smart. Bugs happen. Features need to improve. Nobody wants to force a million users to migrate every time something breaks. So the upgradeable proxy looks like a clean, user-friendly solution.
But here’s where it gets serious.
If a government, a foundation, a company, or any central authority controls that upgrade key, they don’t need to shut anything down. They don’t need loud freezes or dramatic blacklists. They just push a new implementation behind the proxy.
Suddenly transactions can be filtered.
Permissions can be changed.
Access can be restricted.
Rules can tighten overnight.
And you’re still using the exact same contract address. Everything looks normal. No migration. No warning. Just quiet control.
The Sign Protocol makes this even smoother because it weaves identity, approvals, and validation straight into the system. Now upgrades aren’t just technical tweaks—they can decide who’s allowed to do what, all without anyone noticing the hand on the lever.
That’s the quiet power of these patterns: no disruption, no migration, just total control behind the scenes. The whole thing still feels decentralized on the surface, but there’s a hidden master switch built right in.
Look, I’m not saying upgrades are evil. Without them most projects would die or become useless. But let’s stop pretending this is neutral technology. Whoever holds the upgrade rights holds the real power. Period.
Whether it’s a small dev team, a VC-backed company, or a government doesn’t matter—the risk is the same. What starts as “maintenance” can quickly become policy pushed straight through code. And the scariest part? It never looks like control. It always looks like an innocent upgrade.
That’s exactly why I don’t blindly trust anything upgradeable anymore.
It’s convenient as hell, sure. But it trades real permanence for flexibility—and flexibility always ends up belonging to whoever’s in charge.
So do yourself a favor: before you put a single dollar or a single piece of your identity into any protocol, go check who actually controls the upgrade key.
That person (or entity) is the real owner. Not the pretty code you see. Not the marketing. Not the whitepaper.
The code you interact with is just the front door. The upgrade key is the master key to the entire house.
Keep learning. Keep asking the uncomfortable questions. This space only gets safer when we stop treating convenience as trust.
Stay sharp out there.
