i went back through SIGN’s litepaper / docs this week, mostly because i kept seeing it summarized in a very clean way: it verifies credentials, helps distribute tokens, and uses $SIGN as the coordination layer. neat story. almost suspiciously neat. i’ve learned to pay attention when a protocol sounds obvious on the surface, because usually that means the hard part has just been pushed one layer down.
most people, i think, will stop at the simple version. SIGN is an attestation system. issuers create claims, users hold credentials, apps verify them, and then projects use those credentials for airdrops, grants, allowlists, maybe reputation. fair enough. in Web3 terms, that’s already useful. nobody really enjoys building eligibility logic and distribution ops from scratch.
but that’s not the full picture.
the deceptively simple primitive here is the attestation itself. just a signed claim from one party about another. sounds tiny. almost boring. but if the claim is structured well and can be consumed by other systems, it becomes more like programmable trust than mere metadata. not “this wallet has a badge,” but “this address is eligible for a payout because it completed a campaign, belongs to a verified cohort, passed some compliance gate, or holds a credential issued under a known schema.” and that’s where it gets interesting. once credentials become machine-readable inputs into policy, the protocol starts sitting in the middle of real coordination problems.
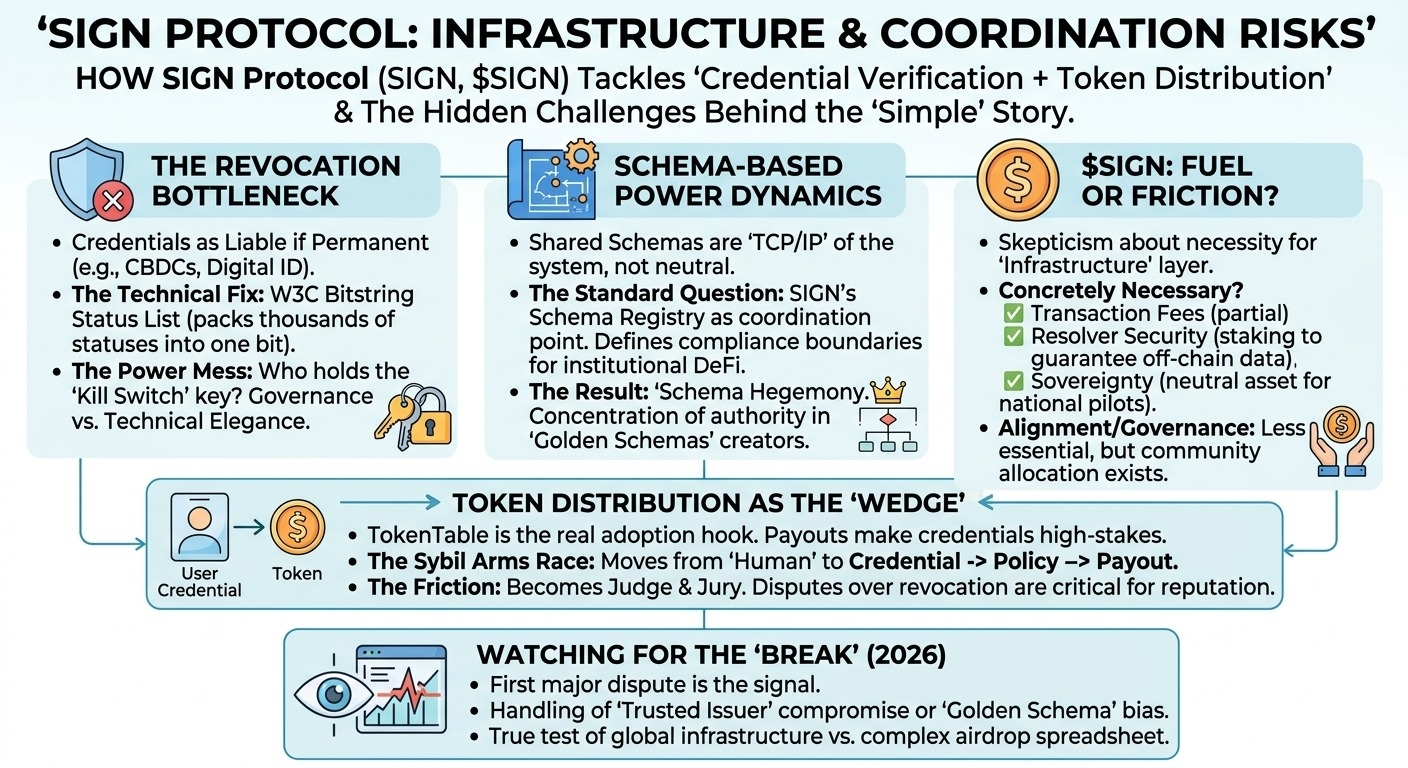
one capability that matters a lot is schema-based attestations. this is the part that feels like implementation detail until you realize it’s probably the main thing determining whether SIGN is infrastructure or just a nice app layer. shared schemas make claims interpretable across products. if multiple systems agree what a credential means, then verification becomes cheaper and more portable. that opens the door to composability. but it also raises a quiet standards question: who defines the schema everyone ends up using, and who gets trusted as an issuer inside that schema? open networks still accumulate defaults, and defaults become power.
second is the distribution layer. honestly, this looks like the most concrete part of the stack right now. “token distribution” sounds simple until you’ve had to operate one. sybil resistance, wallet clustering, region restrictions, claim windows, proofs of participation, failed transactions, user support — it gets ugly fast. SIGN seems to be building the path from credential issuance straight into allocation and claiming, which is much more useful than a generic attestation registry. but here’s the thing: when verification directly influences payouts, the protocol stops being neutral plumbing. every issuer choice, every eligibility threshold, every revocation path has governance implications whether the docs say so or not.
third is the bigger “global infrastructure” framing. i can see why that’s the ambition. credentials shouldn’t be siloed by app, and token entitlement shouldn’t need to be re-derived from scratch every time someone moves ecosystems. some of this is already real — products are live, attestations exist, distributions have happened. that’s important. not just whitepaper land. but the broader cross-chain / universal layer story still feels partly future-tense. portability sounds easy until you start thinking about chain-specific account models, privacy expectations, issuer reputation traveling across networks, and how revocations propagate. global trust systems usually look cleaner in diagrams than in operations.
my main hesitation is around where trust actually accumulates. if a handful of issuers or schema maintainers become canonical, then the protocol might remain technically open while functionally concentrating authority. maybe that’s unavoidable. maybe it’s even desirable in some regulated or high-stakes cases. still, it’s the part i’d want to inspect harder than the token mechanics.
and on $SIGN, i’m curious but not fully convinced yet. i can imagine roles for fees, governance, staking, alignment, maybe some network security assumptions over time. but it’s still not obvious to me whether the token is fundamental to the most useful parts of the system, or mostly attached to them.
watching:
- whether schemas become reusable standards beyond SIGN’s own ecosystem
- how issuer trust, revocation, and dispute handling work when something breaks
- whether token distribution is the actual adoption wedge, more than credentials alone
- what $$SIGN s concretely necessary for in production
- whether “global infrastructure” becomes shared standards or just broad product coverage across chains
@SignOfficial $SIGN #signdigitalsovereigninfra