Most people never question identity systems because they feel smooth on the surface. You upload your documents, get verified, and move on. It feels normal, almost invisible. But if you slow down and really think about it, something feels off. Why do you have to prove the same thing again and again across different platforms? Why does every system need its own copy of your data? And more importantly, once you submit that data, who actually controls it? That’s the part most people don’t stop to consider. Identity today isn’t just about verification. It’s about duplication, exposure, and a quiet transfer of control that happens every time you click “submit. The way modern systems are built follows a predictable pattern. You provide your information, the platform stores it, and then it verifies it through some authority. This process repeats everywhere, from financial apps to government services to simple online registrations. At first glance, it looks efficient, but underneath, it creates a structure where your identity is constantly being copied and stored across multiple databases. Each copy becomes a new risk, and each system holding your data becomes another point of potential failure. That’s why data breaches keep happening at scale. It’s not just a security problem. It’s a design problem. Identity is not failing because it’s hard to verify. It’s failing because it’s being handled in a way that multiplies exposure over time. This is where Sign Protocol begins to change the conversation in a meaningful way. Instead of focusing on storing identity, it focuses on proving identity without repeatedly exposing it. At the center of this approach are attestations, which are essentially verifiable, cryptographic proofs about you. These proofs are issued once by a trusted entity and can then be reused across different platforms without requiring you to resubmit your raw data every time. That changes the flow completely. Instead of sending your information again and again, you present a proof, and the system verifies that proof. It’s a subtle shift, but it restructures how identity moves across systems. What makes this powerful is that it flips the traditional model. In most systems today, platforms own your data. With Sign Protocol, you own the proof of your identity. That distinction matters more than it seems. When platforms store your data, they control access, usage, and retention. When you hold the proof, you control how and when it is used. Systems no longer need to collect everything. They only need to verify what is relevant. This reduces friction, but more importantly, it reduces unnecessary risk. Identity stops being something that is scattered everywhere and starts becoming something that is selectively shared. Another important layer is how trust itself is handled. In traditional systems, trust is often informal and assumed. A document is accepted because it looks valid, or an institution is trusted because it always has been. These assumptions are rarely visible, and they are even harder to audit. Sign Protocol changes that by making trust explicit and programmable. Every attestation clearly defines who issued it, what it represents, and who is allowed to verify it. This turns trust into something structured instead of something implied. It becomes transparent, trackable, and verifiable without relying on hidden relationships or outdated assumptions. This also changes how privacy is experienced. Most systems claim to protect privacy, but still require users to share more data than necessary. Over time, that data accumulates across different services, often without the user fully realizing where it ends up. Sign Protocol introduces a different approach by allowing selective disclosure. Instead of revealing everything, you only share what is required for a specific interaction. You can prove eligibility without exposing full identity, confirm compliance without sharing full documents, and verify status without unnecessary detail. Privacy stops being a promise written in policies and becomes something you actively feel in how the system works. As this model scales, the impact becomes even more significant. Identity begins to move from being isolated within individual platforms to becoming a shared layer across multiple systems. A credential issued in one environment can be used in another. A proof created for compliance can unlock access to financial services. The boundaries between systems start to blur, and identity becomes more portable without becoming more exposed. This is where Sign Protocol shifts from being just a tool to becoming infrastructure. It creates a foundation where identity, verification, and trust can operate seamlessly across different parts of the digital world. What’s important to understand is that this shift is not just technical. It’s structural. It changes how authority is distributed, how data flows, and how control is maintained. The more systems adopt this model, the more identity stops being something fragmented and starts becoming something unified. And once identity becomes part of shared infrastructure, it becomes much harder to replace or redesign later. That’s why these early decisions matter so much. In the end, the future of identity is not about proving more. It’s about proving smarter, with less exposure and more control. Sign Protocol is pushing in that direction by separating proof from storage, trust from assumption, and identity from centralized ownership. Because the real question is no longer whether you can prove who you are. The real question is whether you control how that proof is used, where it travels, and who gets to rely on it. Right now, most people don’t. But that’s exactly what is starting to change.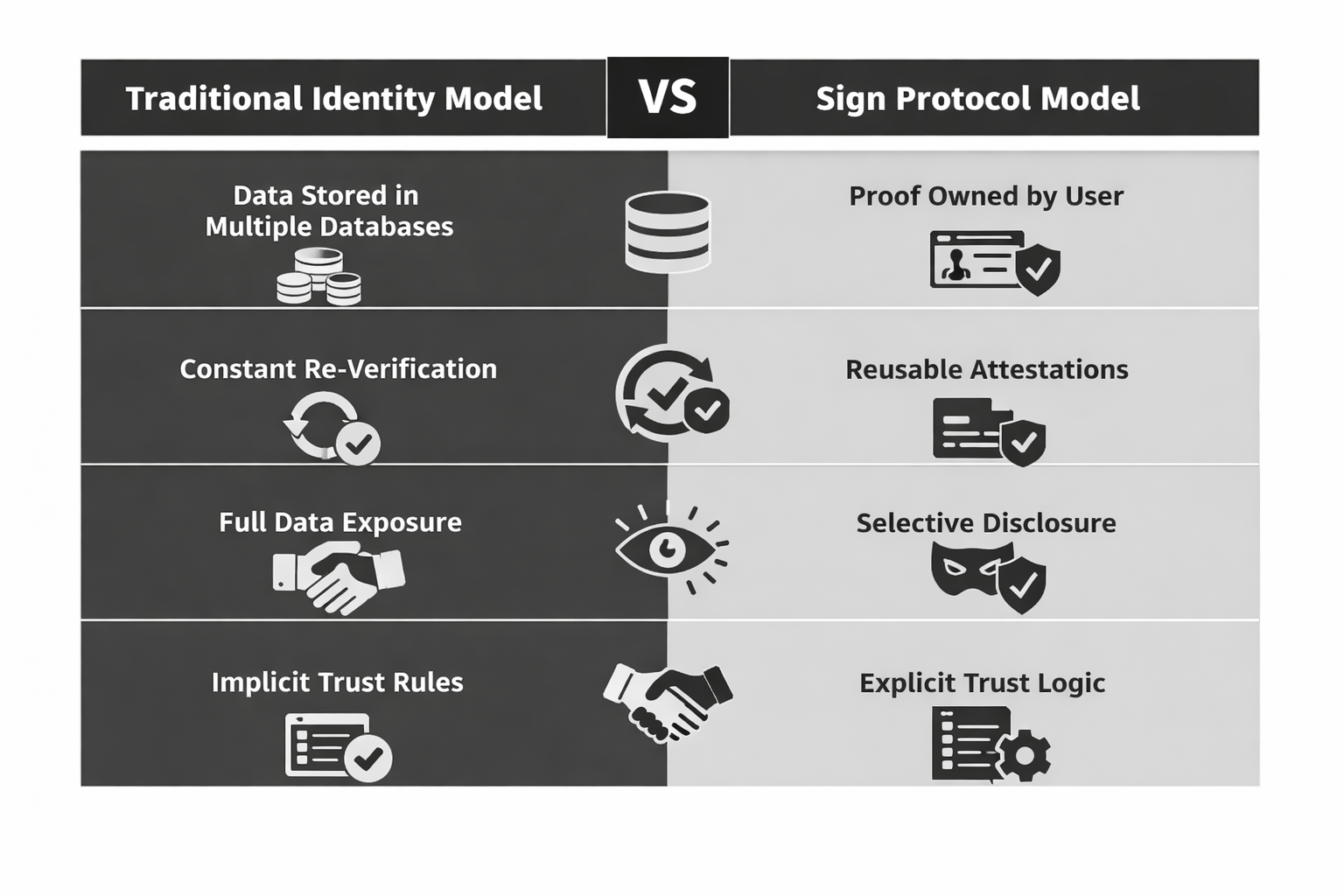
Article
You Don’t Own Your Identity Yet, Here’s What Sign Protocol Is Quietly Fixing
Disclaimer: Includes third-party opinions. No financial advice. May include sponsored content. See T&Cs.
0
23
298
Explore the latest crypto news
⚡️ Be a part of the latests discussions in crypto
💬 Interact with your favorite creators
👍 Enjoy content that interests you
Email / Phone number
