I was reading through SIGN’s litepaper and some of the live product stuff this week, mostly because I kept seeing it framed as credential verification plus token distribution. Which, on first pass, sounds almost too tidy. An issuer creates an attestation, a user proves eligibility, tokens get distributed. End of story.
That’s probably how most people think about it. SIGN as a nicer airdrop machine, maybe with some identity rails underneath. Something for badges, grants, whitelists, contribution proofs, reward campaigns. Operational tooling, useful but not especially deep.
but that’s not the full picture.
What looks simple here is the attestation itself. A signed claim about a wallet or identity. Fine. But once that claim is meant to be reusable across apps, chains, and organizations, it stops being just a message and starts acting more like trust infrastructure. You need shared schemas, clear issuer semantics, revocation paths, and some way to keep claims useful without exposing more data than necessary. and that’s where it gets interesting, because the system is really trying to sit between social trust and onchain execution — which is usually where things get messy.
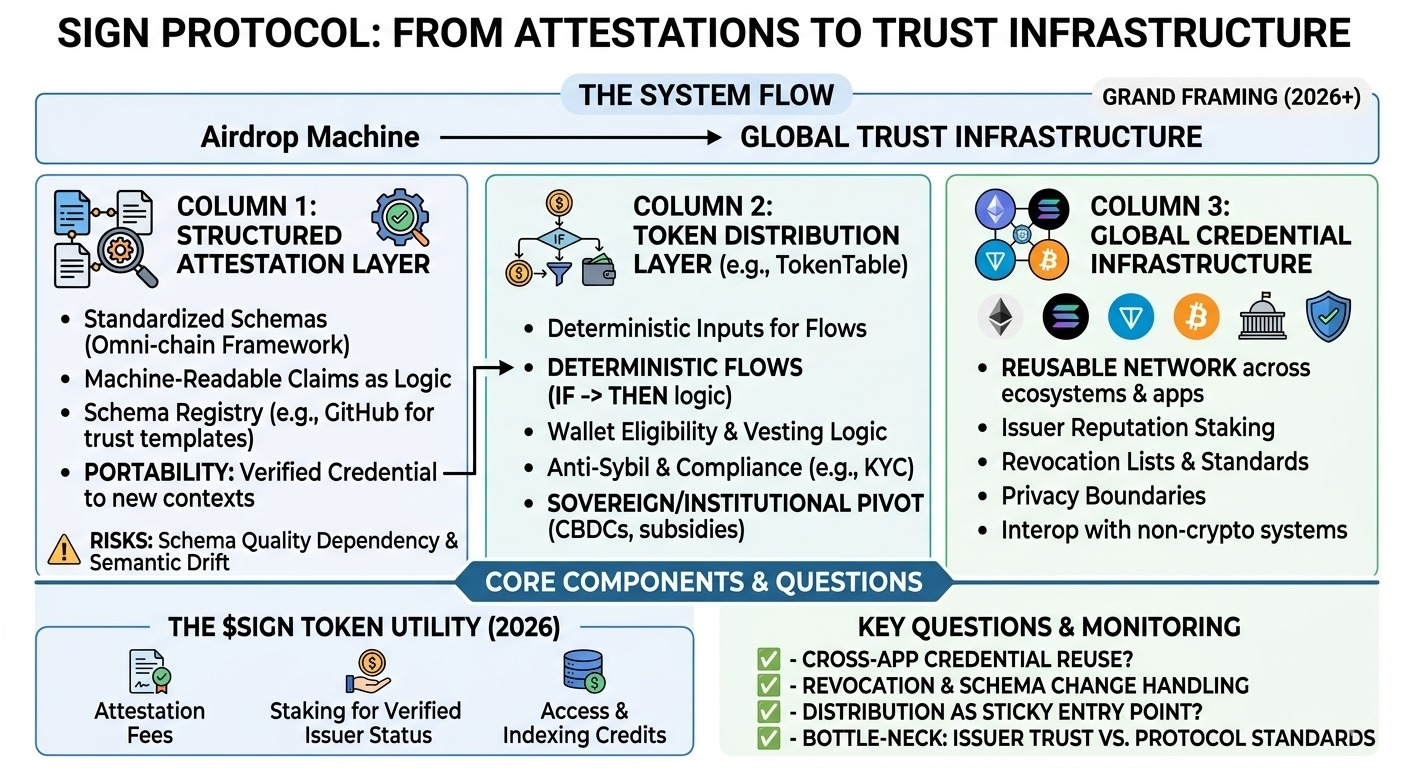
The first mechanism that stands out is the structured attestation layer. From what I can tell, SIGN isn’t just storing arbitrary proofs; it’s trying to make claims machine-readable in a standardized way. That matters more than it sounds. If an attestation has a known schema, then downstream apps can actually consume it as logic, not just display it as metadata. A user could carry a verified credential from one context into another: contributor status, KYC-like verification, governance eligibility, maybe proof of participation. That’s the nice version. The less nice version is that schema quality becomes a real dependency. If different issuers define similar credentials differently, or if the semantics drift over time, portability gets weak fast. Standardized data does not automatically create standardized trust.
The second mechanism is the token distribution layer built on top of those attestations. This feels like the most concrete thing SIGN has today. There are already live products around claims and distribution, which honestly gives me more confidence than the grand framing does. Distribution sounds boring until you’ve had to run it. You need wallet eligibility, anti-sybil filters, vesting logic, claim periods, maybe geographic restrictions, all while keeping a paper trail clean enough that no one argues forever after the fact. If SIGN is turning attestations into a deterministic input for those flows, that’s real infrastructure. But here’s the thing: distribution systems only look neutral on the surface. Whatever assumptions sit inside the credential layer get enforced downstream in a much harder way once tokens are involved.
The third piece is the broader idea of “global infrastructure” for credential verification. Some of that is already real, at least in a narrow sense. The attestation tools exist, the claims rails exist, teams are using them. So this isn’t purely roadmap theater. But the larger ambition — a reusable credential network across ecosystems, apps, and maybe institutions — still feels very much phased. That depends on more than contracts and APIs. You need issuer reputation, revocation standards, privacy boundaries, and probably interoperability with systems that don’t think in crypto-native terms at all. That’s a much slower build than shipping claim pages.
My main open question is where the trust bottleneck ends up. maybe it remains distributed across issuers. maybe SIGN becomes the default coordination layer and centralizes soft power there. I’m also a little unsure about $SIGN in all this. It may eventually coordinate incentives around issuers, verifiers, or network usage, but right now the utility of the products is easier to explain than the necessity of the token.
watching:
- whether credentials created in one app actually get reused elsewhere
- how revocation and schema changes are handled once downstream systems depend on them
- whether token distribution stays the sticky entry point while the broader credential network matures slowly
- how much trust ends up sitting with issuers, versus with the protocol and its standards
$SIGN @SignOfficial #signdigitalsovereigninfra