I was reading through SIGN’s materials again — litepaper stuff, product docs, a few examples of real usage — and i kept coming back to how ordinary the pitch sounds at first. credentials, attestations, token distribution. verify who should get what, then send it. that whole category can feel kind of repetitive now, like every other protocol has some version of “trust layer” in the deck.
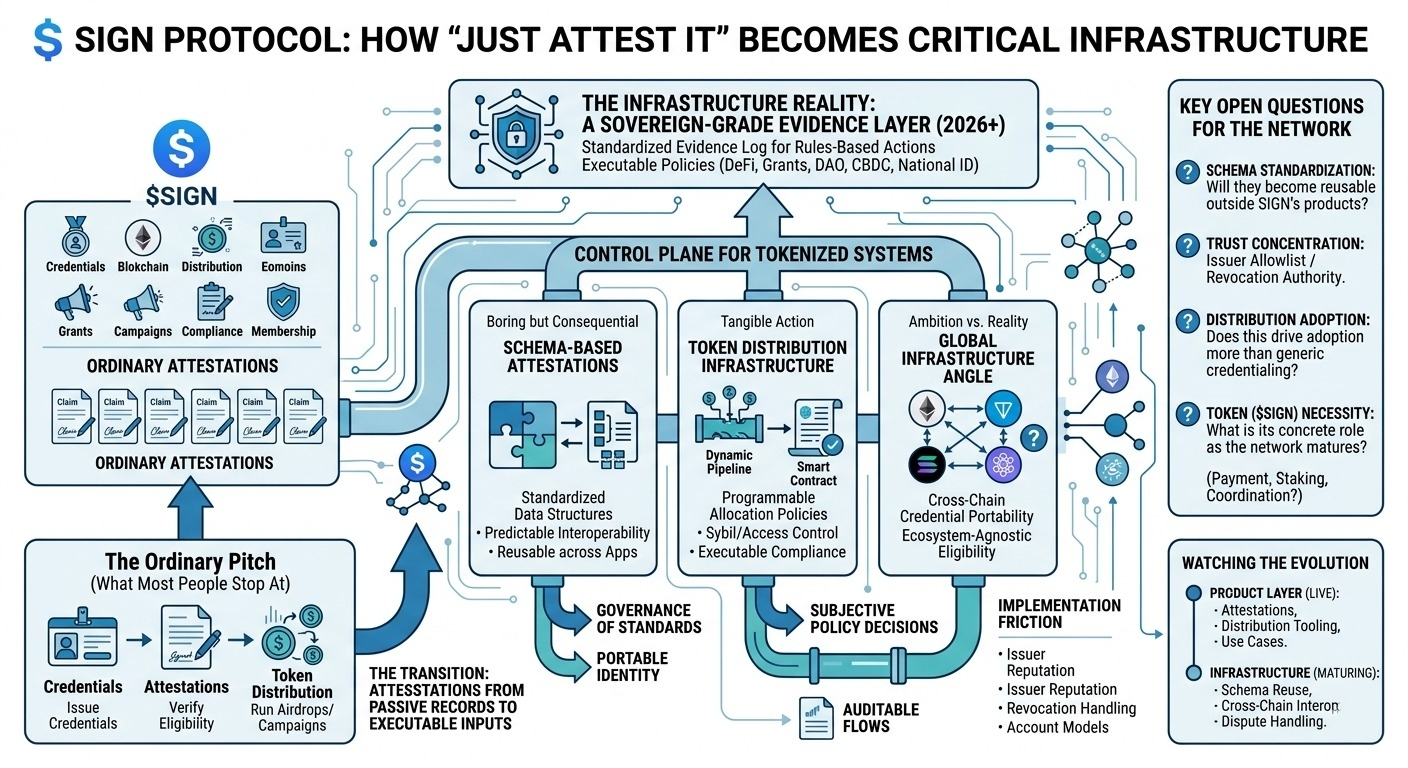
i think that’s the surface-level read most people stop at. SIGN is easy to summarize as an attestation protocol with a distribution product attached, plus SIGN as the coordination/economic layer. issue credentials, prove eligibility, reduce sybil noise, run an airdrop, maybe gate access to something. fair enough.
but that’s not the full picture.
the thing that looks simple here is the attestation itself. one party signs a claim about another party. almost too basic to notice. but once that primitive gets standardized and reused, it starts becoming a control plane for a bunch of different systems. not just identity-ish reputation, but grant eligibility, campaign completion, contributor history, KYC-adjacent status, cross-community membership, all the annoying “who qualifies?” questions that every tokenized system eventually runs into. and that’s where it gets interesting, because a protocol that only records claims is one thing; a protocol that feeds those claims into allocation and access decisions is doing something much more consequential.
one mechanism i keep circling is schema-based attestations. this sounds boring, and usually boring is where the real design choices are. if attestations follow common schemas, then apps can read and verify them in a predictable way. that lowers integration cost and gives credentials a chance to be portable instead of trapped inside one issuer’s product. but it also introduces a standards problem. whose schema becomes the default one for “verified human” or “eligible contributor”? open systems still end up with dominant formats, and once that happens, governance starts to matter more than the data structure itself.
second is the token distribution infrastructure. honestly this may be the more tangible part of SIGN today. projects don’t really struggle with creating narratives around fairness; they struggle with the implementation details of actually distributing assets without sybil leakage, jurisdiction headaches, broken claim flows, or support tickets from confused users. linking credential verification directly to distribution rails is practical. it turns attestations from passive records into executable policy inputs. but here’s the thing — the moment distribution gets encoded, decisions that looked neutral start becoming political. who gets included, who gets excluded, who can appeal, what proof counts. the protocol can make this process cleaner, but not less subjective.
the third piece is the “global infrastructure” angle, and i’m a little split on that. i get the ambition: credentials should outlive any one app or chain, and eligibility should be portable enough to work across ecosystems. that’s a strong idea. some of SIGN’s architecture and positioning clearly point there. but cross-chain trust systems usually look smoother in diagrams than they do in production. issuer reputation, revocation handling, privacy constraints, and chain-specific account models all add friction. so yes, global is plausible as a direction. as a clean end-state, less sure.
what feels real already is the product layer: attestations are live, distribution tooling is live, and there are actual use cases beyond theory. that matters. what feels more phased, maybe still forming, is the role of SIGN n the long run. i can see possible functions — payment, governance, staking, coordination incentives — but token necessity in infra systems is always where i get slightly skeptical. sometimes the protocol works because the workflow is useful, not because the token is structurally indispensable.
my main open question is around trust concentration. if this becomes a meaningful credential and distribution layer, then issuer allowlists, schema governance, and revocation authority become very high-leverage points. maybe that’s unavoidable. still, it’s the kind of thing that quietly defines whether the system is open infrastructure or just a well-run platform with a decentralized wrapper.
watching:
- whether schemas become reusable standards outside SIGN’s own product surface
- how issuer trust, revocation, and dispute handling actually work under stress
- whether distribution use cases drive adoption more than generic credentialing
- what SIGN concretely needed for as the network matures
- whether “global infrastructure” means interoperability at the standard level, or mainly broad deployment across ecosystems
$SIGN @SignOfficial #signdigitalsovereigninfra