been reading through SIGN’s docs / product stack a bit, and i initially filed it under the usual Web3 bucket: credentials, attestations, maybe some identity-adjacent infra, plus a token to coordinate the network. easy enough to dismiss as another layer trying to clean up airdrops and user verification.
that’s probably how most people see it. SIGN = issue credentials, verify eligibility, distribute tokens, done. the surface-level narrative is pretty straightforward: make trust portable, reduce sybil noise, help projects send assets to the right users. and sure, that’s part of it.
but that’s not the full picture.
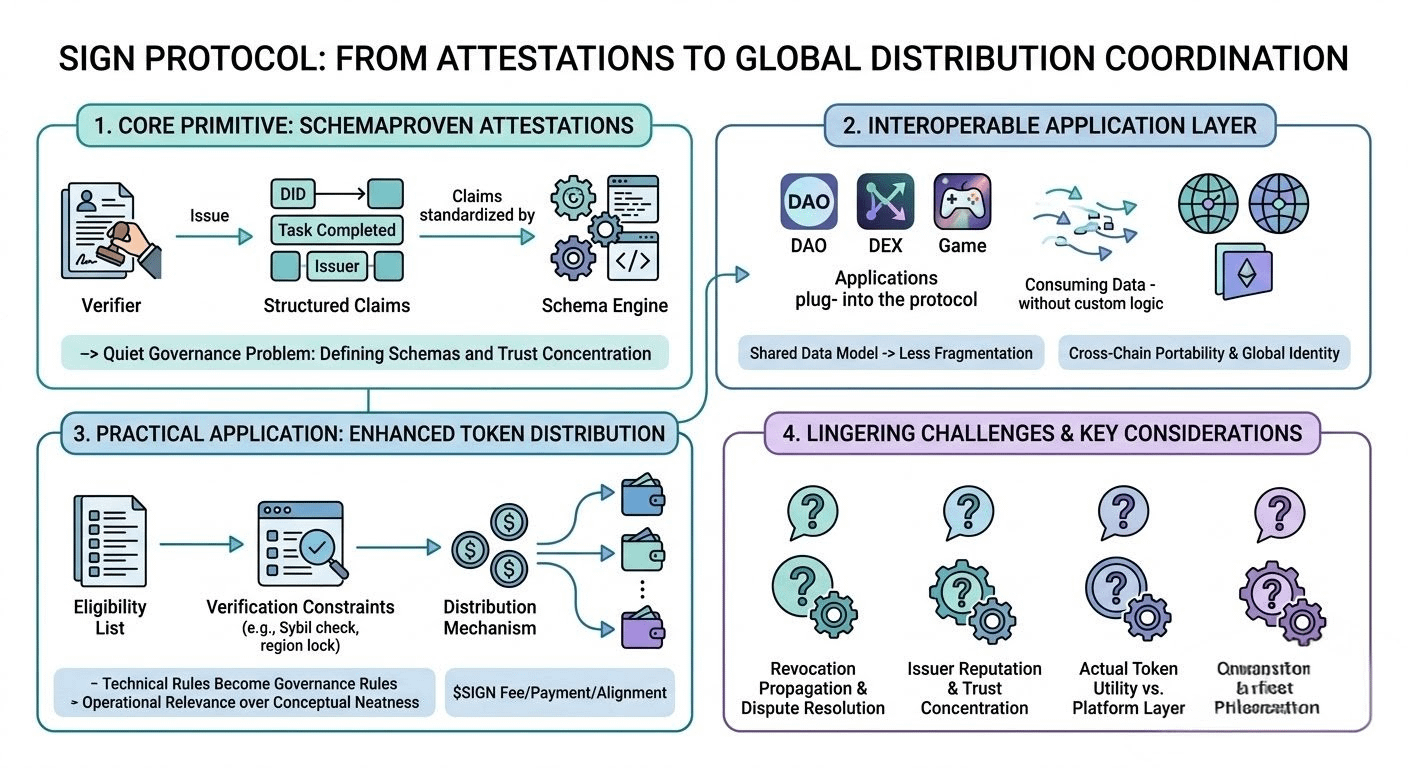
the simple-looking primitive here is the attestation. one entity signs a claim about another entity, maybe onchain, maybe anchored somehow, maybe tied to a schema. sounds boring. but once you take that seriously as infrastructure, it starts acting less like a badge system and more like a coordination layer. not just “this wallet belongs to x,” but “this address completed y task,” “this person passed z verification with issuer n,” or “this account is eligible for a distribution under these exact conditions.” small primitive, bigger implications.
one mechanism that stands out is schema-driven attestations. this is one of those things that feels like implementation detail until it isn’t. if claims are structured under shared schemas, then different apps can consume them without rebuilding custom parsing and custom trust logic every time. that creates a shot at interoperability, or at least less fragmentation. but it also creates a quiet governance problem: who defines the schemas that matter, who upgrades them, and whose attestations become socially accepted enough to be useful? the protocol can be open and still end up with a pretty concentrated trust map.
the second piece is token distribution infrastructure, which honestly may be the more practical side of the whole stack. lots of projects can generate an eligibility list. fewer can execute distribution cleanly across regions, wallets, chains, and anti-sybil constraints without making a mess. SIGN seems to be betting that verification and distribution shouldn’t be separate systems. if credentials feed directly into claims, unlocks, or allocation logic, then the protocol becomes operationally relevant, not just conceptually neat. and that’s where it gets interesting — because distribution is where technical rules become governance rules very fast. one line in an eligibility policy can decide who gets paid and who doesn’t.
there’s also the broader “global infrastructure” angle, meaning not just attestations on one chain but a general layer for credentials and token flows across ecosystems. i get the appeal. identity and reputation are more useful when they travel. but here’s the thing: cross-chain portability usually sounds cleaner in diagrams than in production. issuer trust, revocation, data availability, wallet fragmentation, and privacy expectations all behave differently depending on where and how the attestation is consumed. so calling it global is maybe directionally right, but i suspect the actual work is a lot of adapters and operational glue.
some of this is definitely live now. attestation issuance is real, distribution tooling is real, and SIGN has actual usage instead of just a roadmap. that matters. what feels less settled is the long-term role of $SIGN itself. maybe it ends up as fee/payment/governance/alignment infrastructure. maybe it secures some network function over time. or maybe the useful part of the system is the product and data model, while the token case stays a little thinner than the docs imply. not saying that as a knock, just... i’ve seen that pattern before.
my lingering concern is around revocation and trust concentration. if a credential gets revoked, who notices? if an issuer is compromised, how does that propagate? if a distribution depends on third-party attestations, what happens when users dispute the claim? these are boring questions, maybe, but usually the boring questions are the real system.
watching:
- whether schema standards actually get reused across teams, not just inside SIGN’s own stack
- how revocation / disputes / issuer reputation are handled in practice
- whether token distribution becomes the main adoption wedge, more than “identity”
- what $SIGN is required for versus what is just attached to the platform
- how “global” the infra really gets once cross-chain edge cases pile up#signdigitalsovereigninfra @SignOfficial $SIGN