When I first started working with SIGN, I honestly thought it would be just another digital system, some identity tool, some database, maybe a blockchain component. But the moment I got involved in a real sovereign deployment, I realized something much bigger was happening. SIGN wasn’t software, it was an entire operational structure. It felt like stepping into the control room of a country’s digital nervous system.
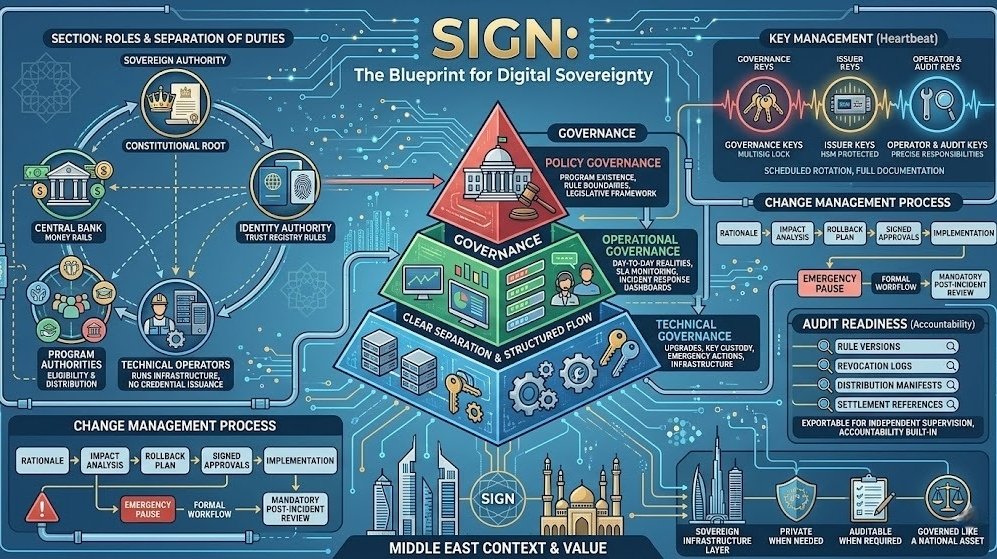
My first real understanding came during a governance review session. Three layers, policy, operational, and technical, each handled by different authorities. It surprised me how clearly everything was separated. Policy governance decided what programs even existed and what rules should bind them. Operational governance handled the day-to-day realities, SLAs, incident response, real monitoring dashboards. And technical governance quietly ensured upgrades, key custody, and emergency actions never happened impulsively. Nothing moved without structure, approval, and traceability.
I remember seeing for the first time how roles were divided. The sovereign authority acted like the constitutional root of the system. The central bank controlled the money rails. The identity authority set the trust registry rules. Program authorities handled eligibility and distributions. Technical operators ran infra but never issued credentials. That separation of duties hit me deeply; it’s what made the system trustworthy.
Key management felt like the heartbeat of the whole setup. Governance keys locked behind multisig, issuer keys inside HSMs, operator and audit keys each serving precise responsibilities. Everything rotated on schedule, everything documented. I had never seen digital sovereignty implemented with this level of discipline.
The change management process impressed me most. Nothing was just pushed. Every modification required a rationale, an impact analysis, a rollback plan, and signed approvals. Even an emergency pause had a formal workflow and a mandatory post-incident review.
Over time, I also saw how audit readiness shaped the entire system. Every program had rule versions, revocation logs, distribution manifests, and settlement references, all exportable for independent supervision. It made accountability feel built-in, not added later.
Working with SIGN in the Middle East context made this even more meaningful. These countries are building new digital foundations for rapidly expanding economies, and SIGN fits perfectly as a sovereign infrastructure layer, private when needed, auditable when required, and governed like a national asset.
I went in expecting a tool. I came out realizing I had witnessed the blueprint for digital sovereignty.
@SignOfficial #SignDigitalSovereignInfra $SIGN