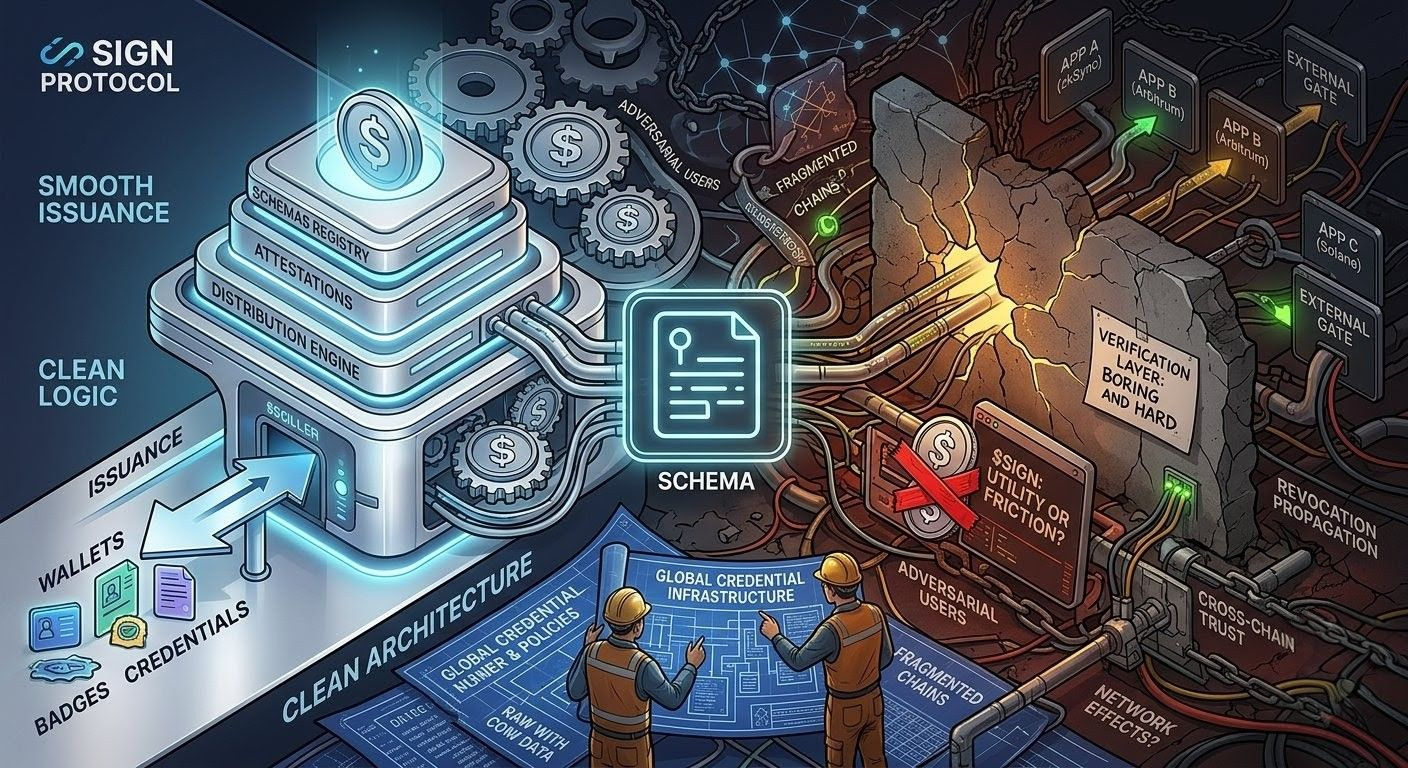
i was reading through the SIGN docs again, and it’s one of those projects where the surface level is so clean you almost don’t look for the cracks. you have schemas, you have attestations, you have a distribution engine. teams issue credentials to wallets, and then those wallets use them to claim tokens or access gated things. it’s the standard “identity and incentive” stack, easy to file away as just another way to run airdrops or loyalty programs.
but that’s not the full picture.
What actually matters isn't the badge, but the enforcement layer underneath. a lot of these projects solve for the “issuance” side and then hand-wave the “verification” side, or they build a shiny dashboard and ignore the fact that the actual data isn't composable. if SIGN is going to be “global infrastructure,” it has to solve for the scenario where an app on an entirely different chain wants to trust a credential issued by someone they’ve never met. that’s where the engineering gets boring and hard.
The core mechanism that holds this up is the schema registry. it sounds like a database feature, but it’s actually a trust-negotiation feature. if you don’t have a standard way to version and interpret a claim, you just have a giant pile of blobs. SIGN’s approach to structured schemas is what allows downstream apps to actually do something with the data without writing custom glue code for every issuer. and that’s where it gets interesting: once you have standard schema definitions, you aren't just storing attestations; you’re building a language for policy. an app can say “i only care about users who hold this specific schema, signed by this subset of trusted issuers.” that’s a real primitive.
The second bit is the coupling of those attestations with the distribution engine. this is where people mistake the protocol for a marketing tool. if you’re doing token distribution at scale, you have to deal with the reality that users are adversarial and infrastructure is fragmented. you need replay protection, you need to handle revocation when a credential is no longer valid, and you need to verify eligibility without blowing up gas costs. SIGN seems to be trying to bake that logic into the claim flow itself. it’s not just a receipt; it’s an entitlement. that’s a subtle shift, but it changes the protocol from a database of facts into an execution layer for distribution.
Some of this is clearly live today—the attestation issuance, the schema logic, and the production-grade distribution tools. that’s the “it works” part of the story. the “future promise” part is the network effect of third-party adoption. can i take an attestation from a SIGN-based issuer and use it to gate an app that has absolutely no relationship with the SIGN team? that’s the threshold for being “global infrastructure.” right now, it feels like the system is still heavily skewed toward the first-party or partner-campaign use case.
i do have a recurring doubt about the token, $SIGN. i keep asking myself if it’s load-bearing or just ecosystem signaling. if you’re building a neutral verification layer, the token needs to either solve a coordination problem (like spam or validator incentives) or it risks becoming a source of friction. if the protocol is supposed to be the base layer for other apps, does the token need to be involved in every request, or is it just for governance? if it’s the latter, is it really necessary? the danger with these protocols is that they start by being useful and end by being token-extractive.
my main open question is whether these systems actually want to be decentralized, or if they’re content being the “managed service” for high-stakes distribution. because there’s a difference between a protocol that lets anyone verify anything, and a platform that handles the hard parts of web3 growth for their clients. one is a utility, the other is a business. it’s possible to be both, but i’m watching to see which lane they actually occupy.
watching:
- whether third-party apps build on SIGN schemas without internal team support
- how revocation propagates across chains when attestations are reused by external parties
- what specific mechanism $SIGN provides that couldn't be solved by a flat fee or standard software contract
- the ratio of “first-party” vs “third-party” attestation traffic
- any signs of schema fragmentation as more independent issuers join the network#signdigitalsovereigninfra @SignOfficial $SIGN