sIgn Protocol is not trying to compete with other crypto projects. It is trying to replace how GOVt handle identity, credentials, and digital asset distribution at a national scale. That ambition is backed by real deployments, real money, and a technical architecture that is more sophisticated than most people give it credit for.
TokenTable alone has distributed over 4 billion dollars in digital assets across more than 40 million on chain wallet addresses serving over 200 projects. The national digital ID system in Sierra Leone runs on Sign infrastructure. The UAE Web3 Entrepreneur Program is built on it. The project secured 25.5 million dollars in a strategic round led by YZi Labs and IDG Capital with YZi Labs returning after already leading the earlier Series A. A lead investor doubling down is one of the strongest signals of genuine conviction you can find in this space.
I went through the MiCA regulatory filing and the whitepaper looking to understand the architecture at a technical level. The attestation layer held up well. The zero knowledge proof integration for privacy preserving identity is exactly the kind of cryptographic foundation sovereign infrastructure needs. The three layer SIGN Stack combining the Sovereign Chain with Sign Protocol and TokenTable is a coherent and well thought out design.
Then I found the sequencer section and stopped reading forward.
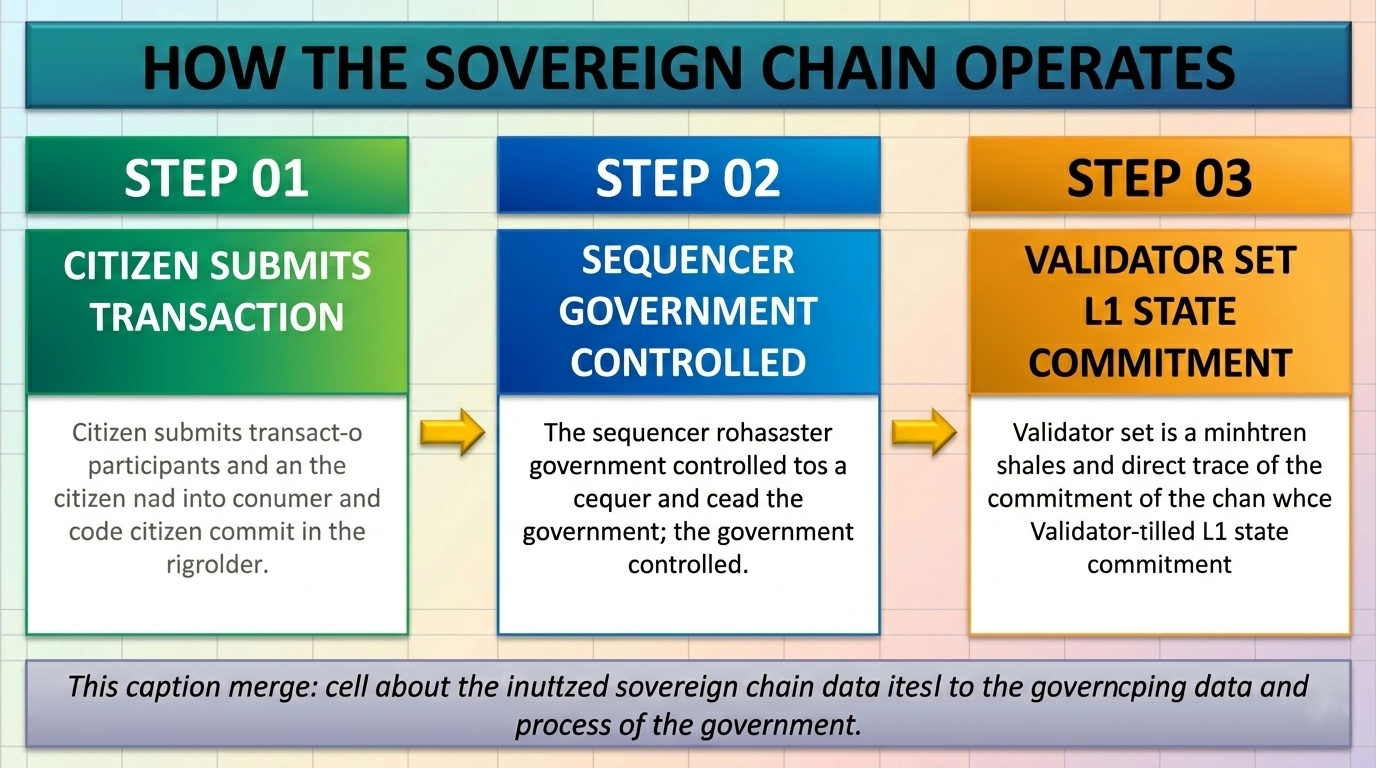
How the sovereign chain actually operates
Under normal conditions the flow is clean. A citizen submits a transaction. That transaction goes directly to the government controlled sequencer. The sequencer orders and batches every single transaction on the chain before anything reaches the validator set for Layer 1 state commitment. Nothing bypasses it. Nothing skips it. The sequencer touches every transaction.
This is an intentional design decision and a correct one. Governments running national digital infrastructure cannot have external parties controlling transaction ordering. A sovereign chain needs sovereign control at every layer and the sequencer delivers that cleanly.
But that same design creates a structural reality the whitepaper never fully addresses. The sequencer is not just the control point of the entire chain. It is also the single point of failure.
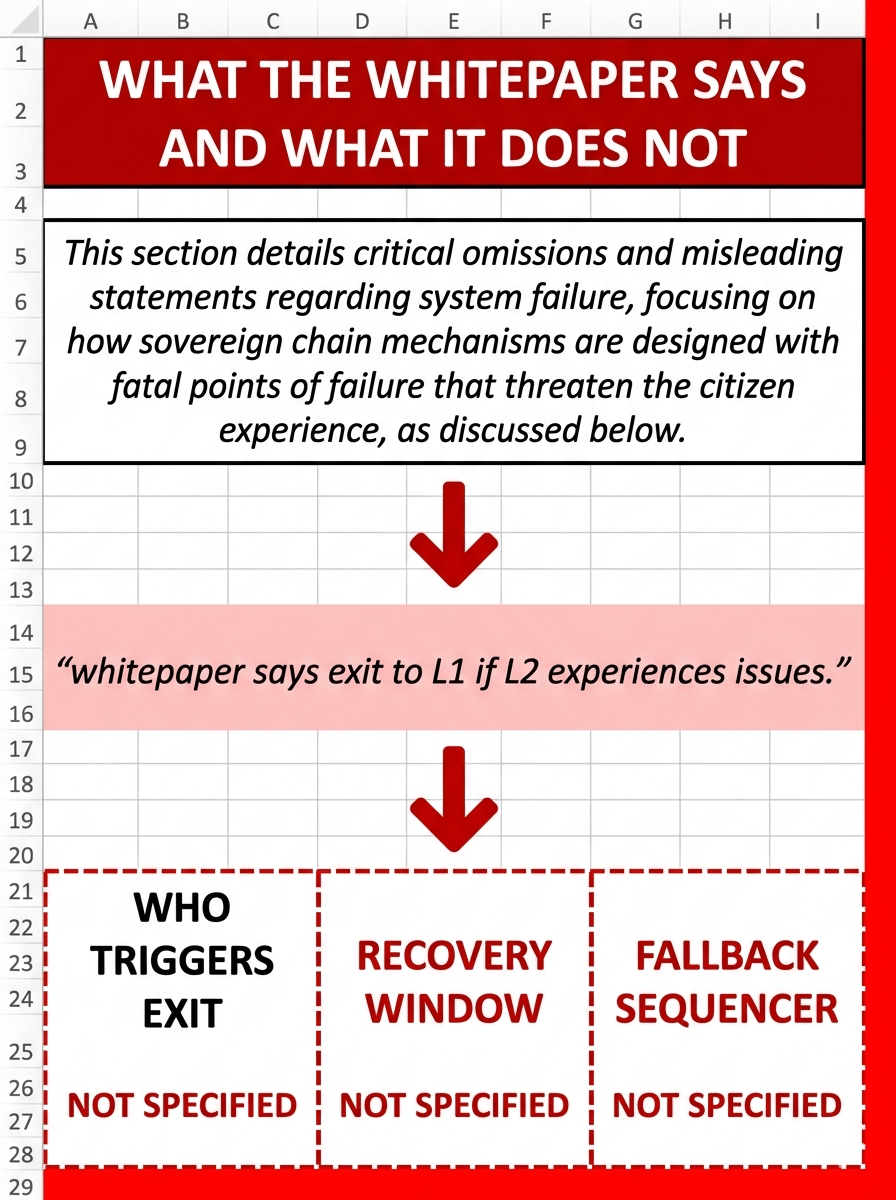
WHAT THE WHITE PAPER SAYS AND WHAT IT DOESN'T NOT
The document addresses sequencer failure in exactly one sentence. It says to exit to L1 if the L2 experiences issues. That is the entirety of the contingency documentation as written in the filing.
Three questions come out of that sentence immediately and none of them have answers anywhere in the document.
First, who actually triggers the L1 exit. Is it the government entity operating the sequencer. Is it a validator node that detects the failure automatically. Is it an automated on chain rule that fires when a defined threshold is breached. The whitepaper does not say. In a real failure under pressure that ambiguity becomes a second crisis layered on top of the first one. While decision makers argue about who has authority to act, citizen transactions remain completely frozen.
Second what is the defined recovery window. How many minutes or hours does a citizen wait before the fallback protocol activates. National infrastructure operates on service level agreements. Banks publish them. Telecoms publish them. Government digital systems require them. The sIgn whitepaper offers no timeline anywhere in the document.
Third, is there a fallback sequencer already standing by. If the primary government sequencer goes offline is there a hot standby ready to take over transaction ordering immediately or does the entire chain halt until the original is restored manually. The document is completely silent on this point.
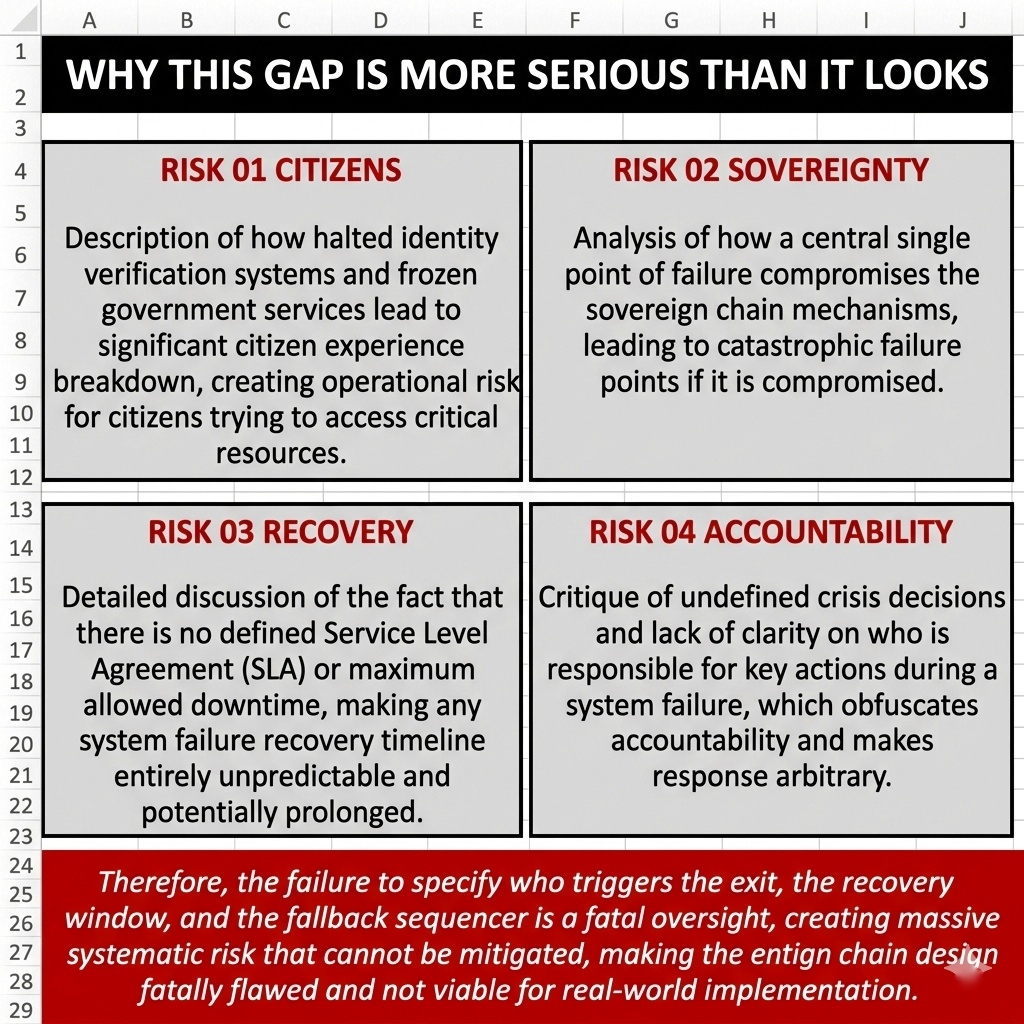
why this gap is more serious than it looks
The sequencer centralization problem is documented across the entire Layer 2 ecosystem. A major cloud outage stress test showed that nearly all Layer 2 systems running centralized sequencers failed the live resilience test at the same time. The lesson drawn was that operational decentralization matters as much as protocol decentralization. A mathematically elegant consensus mechanism still goes down when one server stops responding.
siGn Sovereign Chain runs the same model by design but the stakes are categorically different. When a public Layer 2 goes down crypto native users lose access to an application for a few hours. When a sovereign chain running a national digital ID system goes down citizens cannot verify their identity, cannot access government services, cannot receive benefits, and cannot complete legally binding transactions.
Sign has stated a goal of reaching 50 million people in the first deployment year. The majority of those 50 million will not know what a sequencer is. They will only know that the government service they needed today is not working.
This is entirely fixable. Threshold signatures distributed across multiple authorized government entities would define who triggers the L1 exit. A defined SLA window written into deployment contracts would give citizens a guaranteed maximum downtime commitment. A hot standby sequencer would eliminate the single point of failure structurally.
Every government evaluating Sign infrastructure for national deployment will ask the same three questions before signing any contract. Who triggers the exit. What is the recovery window. Is there a fallback sequencer. Answering those questions in a clear public technical document would not create doubt about Sign. It would eliminate the last serious technical objection standing between Sign Protocol and the scale it is clearly building toward.
That is what infrastructure built for governments actually looks like when it is designed to last.