#SignDigitalSovereignInfra @SignOfficial $SIGN 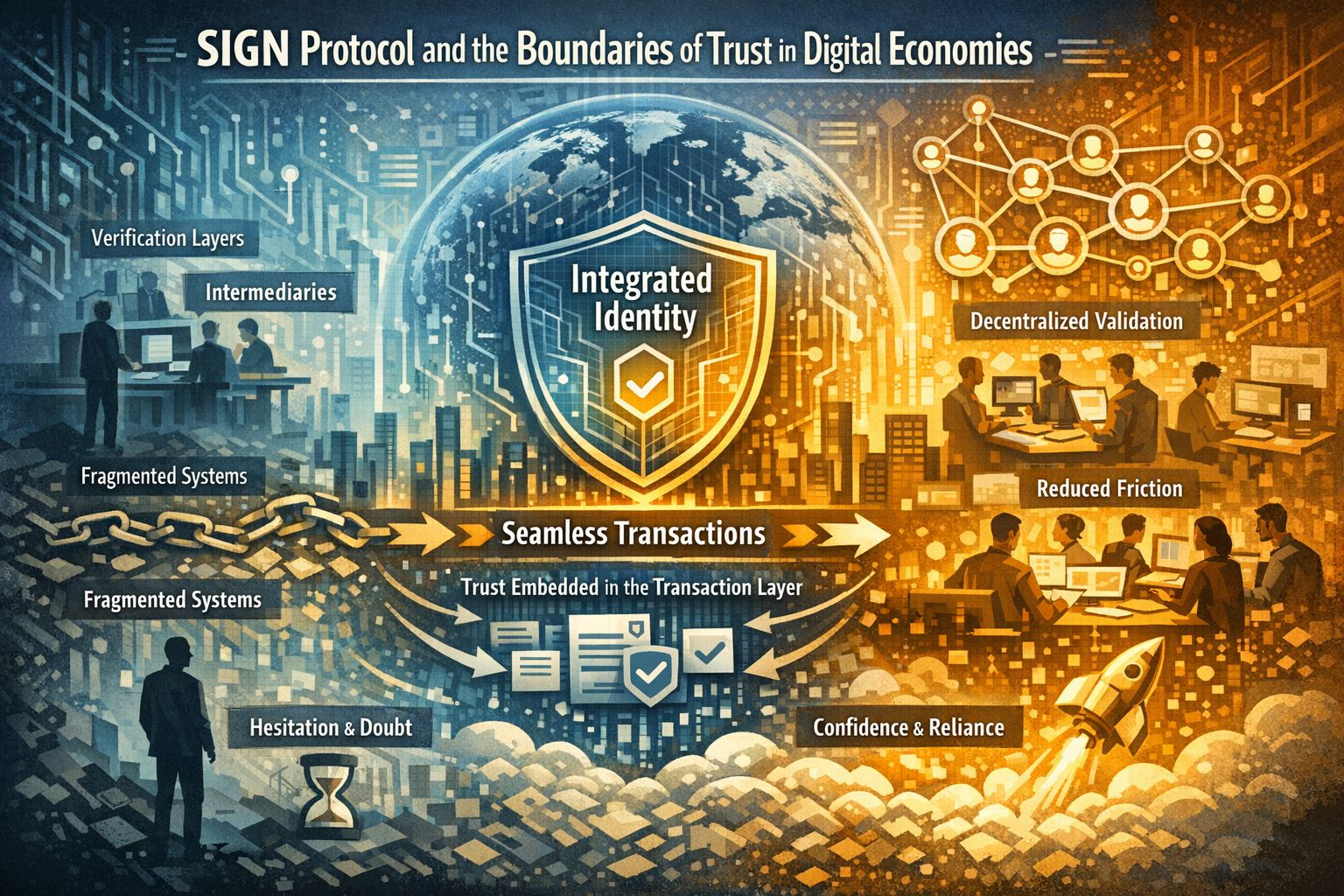 I’ve spent enough time in crypto to recognise how easily I get pulled into narratives that feel structurally inevitable. Identity has been one of those ideas for mesomething that always sounded foundational, almost overdue, yet rarely showed up in the workflows I actually used. I remember following projects that positioned identity as a missing layer for everything, only to realise later that my behaviour as a user hadn’t changed at all. That gapbetween what feels necessary and what becomes embeddedis where my skepticism started to settle. Renaming it as SIGN Protocol doesn’t change that instinct; if anything, it sharpens the question of whether this is infrastructure or just another convincing abstraction.
I’ve spent enough time in crypto to recognise how easily I get pulled into narratives that feel structurally inevitable. Identity has been one of those ideas for mesomething that always sounded foundational, almost overdue, yet rarely showed up in the workflows I actually used. I remember following projects that positioned identity as a missing layer for everything, only to realise later that my behaviour as a user hadn’t changed at all. That gapbetween what feels necessary and what becomes embeddedis where my skepticism started to settle. Renaming it as SIGN Protocol doesn’t change that instinct; if anything, it sharpens the question of whether this is infrastructure or just another convincing abstraction.
What shifted my perspective wasn’t a feature announcement, but repeated interaction with systems where identity wasn’t presented as a step, but as a condition. In SIGN Protocol, when identity is integrated directly into the transaction layer, it doesn’t ask for attentionit shapes outcomes quietly. I don’t find myself verifying credentials mid-flow, yet the system behaves as if certain checks have already been resolved. The effect is subtle but persistent: fewer interruptions, fewer external confirmations, and a noticeable reduction in the need to second-guess whether something actually happened. Identity, in this context, stops being a checkpoint and starts acting like a boundary around uncertainty.
This changes the role of trust in a way that’s easy to miss if you’re only looking at throughput or latency metrics. When identity is embedded, I’m no longer outsourcing trust to intermediaries in the same way. I’m not relying on external verification layers or post-transaction validation loops. Instead, the system pre-conditions what is allowed to occur. That shift compresses the range of outcomes I consider possible. It doesn’t eliminate risk, but it narrows ambiguity. Over time, that narrowing changes behaviour more than any improvement in raw speed ever could.
What I’ve found more interesting is how this plays out under repetition. A system like SIGN Protocol doesn’t prove itself in a single interaction. The real signal appears after dozens of transactions, when I stop consciously thinking about identity altogether. That’s where design decisions around privacy and verifiability start to matter. If identity feels intrusive, I notice it immediatelyI hesitate, I delay, I look for ways around it. But when it operates quietly in the background, balancing what needs to be revealed with what can remain abstracted, it becomes almost invisible. That invisibility isn’t a lack of presence; it’s a sign that the system is aligned with how I naturally operate.
There’s also a psychological layer that becomes more pronounced when identity is tied to financial activity. I’ve noticed that when verification is frictionless, it doesn’t just reduce effortit changes my willingness to act. I’m less cautious about submitting transactions, less inclined to double-check outcomes, and less likely to repeat actions unnecessarily. But when identity feels heavy or overly exposed, the opposite happens. Even small delays or unclear signals create hesitation, and hesitation spreads. In clustered environmentswhere many users are acting at oncethat hesitation becomes collective behaviour, not just an individual response.

The regional context adds another layer of complexity. In places undergoing rapid digital transformation, like parts of the Middle East, infrastructure decisions are not just technicalthey’re foundational to how coordination evolves across finance, trade, and public systems. What stands out to me is how separating identity from financial systems tends to create fragmentation over time. Multiple verification layers emerge, each slightly inconsistent, each introducing its own friction. When identity is integrated from the start, as in the case SIGN Protocol is attempting, that fragmentation has less room to develop. The system becomes more coherent, but also more dependent on getting those initial design choices right.
At the market level, I’ve learned to treat attention with caution. Activity often reflects expectation rather than usage. I’ve seen periods where identity-driven narratives attract significant interest, only for actual interaction to remain shallow. The difference becomes clear when you look at behaviour over time. Are users engaging with identity layers repeatedly, or only when prompted? Are developers building systems where identity is required, or merely supported? These are the signals that matter, and they’re often quieter than the narrative itself.
For me, the core test remains repetition. If SIGN Protocol is truly infrastructure, it should disappear into the background of everyday interaction. I shouldn’t have to think about it, explain it, or consciously engage with it. It should simply shape what is possible, consistently and predictably. That kind of presence doesn’t emerge from a single use case or a well-designed interface. It emerges from sustained, repeated reliance.
What would increase my confidence is straightforward, but not easy to achieve: consistent user interaction with identity layers without friction, applications where identity is essential rather than optional, continued validator participation that reflects real usage, and developer activity that persists beyond initial interest. What would reduce it is just as clear: identity remaining an add-on rather than a requirement, usage patterns that spike and fade, and systems where users still feel the need to verify outcomes externally.
The difference, in the end, is not conceptual. Many ideas in crypto sound necessary. Very few become necessary. The dividing line is whether users rely on them repeatedly, without thinking, until the system itself becomes indistinguishable from the workflow it supports. That’s the threshold SIGN Protocol has to cross, and it’s a much higher bar than the narrative suggests.
#SignDigitalSovereignInfra @SignOfficial $SIGN
