$SIGN I used to think proxy contracts were just another technical detail something only developers care about. But the more I looked into it, the more I realized they sit right at the center of how power actually works in modern on-chain systems.
Let me explain it in a simple way.
Most people assume a smart contract is fixed. You deploy it, and that’s it. The rules are permanent. But that’s not always true anymore.
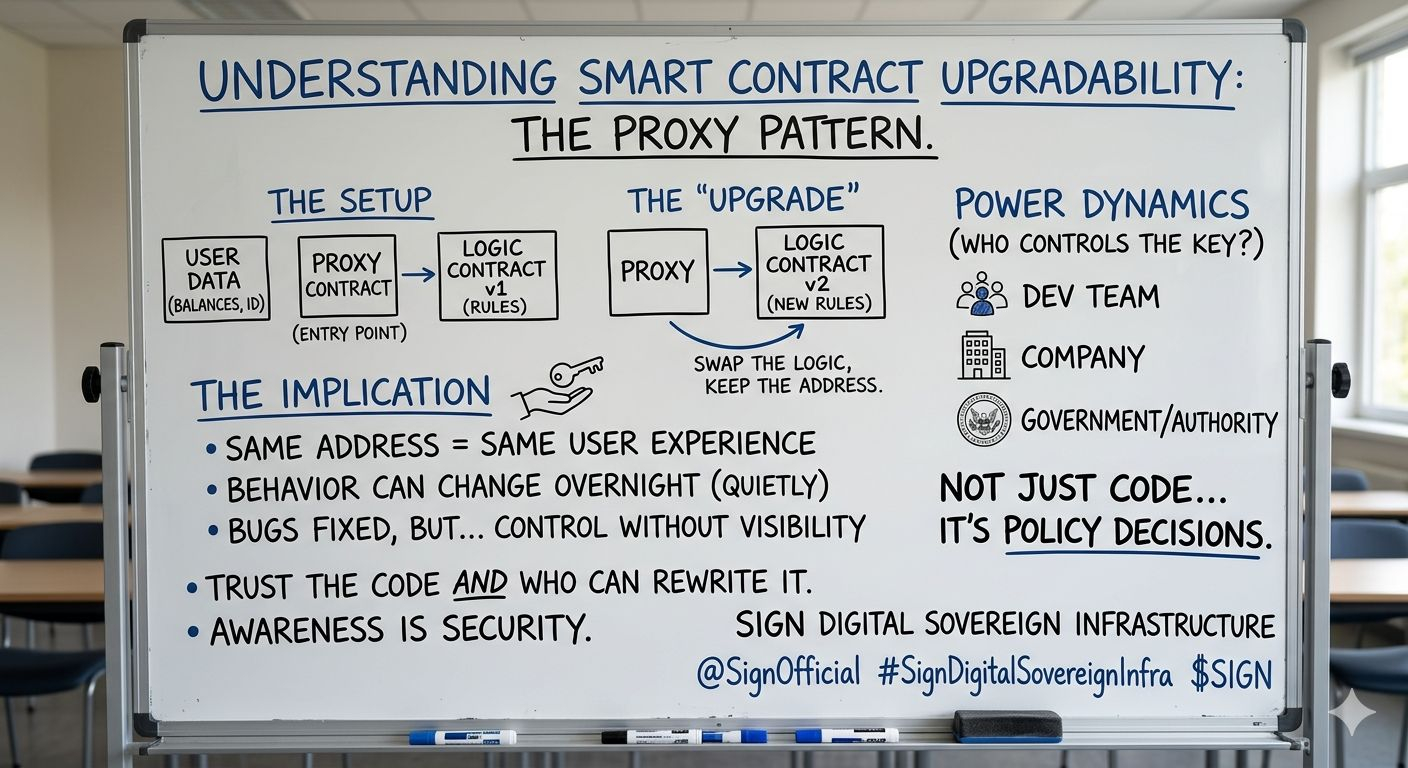
With upgradeable proxy patterns, things are structured differently. Your data like balances, identity, and history lives in one place. The logic the rules that decide how everything works lives somewhere else.
And in between, there’s the proxy.
You interact with the proxy address, thinking that’s the contract. But in reality, it’s just a middle layer pointing to the logic behind it.
Now here’s the part that changes everything:
That logic can be swapped.
Same contract address. Same user experience. But completely different behavior underneath.
That’s what “upgradeable” really means.
At first glance, it sounds like a good thing. And honestly, it is in many cases. Bugs need fixing. Systems evolve. No project wants to force millions of users to migrate every time something breaks.
But there’s another side to this.
If someone controls the upgrade authority, they don’t need to make noise to take control. They don’t need to shut systems down or freeze accounts in obvious ways.
They just update the logic quietly.
And overnight:
transactions might start getting filtered
permissions could shift
access rules might tighten
certain users could be restricted
All while everything looks normal on the surface.
No alerts. No migrations. No visible disruption.
That’s the real power of proxy architecture it allows change without friction, and control without visibility.
Now, when you bring a system like a sign protocol into this, it goes even deeper. Because now it’s not just about code execution it’s about identity, approvals, and verification.
So when an upgrade happens, it can influence who is allowed to interact, who gets validated, and who gets excluded.
At that point, upgrades are no longer just technical improvements they become policy decisions written into code.
And that’s where things get uncomfortable.
Because a system can feel decentralized from the outside, but still have a control lever built into its core.
I’m not Stubbornness upgrades. Without them, most systems would become outdated or break over time.
But we shouldn’t treat them as neutral either.
The real question isn’t whether a system is upgradeable.
The real question is:
Who controls the upgrade?
A small dev team? That’s one level of trust.
A company? That’s another layer.
A government or authority? That changes the entire risk model.
Because now you're not just trusting code you’re trusting whoever has the power to rewrite it.
And the most interesting part?
It doesn’t feel like control.
It feels like maintenance.
That’s why I’ve stopped blindly trusting “upgradeable” systems. They offer flexibility, but that flexibility always belongs to someone.
So before using any protocol, I try to understand one thing clearly:
Who holds the keys to change the rules?
Because in the end, that’s where the real ownership lives not in the code you see, but in the power behind it.
And if there’s one takeaway, it’s this:
Learn how the system works before you rely on it. That awareness is your first layer of security.
