i was digging through the SIGN documentation again, and it’s one of those projects that feels deceptively simple until you start mapping out the operational dependencies. you’ve got schemas for attestations, a way to map those to identities, and a distribution engine to handle token claims. the surface-level narrative is basically just "airdrops but structured," or "credentials for web3 growth." and honestly, that’s useful enough. but it’s not really the full picture.
but that’s not the full picture.
the deeper implication here is that SIGN is trying to turn "claims about users" into a shared piece of infrastructure. most identity or credential projects end up as walled gardens—you use their SDK, you sign in with their wallet, you get their badge. but if you’re building "global infrastructure," you have to solve for the scenario where a third party—who has no relationship with the SIGN team—decides to trust an attestation and build an app around it. that’s where the engineering gets messy, because trust isn’t just a boolean; it’s a stack of assumptions about who issued the data, what schema they used, and whether the claim is still relevant.
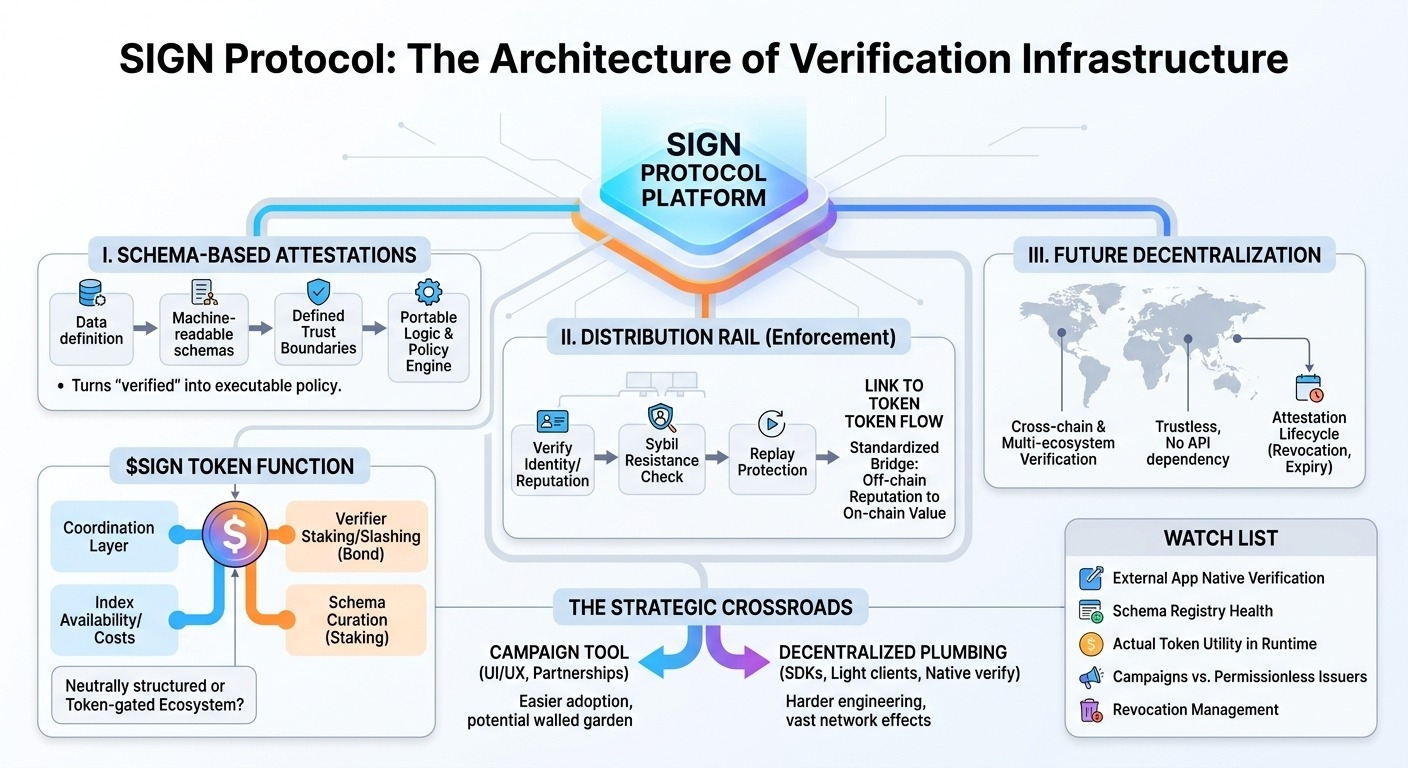
the first core mechanism that makes this interesting is the schema-based attestation layer. it sounds dry, but schemas are the actual trust boundary. if you don't have a rigid way to define what "verified" means in a machine-readable way, then every integration becomes a bespoke mapping exercise. SIGN seems to be betting that if you provide a stable registry for schemas, you stop being just a credential database and start being a policy engine. an app can say "only wallets with this schema, issued by this set of actors, can claim this reward," and that logic stays portable.
the second mechanism is the distribution rail. this is the part that gets lost in the marketing, because people think "distribution" is just a UI for clicking 'claim.' in reality, it’s a high-stakes enforcement layer. it has to handle sybil resistance, replay protection, and the ability to update eligibility rules on the fly without breaking the user experience. SIGN’s ability to link these claims to token flows means they aren't just recording facts; they’re executing policy. and that’s where it gets interesting, because the protocol is effectively creating a standardized bridge between offchain reputation and onchain value.
some of this is live right now—the attestation lifecycle, the schema registry, and the claim flow are all production-tested components. you can see them working in real-time. the future promise, though, is the "global" aspect. that implies a world where these attestations are verified across chains, ecosystems, and apps without needing to ping the SIGN protocol API every single second. that level of trustless decentralization is the phased part, and it’s still very much a work in progress.
then there's $SIGN. i’m still trying to figure out where the token sits in the stack. if the protocol is truly neutral infrastructure, the token needs to serve a specific function—maybe coordinating verifiers or managing the cost of indexing and availability. but i have a standing concern with protocols that start as "neutral infrastructure" and then get squeezed by their own token incentives. is the token required for the system to function, or is it just a coordination layer that could have been a DAO-managed fee schedule? i don't have an answer yet, but the friction between "public utility" and "token-gated ecosystem" is always the place where these things start to show their age.
my open question is whether the team wants to be the "plumbing" for the whole ecosystem, or if they’re content being the best-in-class tool for teams running campaigns. those are two very different business and technical paths. if they stay the latter, they win on product quality; if they go for the former, they win on network effects. it’s rare to successfully do both.
watching:
- whether external apps verify SIGN attestations natively, without relying on SIGN-hosted APIs or frontends
- the evolution of the schema registry—does it stay lean, or does it become a graveyard of dead schemas?
- what $SIGN actually does in the runtime beyond governance
- the ratio of “partner campaigns” vs “independent, permissionless issuers” on the network
- how revocation is handled when an issuer goes offline or gets compromised across different chains
$SIGN #signdigitalsovereigninfra @SignOfficial