 Crypto loves to promise decentralization. But underneath, control can hide quietly.
Crypto loves to promise decentralization. But underneath, control can hide quietly.
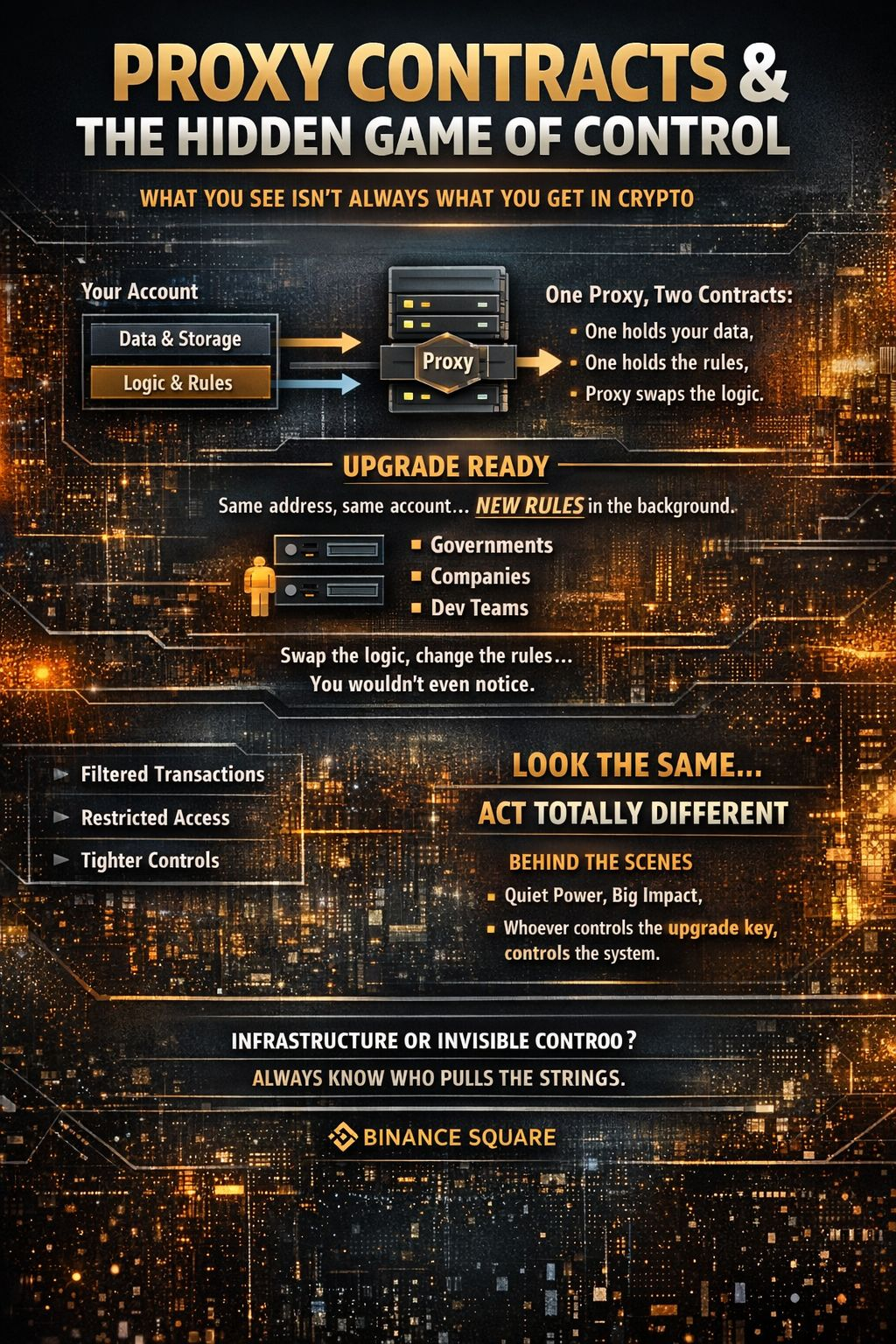
Take proxy contracts — sounds boring, right? Until you see what they really do:
One contract stores your balances, identity, and history.
Another contract holds the rules and logic.
You interact with a proxy that sits in front.
Here’s the catch: the logic can change without touching your account. Same address. Same user. Different rules.
This is the quiet power of upgradeable contracts.
Now add Sign Protocol to the mix:
It ties identity, verification, and token distribution into the system.
Upgrades aren’t just technical fixes — they can define who is allowed to do what.
On paper, it’s neat. In practice, the holder of the upgrade key has the real power.
Why it matters:
1. Decentralized in appearance, centralized in control — upgrades can silently alter permissions, filters, or access.
2. Governments or companies can encode policy as logic — what used to be external rules now live in code.
3. Token incentives drive behavior — verification becomes politics disguised as rewards.
The takeaway?
Crypto infrastructure isn’t neutral. It’s flexibility with a lever, and whoever holds the lever shapes the system.
That’s why before trusting any protocol, check:
Who controls the upgrade key?
Because that person, company, or authority is the real owner — not the code.
Smart crypto + modular design = potential.
Blind trust = risk.