I was reading through SIGN’s litepaper and some of the product docs this week, mostly expecting the usual Web3 identity/airdrop framing. you know the type: attestations, credentials, maybe some anti-sybil angle, then a token layered on top to align the network. at first glance, SIGN fits that pattern almost too neatly.
that’s probably how most people interpret it. a protocol for issuing and verifying credentials, then using those credentials to drive token distributions, access control, maybe a bit of reputation. practical enough, sure. especially for teams that are tired of manually stitching together allowlists, snapshot logic, and claim tools. if that’s all it is, it’s still useful.
but that’s not the full picture.
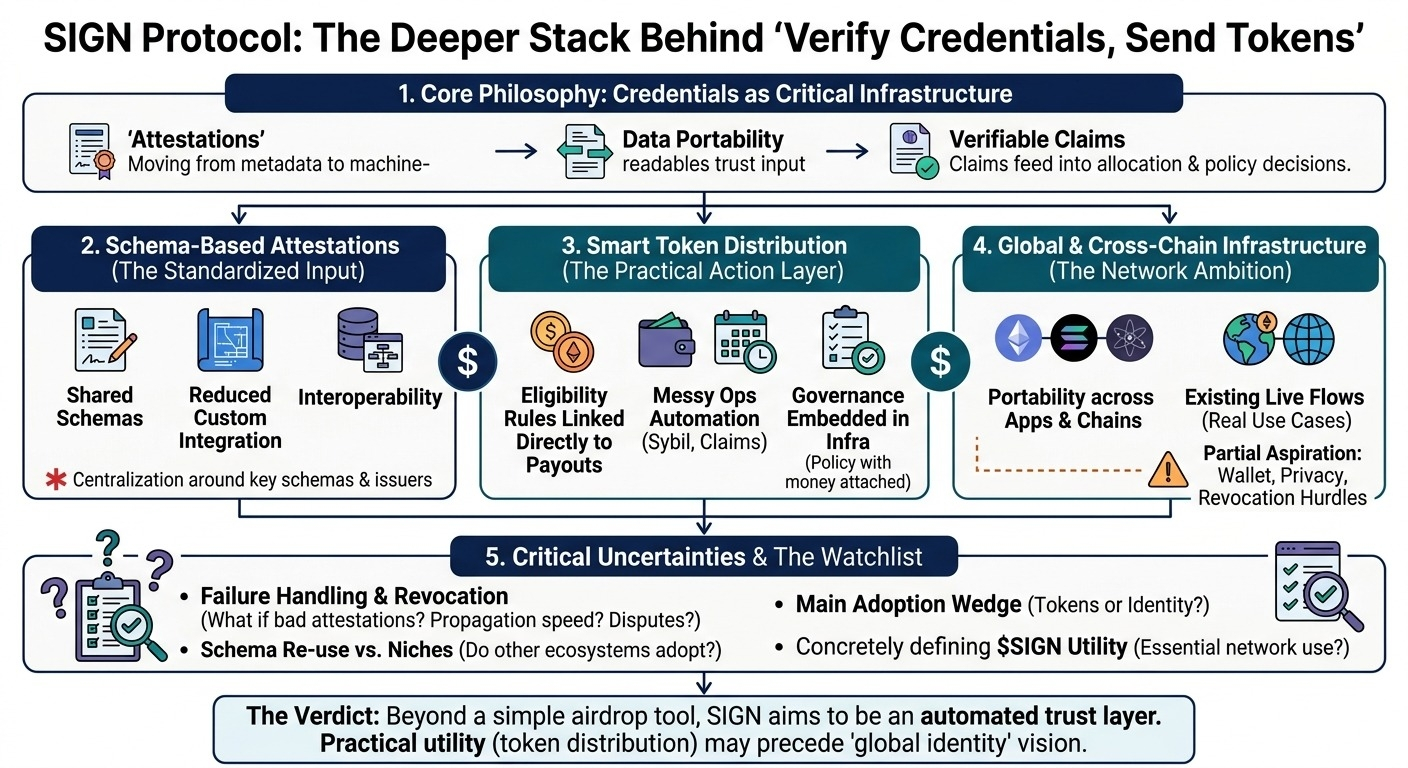
what looks simple on the surface is the attestation primitive itself. one entity signs a claim about another entity. that sounds trivial. but if the claim is structured under a schema, tied to some verification context, and made available across applications, it starts becoming infra instead of metadata. now it can feed into decisions: who is eligible, who has completed some milestone, who belongs to some set, who passed some check with a trusted issuer. and that’s where it gets interesting. the system is no longer just “proof that something happened” — it becomes a machine-readable trust input for allocation and policy.
one core mechanism is schema-based attestations. this feels like boring plumbing, but it’s probably the thing that determines whether SIGN ends up as a useful protocol or just a nice product suite. shared schemas make claims portable and verifiable in a standard way. that reduces custom integration work and gives downstream apps a way to reason about credentials without bespoke code for every issuer. but there’s a catch. standards in open systems tend to harden around a small set of dominant issuers and formats. so even if the protocol is open, the practical trust graph may still centralize pretty quickly. i don’t think that’s a dealbreaker, just something people gloss over when they say “decentralized credentials.”
second is the token distribution layer. this part feels more grounded to me than the broad identity story. lots of teams can define an eligibility rule. fewer can execute token distribution cleanly once edge cases start piling up — multi-wallet users, sybil filtering, regional restrictions, proof of participation, claim expiration, all that messy ops stuff. if SIGN links attestations directly into distribution logic, then it’s solving a real workflow problem, not just creating another registry of claims. but here’s the thing: as soon as credentials affect payouts, governance gets embedded in infrastructure. schema design, issuer selection, and verification thresholds stop being abstract architecture choices and start becoming policy decisions with money attached.
the third piece is the “global infrastructure” framing. i get the ambition. credentials and entitlement data should move across apps and chains instead of being re-created in every silo. that makes sense. some parts of this are already live — there are real attestation flows and real distribution use cases today, not just roadmap slides. but the global piece still feels partially aspirational. portability across chains sounds great until you get into differences in wallet models, settlement assumptions, privacy needs, and revocation handling. so yes, some infrastructure exists today; the universal layer story still feels phased, maybe contingent on adoption by issuers and integrators more than on pure protocol design.
my main doubt is around failure handling. what happens when an issuer makes a bad attestation? how are disputes resolved? who sees revocations first, and how fast do they propagate into distribution systems? these aren’t flashy questions, but they’re probably more important than whatever token utility slide comes later. and on SIGN specifically, i’m still not sure whether the token ends up essential to the network’s operation or mostly adjacent to an already-useful product stack.
watching:
- whether common schemas actually get reused outside SIGN’s immediate ecosystem
- how issuer trust, revocation, and dispute resolution work in production
- whether token distribution, not identity, becomes the main adoption wedge
- what $$SIGN s concretely needed for over time
- whether “global infra” turns into shared standards or just broad deployment across chains
$SIGN @SignOfficial #signdigitalsovereigninfra