Proxy contracts usually sound like one of those technical subjects that people skip because they seem too dry, too internal, or only relevant to developers. But the moment you understand what they actually do, they stop looking boring and start looking like one of the most important power mechanisms inside modern blockchain systems.
At the center of this architecture is a simple but powerful reality: the system you use today may not truly be the same system you use tomorrow, even if everything on the surface appears unchanged.
That is the real meaning of upgradeable proxy design.
In a traditional smart contract, logic and storage are usually deployed together. The rules, balances, permissions, and historical state all exist inside one fixed contract. Once deployed, that contract becomes difficult to alter, and that immutability is part of why blockchain earns trust in the first place.
Upgradeable proxy architecture changes that structure completely.
Instead of placing all functionality inside one permanent contract, developers separate the system into layers.
One contract stores the critical data: balances, identity records, permissions, historical interactions, and account state.
Another contract contains the actual logic: the rules that determine how the system behaves, what actions are allowed, and how each interaction is processed.
Between these two sits the proxy.
The user does not directly interact with the logic contract. Every action goes through the proxy contract, which forwards calls to whichever implementation contract is currently assigned behind it.
This creates the appearance of stability because the user continues interacting with the same contract address.
But underneath that stable address, the logic can change.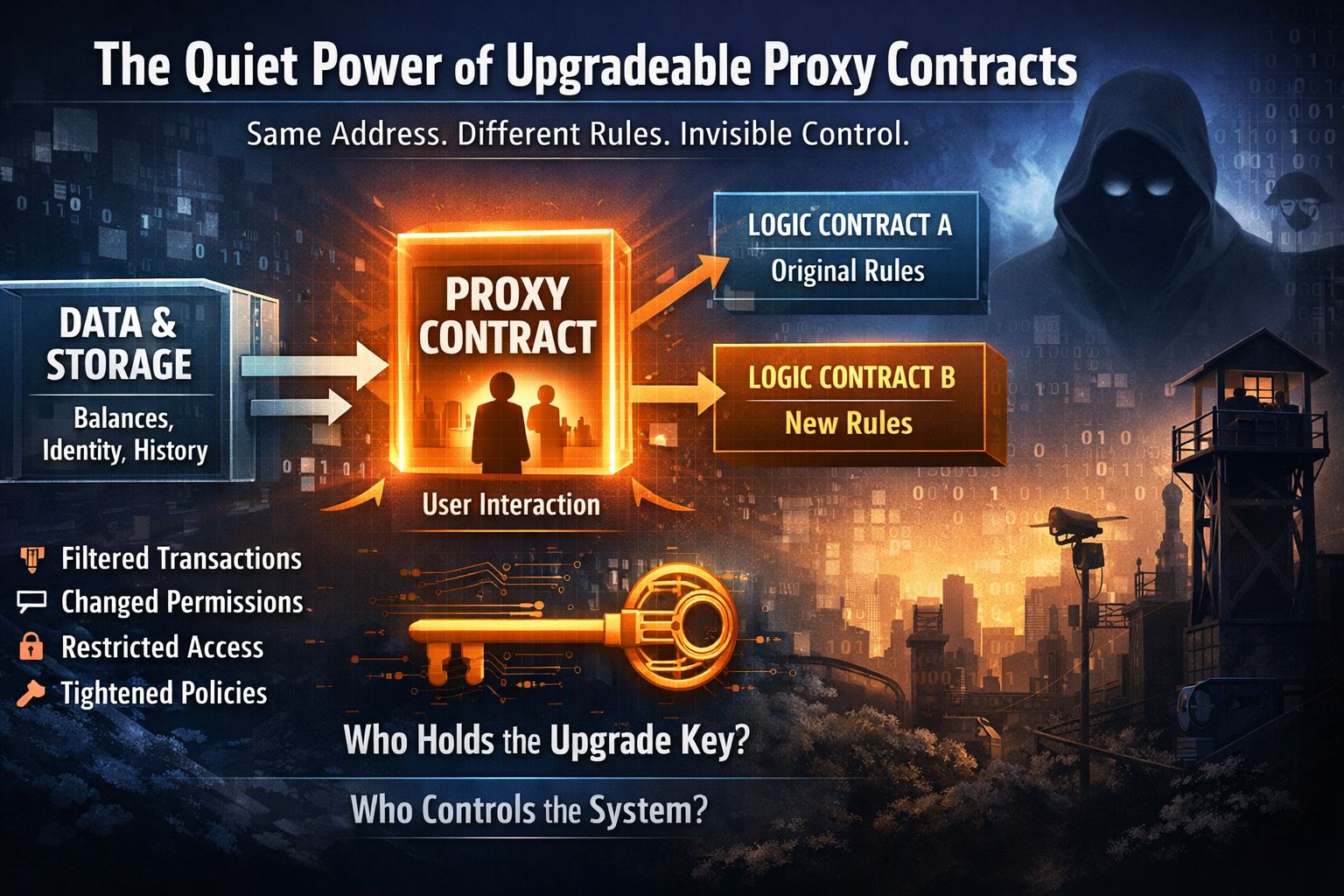
The implementation contract can be replaced while storage remains untouched.
The address remains the same. The account remains the same. The balances remain visible. From the outside, everything appears normal.
Yet the rules governing that same system may already be different.
That is what an upgrade really means: same address, same user interaction, but potentially new logic operating underneath.
On paper, this is extremely useful.
Software evolves. Bugs appear. Security vulnerabilities emerge. User needs change. No serious protocol wants to force millions of users to migrate manually every time a flaw is discovered or a feature must improve.
Upgradeable systems solve that operational problem elegantly.
But the technical advantage immediately creates a political question:
Who controls the upgrade?
Because the moment someone holds the upgrade authority, they do not only control maintenance.
They control future behavior.
And that control becomes serious very quickly.
If a government, institution, corporation, or centralized authority controls the upgrade key, they do not need dramatic intervention to reshape a system.
They do not need public shutdowns.
They do not need visible freezes.
They simply deploy a new implementation behind the proxy.
Quietly.
The contract address remains identical.
The interface remains familiar.
Users continue interacting normally.
But beneath that familiar surface:
transactions can begin filtering certain activity
permissions can change
access conditions can tighten
specific users can face new limitations
certain behaviors can become restricted
policy can enter the system through code
This is the quiet power of proxy architecture.
No migration.
No disruption.
No visible replacement.
Only altered logic hidden behind continuity.
And when a sign protocol layer becomes connected to this model, the implications become even more important.
Because now upgrades do not only affect technical execution.
They affect identity, approval, validation, and who is allowed to participate inside the system.
A sign-based protocol introduces another decision layer: proof, legitimacy, permission, and recognition.
That means upgrades can influence not just what transactions do, but who qualifies to make them under changing conditions.
At that point, the architecture begins to carry more than technical flexibility.
It begins carrying institutional power.
The result is a system that may feel decentralized at the surface while still containing a central control lever underneath.
This does not automatically make upgrades wrong.
Without upgradeability, many modern systems would become fragile, outdated, or unsafe over time. Real infrastructure requires maintenance.
But flexibility is never neutral.
Flexibility always belongs to whoever controls change.
If that control belongs to a small development team, one kind of risk exists.
If it belongs to a company, another kind emerges.
If it belongs to a government, the meaning changes entirely because code stops behaving like software alone and starts functioning like policy.
And policy delivered through code is often harder to notice because it arrives disguised as technical maintenance.
That is why upgradeable systems deserve more attention than they usually receive.
The real question is not whether a protocol looks decentralized today.
The real question is who can rewrite the rules tomorrow without asking anyone.
Because in many systems, the visible contract is not the final source of power.
The real power often sits with whoever controls the upgrade key.
That is why before trusting any protocol, the first thing worth checking is not only what the code currently does, but who has authority over what that code may become later.
Understanding architecture matters because power in digital systems is rarely obvious.
And if you do not understand who controls the upgrade path, you may misunderstand who truly controls the system itself.
Most users read interfaces.
Few users read authority structures.
But in upgradeable systems, authority is where the real ownership begins.
And that is exactly why learning the technology before trusting it is no longer optional.