The Global Infrastructure for Credential Verification and Token Distribution
@SignOfficial #SignDigitalSovereignInfra $SIGN
In many countries today, one of the biggest hidden problems is not the lack of resources, but the lack of trusted systems that can prove who deserves access, who has completed a requirement, who owns a right, and who qualifies for support. A student may complete training but wait months for a certificate to be verified. A farmer may qualify for assistance but face delays because records are scattered across departments. A small business owner may lose opportunities because identity checks, tax records, and licensing systems do not speak to each other. The deeper issue is that trust is still fragmented. Information exists, but institutions often cannot verify it instantly, securely, or fairly. This is where a global credential infrastructure built around SIGN introduces a very different model: one where verification becomes programmable, portable, and trusted across institutions.
At its core, this infrastructure is built on blockchain, but blockchain here is not simply being used as a ledger for transactions. Its larger role is to create a permanent trust layer where proofs can be anchored without depending on a single institution. When a credential is issued—whether it is an educational certificate, a business permit, a social welfare eligibility record, or a professional qualification—it can be registered in a form that cannot easily be altered later without detection. That changes how governments and institutions think about verification. Instead of repeatedly asking citizens to submit the same documents, agencies can verify proofs instantly through a trusted digital layer. This reduces duplication, cuts administrative delays, and limits manipulation.
The strongest part of such an infrastructure is that credentials do not need to remain trapped inside one ministry or one database. A national education authority, a health department, a labor ministry, and financial institutions can all operate through a uniform data schema. This means each institution uses compatible credential structures, even if they serve different purposes. A student graduating from a technical institute, for example, could receive a credential that is immediately understandable by employment systems, scholarship programs, and tax registration platforms. A uniform schema sounds technical, but in practice it means governments stop rebuilding trust every time data moves from one office to another.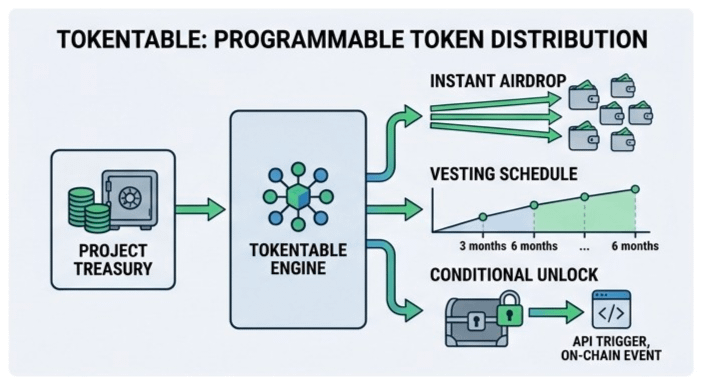
This also changes how token distribution can work. In many countries, aid programs fail not because funds do not exist, but because identifying rightful recipients remains difficult. Records may be outdated, duplicated, or influenced by local power structures. With verifiable credentials tied to clear qualification rules, tokenized distribution systems can direct support with far greater precision. A family verified through income criteria, geographic data, and approved records could automatically receive digital assistance without long manual approval cycles. The value here is not only speed it is traceability. Every distribution can be audited, every eligibility rule examined, and every outcome reviewed transparently.
One of the most important technologies supporting this future is zero-knowledge proof. This sounds complex, but its practical meaning is simple: a person can prove they meet a condition without revealing all personal data behind it. Someone could prove they qualify for a subsidy without exposing full income history. A student could prove certification without exposing unrelated academic records. A company could prove compliance without publishing sensitive internal data. In national systems, this matters because digital trust should not require unlimited exposure. Citizens increasingly want proof systems that protect dignity as much as they protect institutions.
Hybrid storage becomes necessary because not every piece of data belongs directly on-chain. Public blockchains provide immutability, but they are not ideal for storing sensitive national records in full detail. A hybrid model solves this by placing critical proof references on-chain while storing larger or sensitive information securely off-chain under controlled governance. In simple terms, the blockchain confirms that a record exists and has not been changed, while protected databases hold the actual content where required. This balance allows scalability without forcing governments to choose between transparency and privacy.
The national impact becomes larger when digital sovereignty is considered. Many governments increasingly worry about depending entirely on foreign digital systems for identity, records, and citizen verification. A sovereign credential infrastructure allows countries to maintain control over issuance rules, legal standards, and access policies while still remaining interoperable internationally. A worker trained in one country could present trusted credentials abroad without repeating verification from the beginning. A local business could prove compliance to foreign partners more efficiently. Sovereignty here does not mean isolation it means controlled participation in global digital trust networks.
Economic participation also changes when credentials become active rather than passive. Today, credentials often sit unused until manually requested. In a programmable infrastructure, credentials can trigger opportunity. Verified training could unlock funding access. Proven business compliance could enable faster lending decisions. Confirmed agricultural production could connect directly to subsidy systems or insurance programs. The credential stops being a static document and becomes an economic entry point. That is especially important in countries where millions remain excluded not because they lack ability, but because trusted digital proof is weak.
Still, no system should be described as perfect. Risks remain serious. Centralized governance inside a digital credential system can recreate old power structures if only a few institutions control issuance or revocation unfairly. Privacy failures can damage public trust permanently. Poor technical governance can create exclusion instead of inclusion if digital systems become inaccessible to rural populations or low-connectivity communities. Even blockchain itself does not automatically solve institutional bias. Technology only strengthens trust when governance is transparent and accountable.
A realistic example helps explain this clearly. Imagine a flood-affected district where emergency support must reach thousands of households quickly. Traditionally, local verification may take weeks, with repeated paperwork and inconsistent records. In a credential-based infrastructure, prior household verification already exists through trusted credentials issued earlier by relevant departments. Once emergency conditions are declared, approved aid tokens can move directly to verified recipients through programmable rules. Auditors can later confirm exactly how funds moved, while households receive support without repeated bureaucracy. That is not merely faster administration it changes how citizens experience the state itself.
The larger meaning of infrastructures like SIGN is that trust begins moving from isolated institutional databases toward shared, verifiable digital coordination. But success will depend less on technical language and more on whether ordinary people feel the system works fairly for them. If a graduate gets recognized faster, if aid reaches the correct family, if a small entrepreneur gains easier access to opportunity, then the infrastructure becomes meaningful. If not, even advanced systems remain abstract.
The future of credential verification is therefore not simply about digital documents or token flows. It is about whether nations can build systems where proof, access, privacy, and fairness evolve together. That future will require technical strength, institutional discipline, and public trust at the same time