I was reading through the SIGN litepaper and clicking around some of the live product flows again last night, mostly because i kept seeing it described in that very tidy, compressed way: credential verification, token distribution, onchain attestations. and sure, if you only look at the top layer, that’s the story. a system for issuing a claim about a user and then using that claim to decide who gets a token or an access right.
That’s probably how most people file it away. a cleaner airdrop rail, a grants distribution tool, maybe some onchain badges with actual utility. useful, sure, but it feels like operational tooling rather than deep infrastructure.
but that’s not the full picture.
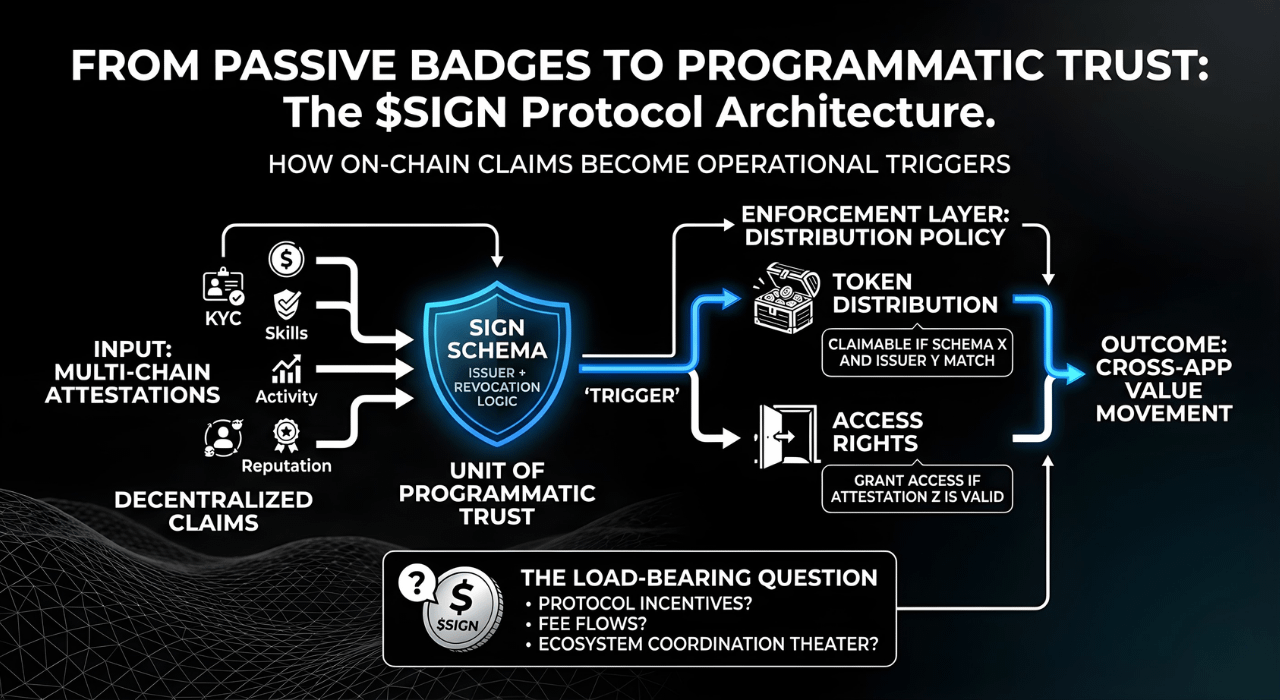
What seems more interesting is that SIGN is trying to make attestations operational, not just collectible. the difference is subtle but huge. a badge is a passive record; a credential that can be verified, interpreted, and plugged into distribution logic without the verifier having to rebuild the trust assumptions from scratch is a primitive. basically, they're trying to turn a claim into a programmatic trigger for value movement.
The first mechanism that really matters here is the schema-based attestation model. this sounds almost too basic to mention, but most identity systems fail because of semantic ambiguity. if an issuer says a user is “verified” or “eligible,” that statement is useless unless the verifier knows exactly what the criteria were and how the data is structured. SIGN’s use of schemas is what prevents the system from becoming just a pile of branded metadata. and that’s where it gets interesting: the real unit of trust isn’t just the issuer, it’s the issuer + schema + revocation logic. if those three stay stable, then another app can consume a SIGN credential as an infrastructure input instead of having to write custom glue code for every new partner.
Then there’s the distribution layer, which i think gets underrated because people hear “token distribution” and think of a simple claims page. But here’s the thing: distribution is where identity assumptions get stress-tested by incentives. It’s where you deal with the ugly parts—sybil resistance, replay protection, eligibility snapshots, and the general mess of updating recipient sets after a launch. SIGN isn’t just sending tokens; it’s functioning as an enforcement layer for distribution policy. This wallet can claim because it satisfies this specific attestation under this specific schema. That bridge from “fact” to “action” is the most practical part of the architecture, and it's probably why the attestation layer has any chance of gaining traction.
The third piece is the portability story—the “global infrastructure” part. in theory, a credential network only wins if attestations can travel across apps and chains without losing meaning. but portability is where these things usually break down. different ecosystems have different trust boundaries and different costs for verification. while the architecture is built for this, im still skeptical about how it handles the social side of trust. it’s one thing to have a cross-chain bridge for data; it’s another to get an app on chain A to trust an issuer on chain B without a centralized API gateway in the middle.
Some of this is clearly live today. the attestation product is in production, and the token distribution workflows are being used for real grants and campaigns. that matters because it moves the conversation from litepaper fantasy to actual product usage. the broader vision—the neutral, global credential layer—is still phased and contingent on broad issuer adoption.
And then there’s $SIGN. im still trying to decide how much of the token is actually load-bearing for the protocol versus ecosystem coordination theater. maybe it aligns validators or handles fee flows, but in a trust-centric system, the token’s role needs to be incredibly crisp. if the selling point is neutrality, you don't want the trust model to feel like it's being economically gamed.
My open question is whether SIGN becomes a broad verification substrate or just the best tool for a specific niche of distribution problems. there’s a gap between “useful for airdrops” and “the default layer for portable credentials,” and a lot of infra projects live in that gap forever.
watching:
- whether third-party apps verify SIGN attestations natively, without custom glue
- how revocation and issuer reputation behave at scale
- where $SIGN is actually required in the system versus just adjacent to it
- whether distribution products drive credential adoption, or the other way around
- how much of the cross-chain verification story is real today versus roadmap-shaped
$SIGN @SignOfficial #signdigitalsovereigninfra