That is probably the clearest signal in how Sign now talks about itself.
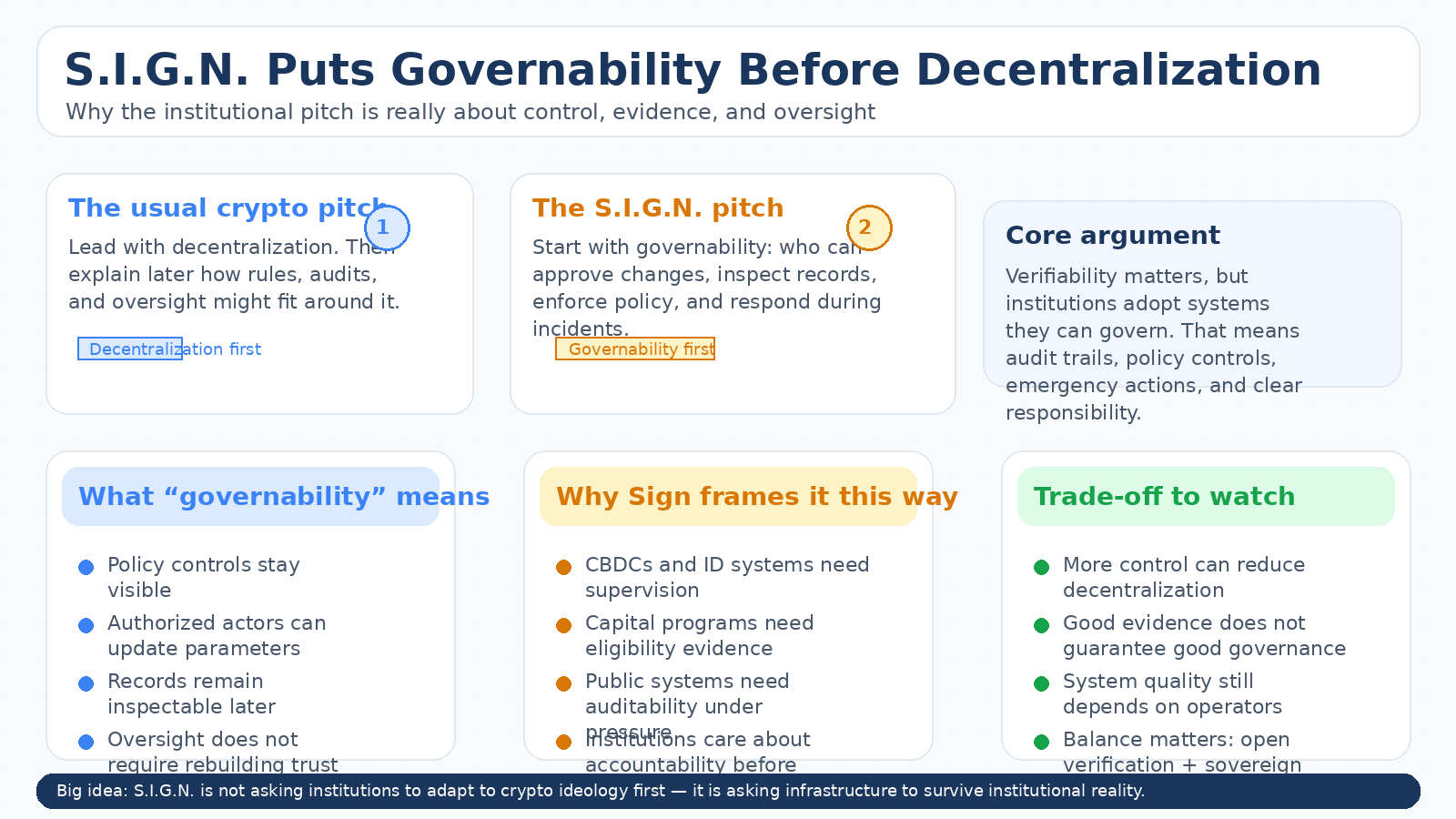
A lot of crypto projects still lead with decentralization as the moral headline and work backward from there. Sign’s current framing feels almost reversed. The docs put S.I.G.N. forward as “sovereign-grade digital infrastructure” for money, identity, and capital, then keep repeating a different set of priorities: governability, auditability, inspection-ready evidence, operational control, and interoperability under national-scale conditions. That is not anti-crypto language. But it is definitely not the usual crypto sales pitch either.
What makes this interesting to me is that the shift does not look accidental. The docs are explicit that S.I.G.N. is “not a product container” but a system-level blueprint for deployments that must remain governable, auditable, and operable under national concurrency. That wording matters. It tells you they are not trying to sell institutions on decentralization as an end in itself. They are trying to sell them on a stack where verification stays cryptographic, but policy, oversight, and emergency control remain intact.
I think that is the real institutional pivot.
Because once you start talking about CBDCs, national ID, benefits, subsidies, compliant capital programs, or public registries, the first question is usually not “how decentralized is this?” The first question is closer to: who can approve changes, who can inspect what happened, what rules applied, and what happens when something goes wrong? Sign’s whitepaper leans directly into that reality. It describes government-controlled transaction fee policies, validator criteria or whitelists in some deployment modes, multi-signature governance for protocol changes, parameter adjustments by authorized entities, and emergency controls for incidents. In plain terms, the system is designed so sovereign operators can keep their hands on the wheel.
That is where I think some people will misread the whole thing.
If you approach Sign expecting a pure decentralization story, the governance language can sound like compromise. But I do not think Sign is pitching ideological purity here. It is pitching something more pragmatic: an open, verifiable stack where evidence remains portable and cryptographic, while governance and operations stay compatible with regulated or sovereign requirements. The docs even say this outright in the deployment section: S.I.G.N. is “designed for deployment realities, not ideology,” with public, private, and hybrid modes depending on whether transparency or confidentiality comes first.
That phrase stuck with me.
“Not ideology” is doing a lot of work there. It suggests the team thinks the limiting factor for national or regulated infrastructure is not whether a system can be decentralized in the abstract. It is whether the system can be supervised, audited, upgraded, paused, and integrated without losing verifiability. In that model, decentralization is still useful, but it is no longer the first promise. Governability is.

And honestly, their evidence-layer framing supports that reading.
Sign Protocol is described as the shared evidence layer across deployments, built around schemas and attestations so systems can answer questions like who approved what, under which authority, when it happened, what ruleset version applied, and what evidence supported eligibility or compliance. That is a very institutional set of questions. It is less about censorship resistance as a slogan and more about making official actions reconstructable later.
I think that is why the decentralization debate can get a little too shallow here. If the real product is “inspection-ready evidence” across money, ID, and capital systems, then the more relevant question is not whether Sign maximizes decentralization at every layer. It is whether it creates a credible balance between cryptographic verification and sovereign control without collapsing into a closed vendor system. On paper, that is exactly the balance they are trying to strike: open standards, interoperable primitives, portable attestations, but policy and oversight held under sovereign governance.
My hesitation is that this balance is easier to describe than to sustain.
The more a system emphasizes government-controlled governance, parameter adjustments, validator permissions, and emergency actions, the more it depends on the quality of the institutions operating it. Verifiability can make actions legible. It cannot automatically make governance good. So I do not read Sign’s pitch as “trustless government infrastructure.” I read it more as infrastructure that tries to reduce blind trust by making authority, action, and evidence easier to inspect. That is a meaningful distinction. Also a narrower one.

So yes, I think the title is basically true.
S.I.G.N. is not putting decentralization at the center first. It is saying control, oversight, and auditability come first, and decentralization only matters if it can work alongside them.Whether people like that framing probably depends on what they think blockchain infrastructure is for. But Sign’s current docs are pretty clear about where they stand. They are not starting from the crypto ideal and asking institutions to adapt to it. They are starting from institutional constraints and asking crypto infrastructure to survive them.
@SignOfficial #SignDigitalSovereignInfra $SIGN

