$SIGN #SignDigitalSovereignInfra @SignOfficial

When I started looking at SIGN, I was mostly focused on schemas and attestations. It made sense. Define the claim clearly, sign it, verify it across systems.
But that only works if every system reads the claim the same way. That’s the part SIGN is trying to fix.
There is a situation where even that model gets tested.
A credential verifies correctly. The issuer is trusted. The schema matches. Everything checks out. Still, the verifier cannot accept it.
Not because the credential is wrong. Because the system needs a network call, and there is no connection.
That’s where things start to break.
A SIGN attestation fixes meaning at issuance. Schema defines the claim. The issuer signs it. That part works.
But it assumes two things at the moment of use:
– the verifier can understand the claim the same way
– the verifier can reach the system if needed
Offline conditions remove the second assumption completely.
Now the verifier has to decide based only on what it has locally.
This is where QR and NFC start to matter.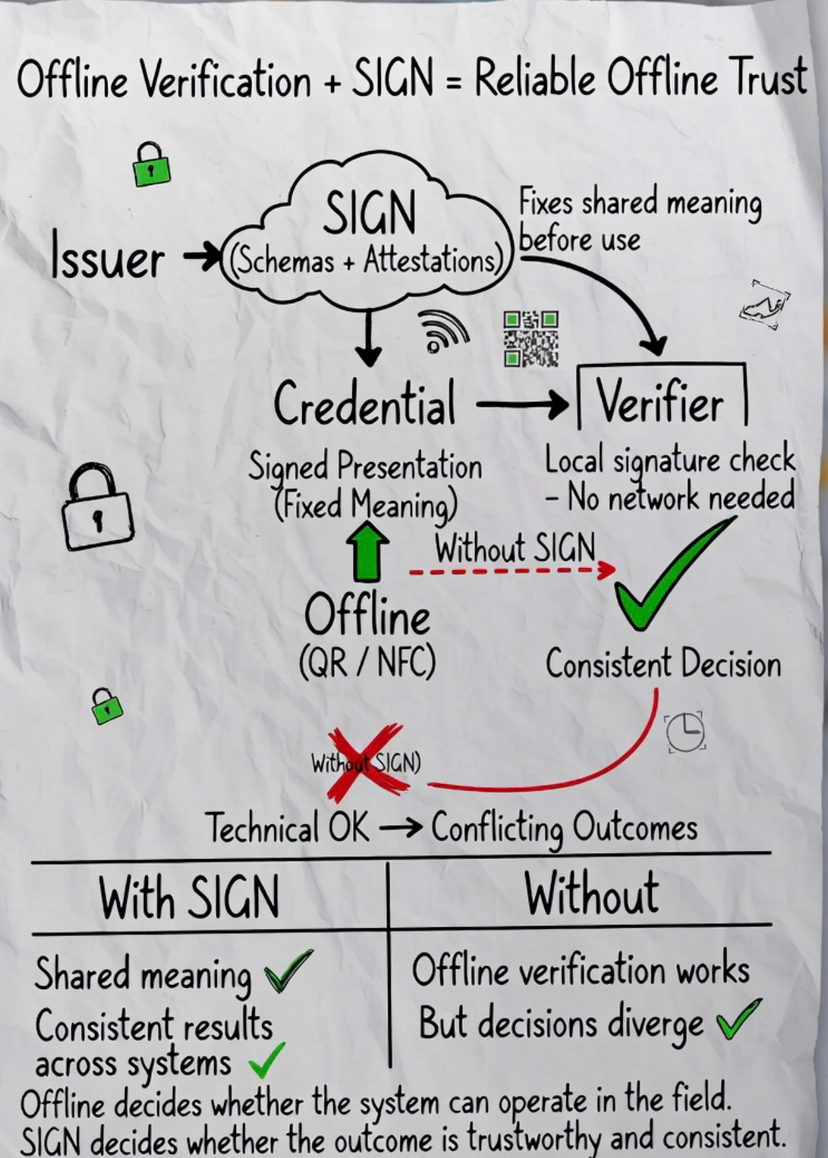
A QR code can carry a signed presentation. An NFC tap can transfer it directly.
The verifier reads it and checks the signature locally.
No dependency on a live connection.
If this works, the credential is usable. If it doesn’t, the system depends on something external.
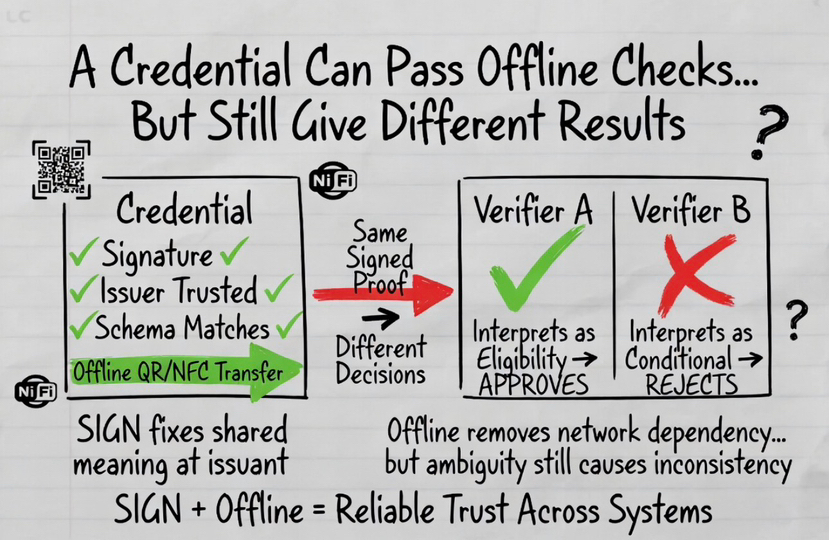
But another problem shows up here.
Even if a credential works offline, it does not guarantee that different systems will interpret it the same way.
One system reads a field as eligibility. Another reads it as conditional approval.
Same credential. Different outcome.
That’s not a connectivity issue. The system is working. It’s just not agreeing with itself.
A simple case: a subsidy credential issued by one authority is scanned offline by two systems. One approves access. The other rejects it based on how it reads eligibility. The proof is the same. The decision isn’t.
This is where SIGN becomes necessary, not optional.
SIGN fixes what the claim means before it is ever used.
So when a verifier reads a credential offline, it is not just checking a signature. It is checking a claim that has already been defined in a shared way.
Without that, offline verification still works technically, but inconsistency just moves closer to the edge.
I’ve seen flows where everything works in testing, but fails in actual use.
The verifier tries to fetch something. It waits. Nothing comes back.
The credential is still valid, but it cannot be used in that moment.
Then another case where offline works, but results don’t match across systems.
In both cases, the issue is different, but the result is the same.
The system cannot be trusted to behave consistently.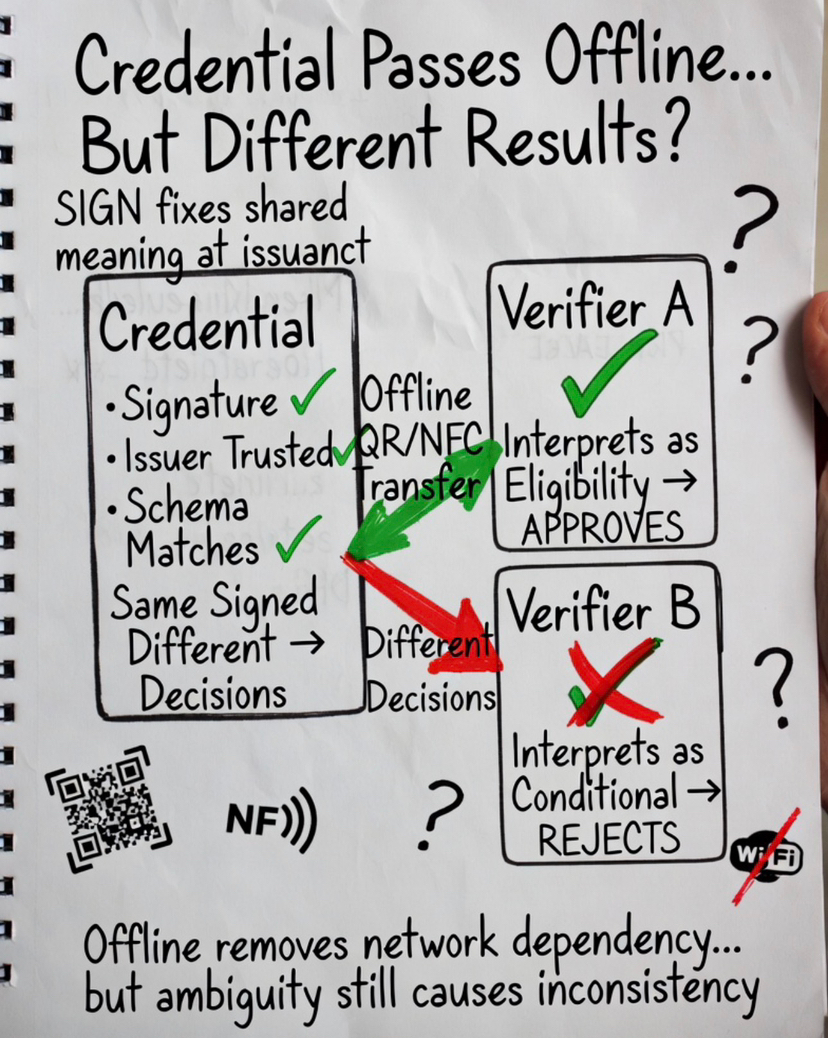
SIGN handles one part of this problem.
It removes ambiguity in what the credential represents.
Offline verification handles another part.
It removes dependency on external systems at the moment of use.
If either one is missing, the system still breaks.
Without offline capability, the credential cannot be used in real conditions. Without SIGN, the credential can be used, but not interpreted consistently.
Border checks and field inspections make this obvious.
The verifier cannot delay the decision. It has to rely on what is available immediately.
That only works if:
– the credential can be verified locally
– the claim inside it is understood the same way
There are trade-offs.
Offline verification means the verifier must already have issuer keys and some state. Revocation cannot always be checked in real time.
So the system shifts complexity, it does not remove it.
The part that changed my view is simple.
A system that depends on connectivity cannot always operate. A system that lacks shared meaning cannot produce consistent outcomes.
Both problems show up quickly in real conditions.
Offline verification decides whether the system can operate. SIGN decides whether the result can be trusted across systems.
Without both, the system either stops
or keeps running and produces conflicting decisions.