@SignOfficial #SignDigitalSovereignInfra
I was up late last night going through the documentation of Sign Protocol, not quickly scanning it but actually reading it line by line. At some point the technical details stopped being the interesting part. A different question kept popping into my head, and once it appeared I couldn’t really ignore it anymore.
What exactly is Sign selling?
Not what they are building. What they are selling.
Because there is a big difference between a project that sells trust and a project that sells operational efficiency. The adoption path, the users who care, and even the way value grows are completely different.
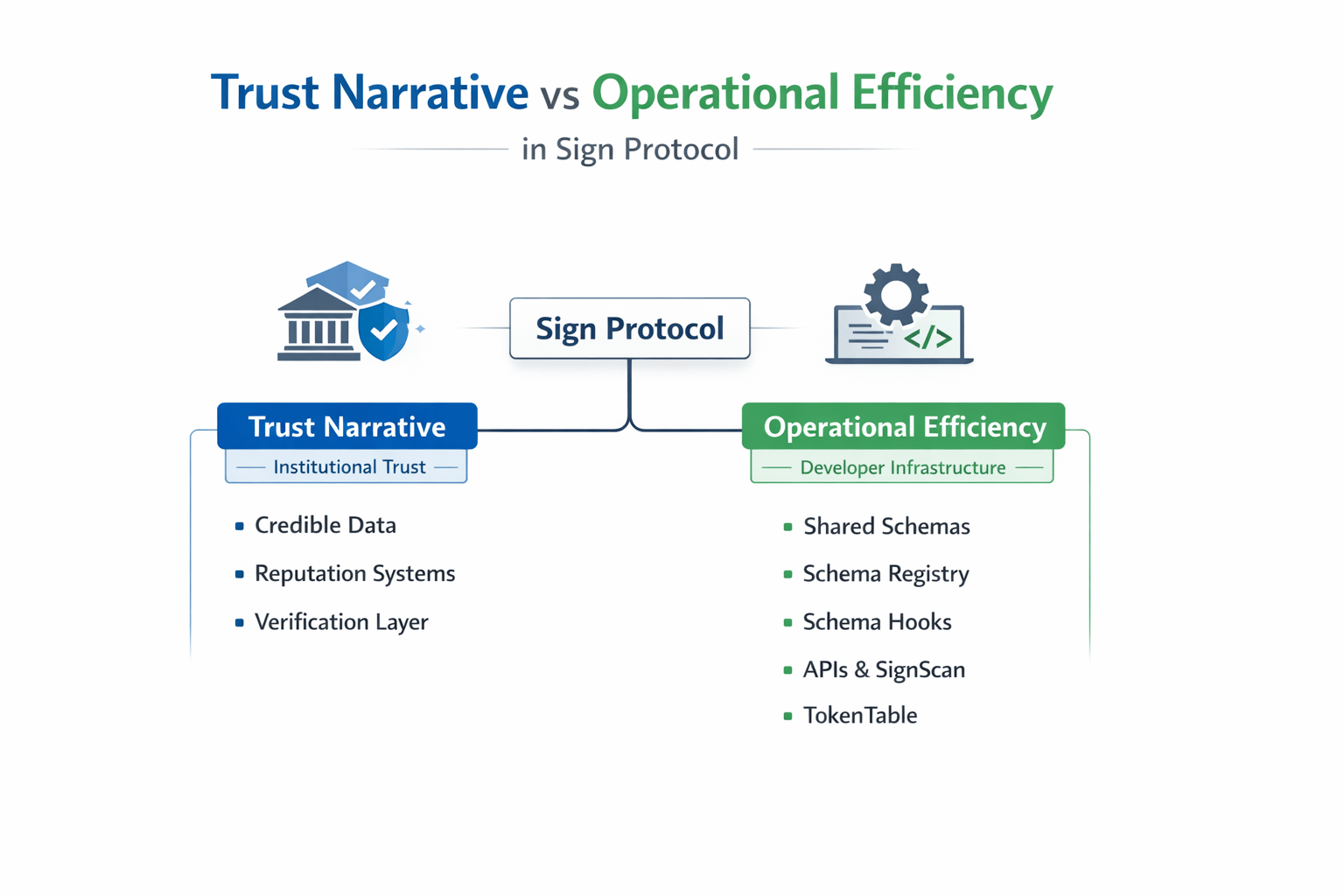
A trust narrative speaks to institutions and end users. It tells a simple story: data becomes more credible, claims become easier to verify, and reputation becomes harder to fake. People like this story because it feels important. It sounds like infrastructure for a more reliable internet.
But trust is a strange thing to sell. It is emotional. It is hard to measure. And it usually takes a long time before people fully believe it.
Operational efficiency is a different kind of pitch. It is aimed directly at developers and teams building products. The argument is simple: if you use this system, you don’t have to build certain things yourself.
No need to design your own verification logic.
No need to maintain custom data structures.
No need to constantly patch integrations between systems.
It is not philosophical. It is practical.
When I went through the Sign documentation with that lens, something became pretty clear. The public narrative often leans toward the trust story, but the actual design of the protocol feels very focused on operational efficiency.
Take the schema registry for example.
On the surface it sounds like a trust layer for structured data. But when you look closer, it behaves more like developer infrastructure. Instead of every application inventing its own format for credentials or attestations, teams can adopt schemas that already exist. That removes a lot of small but annoying coordination problems between systems.
It sounds simple, but anyone who has worked with APIs or data formats knows how messy those conversations can get.
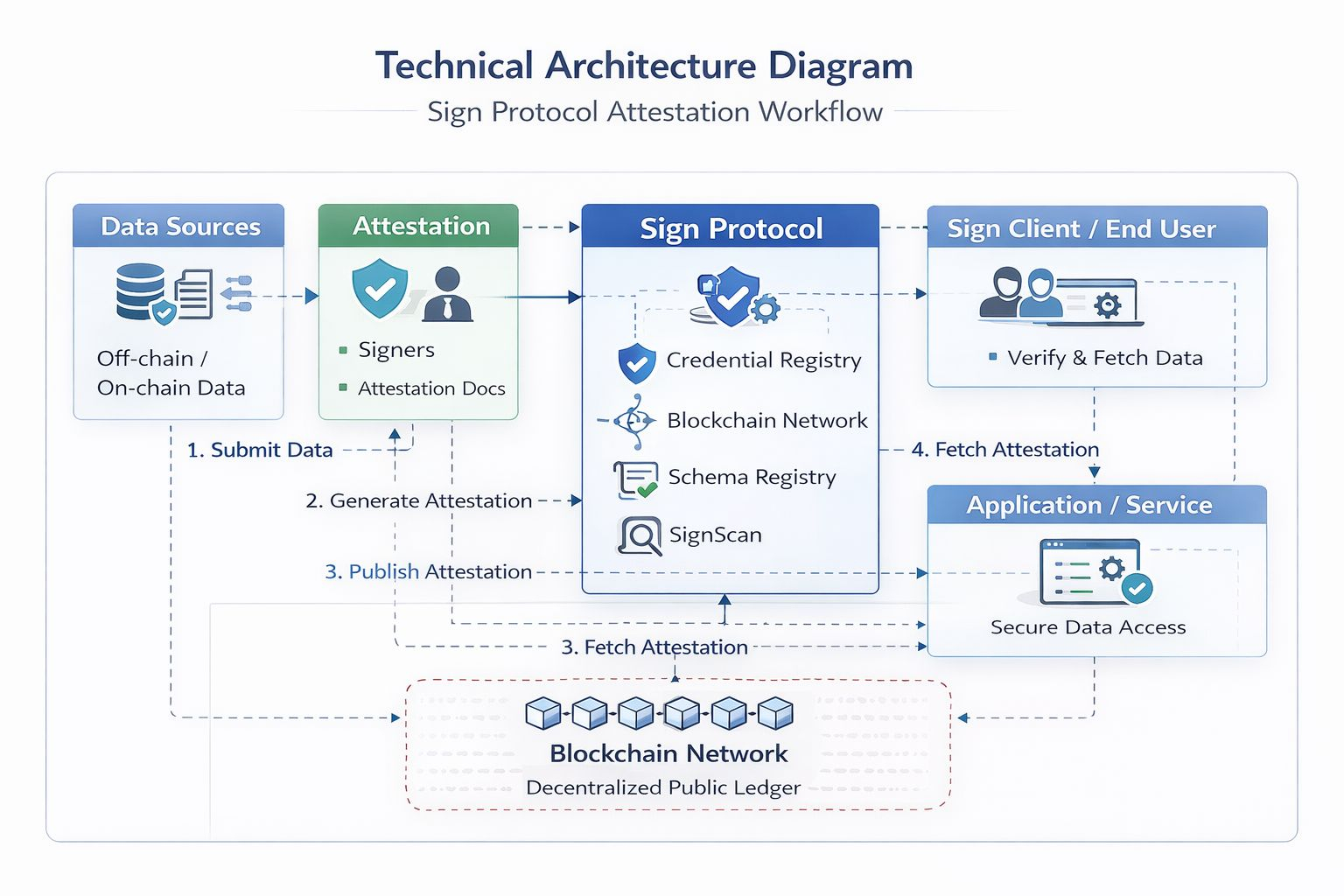
Then there are SpIDs.
At first I thought of them as just another identifier system, but the more I read the more their purpose made sense. They give every issuer, schema, and entity a stable reference that works across chains. Developers don’t have to constantly map addresses between networks or rebuild references when something moves.
Those small details might not excite investors, but they matter a lot when you are actually building software.
Schema hooks are where the operational side of Sign becomes even more obvious.
Before hooks existed, automation around attestations usually meant building off-chain infrastructure. Event listeners, trigger scripts, scheduled checks. Every team ended up creating its own version of the same machinery.
Schema hooks move that logic directly into the schema layer.
When an attestation appears, updates, or disappears, predefined code can run automatically. That means verification, permissions, or rewards can happen without an external system watching everything in the background.
For developers, that removes a surprising amount of operational overhead.
Then there is TokenTable, which might be the most practical example of this whole idea.
Token distribution sounds straightforward until a project actually has to manage vesting schedules, cliffs, allocations, and multi-chain deployments. Suddenly it becomes a mix of smart contracts, spreadsheets, and internal tools.
TokenTable turned that into a single product. Projects use it because it simplifies something they would otherwise have to build and maintain themselves.
That kind of adoption doesn’t come from storytelling. It comes from convenience.
The same pattern shows up in SignScan and the APIs. Having REST and GraphQL endpoints might not sound exciting, but those are the kinds of tools developers rely on when integrating infrastructure into real products.
It is another signal that the team is thinking about daily workflows, not just high-level narratives.
What I find interesting is that these two stories about Sign exist at the same time.
On one side there is the trust layer narrative, which is easier to explain to the broader market. On the other side there is the operational efficiency layer, which quietly makes developers’ lives easier.
Sometimes those narratives align. Sometimes they move at different speeds.
Investors often respond faster to the trust story. It feels bigger and more visionary. But long-term value usually grows when developers start relying on the system because it removes friction from their work.
That is the part I am watching closely.
Real adoption will show up when protocols begin using schema hooks and shared schemas in production environments, not just as examples in documentation. When that happens, Sign stops being an idea and starts becoming infrastructure.
Until then, it sits somewhere in between a narrative and a toolset.
Personally I still hold a small position from the airdrop and I have been looking into the OBI program as well. But I am not rushing to add more yet. I want to see whether operational usage starts growing beyond the obvious cases like KYC or simple credential attestations.
If enough builders start treating Sign as a shortcut instead of an experiment, the protocol could quietly become a very sticky layer in Web3.
If that momentum takes too long, the trust story alone may not be enough to carry everything.
So I keep coming back to the same simple question.
When you look at Sign, do you see a system for building trust, or a tool that makes developers’ work easier?
Depending on the answer, the future of the protocol might look very different.
