Sometimes when you look closely at the digital world, especially the strange, chaotic universe we call Web3, you begin to notice something slightly uncomfortable. For all the talk about decentralization, autonomy, permissionless access and all those grand words that float around crypto discussions, the actual systems underneath often look… improvised. Not malicious, not necessarily broken, but improvised. Airdrops calculated through scripts written the night before distribution. Community contributions tracked in spreadsheets. Eligibility decisions based on snapshots that freeze a moment in time and hope nothing complicated happened before or after. It works, technically. Until it doesn’t.
And when it breaks, it breaks quietly. Some users receive rewards they probably shouldn’t have. Some users who spent months contributing get nothing. Bots slip through filters. Teams scramble to patch things. The ecosystem moves on. No one writes a postmortem because everyone knows the uncomfortable truth: verification infrastructure in Web3 has been fragmented from the beginning.
That’s the context where something like Sign Protocol starts to appear on the radar, and to be honest the first instinct should probably be skepticism. Crypto has produced an entire museum of “identity solutions,” “reputation layers,” and “trust protocols.” Most of them sounded brilliant in theory and faded into obscurity once reality arrived. So when another system claims to reorganize verification logic, the natural reaction is to lean back slightly and ask the simple question: what exactly is different this time?
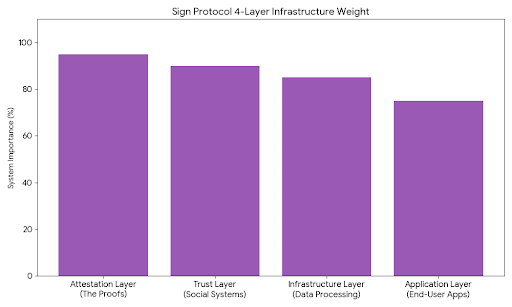
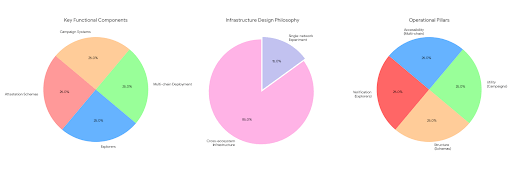
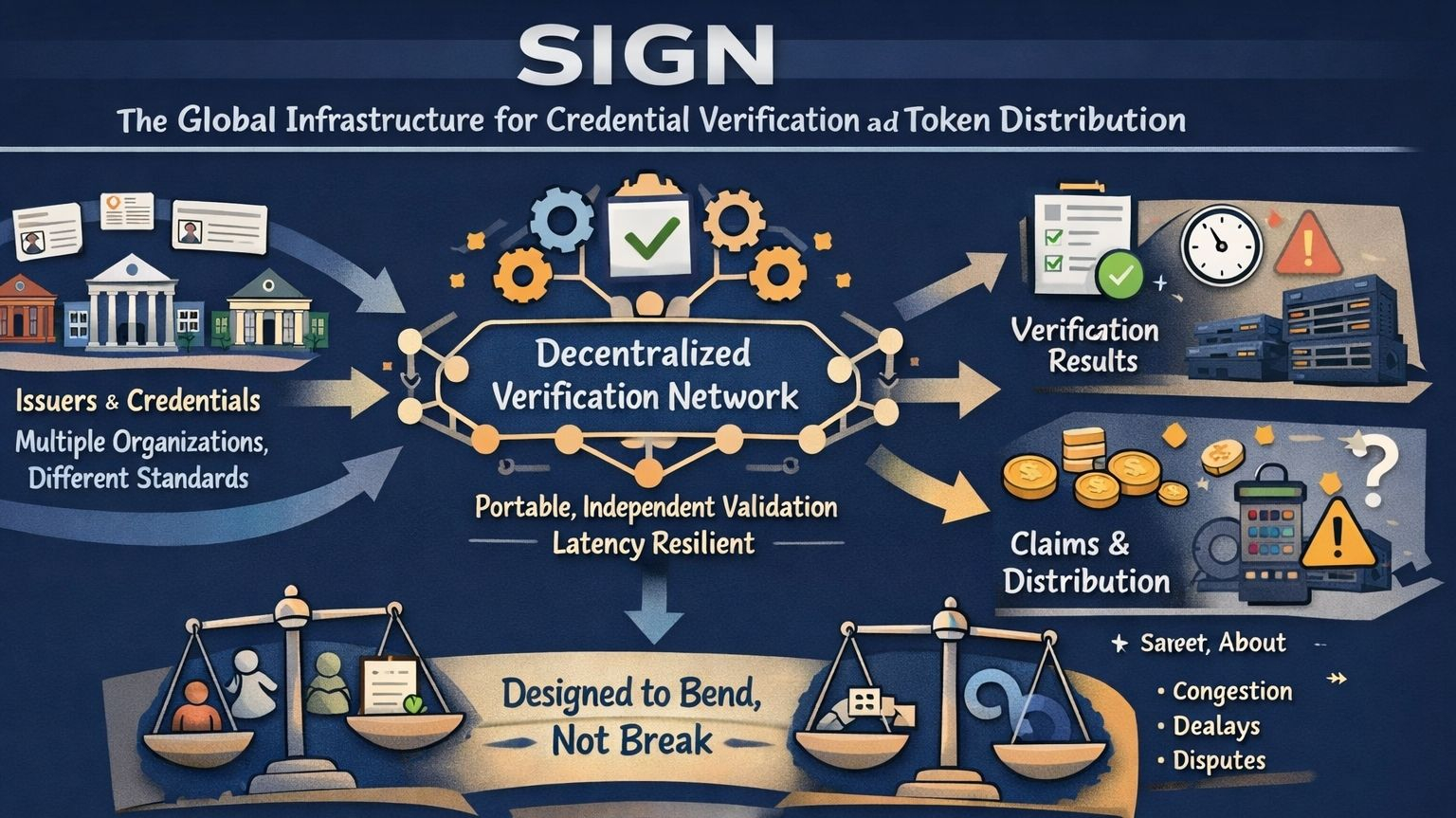
The answer, at least conceptually, is a shift in what the system chooses to record. Most platforms store data. Sign Protocol records decisions. That distinction seems subtle at first, almost too subtle to matter, but the more you sit with it the more interesting it becomes. Instead of maintaining giant databases that attempt to describe users and their actions, the protocol focuses on cryptographic attestations. Statements. Claims. Proofs that an event occurred or that an entity recognized something as valid. A wallet completed a task. A contributor participated in governance. A user qualifies for a reward distribution. Each of those becomes a signed credential, something that can be verified independently rather than trusted implicitly because a platform says so.
In theory, this turns verification into something closer to infrastructure than application logic. The difference is philosophical as much as technical. A project no longer needs to own the entire verification pipeline from beginning to end. Instead, it can rely on attestations issued by other entities, systems, or communities. Credentials start behaving like portable proofs rather than isolated records trapped inside one ecosystem.
But theory is cheap in crypto. Execution is where the conversation gets real.
And to be fair, Sign Protocol does seem to have moved beyond the purely conceptual stage. Attestation schemas exist, which define how credentials are structured. Explorers exist, which allow those attestations to be inspected and verified. The protocol has been deployed across multiple chains, suggesting that it is designed to function as cross-ecosystem infrastructure rather than a single-network experiment. Campaign systems using these credentials have also appeared, where eligibility for participation or rewards is determined through attestations rather than manual data aggregation.
That doesn’t mean the system is solved. Not even close.
Because building a global verification layer introduces pressures that most crypto protocols rarely experience. Verification touches identity. Identity touches regulation. Regulation touches governments. And governments have a long history of approaching decentralized systems with caution, especially when those systems begin interacting with financial incentives or cross-border participation.
Imagine a credential issued in one digital ecosystem suddenly being recognized across multiple platforms. At that point it begins behaving like a form of reputation capital. Something that carries value beyond the original environment where it was created. Now imagine that credential interacting with compliance frameworks, financial rewards, or governance power. The moment those pieces connect, the conversation shifts from purely technical architecture to institutional negotiation.
And institutions move slowly.
There is also the question of scale, which tends to hide quietly in early-stage systems before becoming the central challenge later. Credential infrastructure sounds elegant when the network processes thousands of attestations. It becomes something entirely different when millions of users attempt to verify eligibility during a large distribution event. Suddenly the system must behave less like a lightweight protocol and more like a global verification network capable of handling intense bursts of activity without collapsing under its own complexity.
That’s where another subtle tension appears: the balance between efficiency and transparency. On-chain attestations provide strong guarantees. Every credential exists as an immutable record that anyone can verify. Trust becomes mathematical rather than social. But that level of transparency carries a cost. Literally. Writing large volumes of data directly onto blockchains can be expensive, and as activity scales those costs multiply quickly.
Off-chain verification systems offer a tempting alternative. They reduce cost, increase speed, and allow systems to process large datasets more efficiently. Yet the moment verification moves away from the chain, some of the transparency disappears with it. The system becomes dependent on operators, infrastructure providers, or external logic that must itself be trusted. It’s not necessarily a flaw. It’s a trade-off. And infrastructure design is often a long series of trade-offs rather than perfect solutions.
Then there is the quiet paradox that emerges whenever standards begin to form. Standardization is incredibly powerful. It simplifies integration. It reduces friction between systems. It allows developers to build applications without reinventing the same mechanisms again and again. But standards also shape behavior. Once a verification schema becomes widely accepted, communities begin adjusting their activities to fit within that framework. Participation becomes structured around what the system recognizes as valid.

This is not unique to crypto. The internet itself is built on protocols that quietly define how information flows. Payment networks rely on standards that determine how transactions are processed across banks and institutions. Standards create efficiency, but they also create boundaries.
And that raises an interesting thought about credential systems in general. If verification becomes programmable, then the rules defining verification become extremely influential. Whoever designs those schemas indirectly shapes how participation, reputation, and eligibility are measured across digital environments.
That might sound dramatic, but infrastructure has always worked that way.
Still, the technology itself is only half the story. The deeper challenge sits in the messy space where technology meets human incentives. Cryptographic attestations can prove that a statement was signed by a particular entity. They cannot guarantee that the entity acted honestly when issuing the statement. Reputation systems can track behavior, but they cannot eliminate manipulation entirely. Every verification framework eventually encounters what could be called the social grey zone, where incentives, governance, and trust intersect in unpredictable ways.
Dilse, this is where things become fascinating rather than purely technical.

Because what Sign Protocol is really experimenting with is not just credential verification but programmable accountability. A world where digital actions generate verifiable statements that travel across systems. A world where contributions, participation, and eligibility become portable proofs instead of isolated records.
But experiments rarely follow straight lines. Infrastructure evolves slowly, through iteration and friction. Systems break, adapt, and occasionally reinvent themselves in response to pressures that designers never anticipated. Some protocols fade quietly despite brilliant architecture. Others become foundational layers simply because they solve one persistent problem better than anyone else.
So where does Sign Protocol sit in that spectrum right now? Probably somewhere in the middle. Not a finished framework, not a theoretical idea, but an evolving piece of infrastructure testing its assumptions against the unpredictable behavior of real ecosystems.
And maybe that’s the healthiest way to view it. Not as a perfect solution. Not as the final answer to digital identity or credential verification. Just an ongoing attempt to reorganize how trust moves through decentralized systems.

Which leaves a question lingering in the background, one that the community will eventually have to confront. If the future of digital ecosystems relies on programmable credentials and standardized attestations, then who ultimately decides what counts as legitimate proof?
That answer, strangely enough, may matter far more than the technology itself.
@SignOfficial #SignDigitalSovereignInfra $SIGN
