I used to believe that digital systems would eventually converge into a single layer of truth. It felt inevitable. If blockchains made data immutable and transparent, then identity, capital, and execution would naturally align over time. Adoption, I assumed, would follow coherence.
But what I saw in practice was the opposite.
The same user behaving like a different entity across applications. The same credentials losing meaning outside their origin. The same capital flowing through systems that couldn’t recognize prior verification. Nothing was technically broken but nothing carried forward.
That’s where the doubt began.
It wasn’t a failure of ideas. It was a failure of continuity. Systems worked in isolation, but not in sequence. Trust existed, but it didn’t persist.
Looking closer, the issue wasn’t inefficiency, it was repetition.
Each application rebuilt identity from scratch. Each workflow required fresh verification. Each distribution redefined eligibility independently. There was no shared memory across systems.
It created a subtle kind of friction. Not the kind that forces users to stop, but the kind that prevents them from returning.
What felt “off” wasn’t the absence of infrastructure. It was the absence of reuse.
Concepts like verifiable identity and on chain execution sounded important. But in practice, they behaved like features visible, isolated, and repeatedly invoked instead of infrastructure that quietly supports interaction.
And that led me to a more uncomfortable question:
If verification cannot be reused, is it really verification?
Over time, I stopped focusing on what systems claimed to enable. I started paying attention to what they removed.
Do they eliminate repeated effort?
Do they allow behavior to carry forward?
Do they operate without requiring constant user awareness?
The systems that endure don’t demand attention. They reduce it.
They don’t introduce new steps, they remove the need to repeat old ones.
That shift from narrative to usability changed how I see everything.
When I first came across @SignOfficial , I didn’t immediately see it as something fundamentally different. At first, this felt like another attempt to formalize trust, something crypto has explored many times.
But upon reflection, what stood out wasn’t what it claimed to solve. It was how it framed the system.
The idea of S.I.G.N. not as a protocol, but as a sovereign system architecture.
That distinction changes everything.
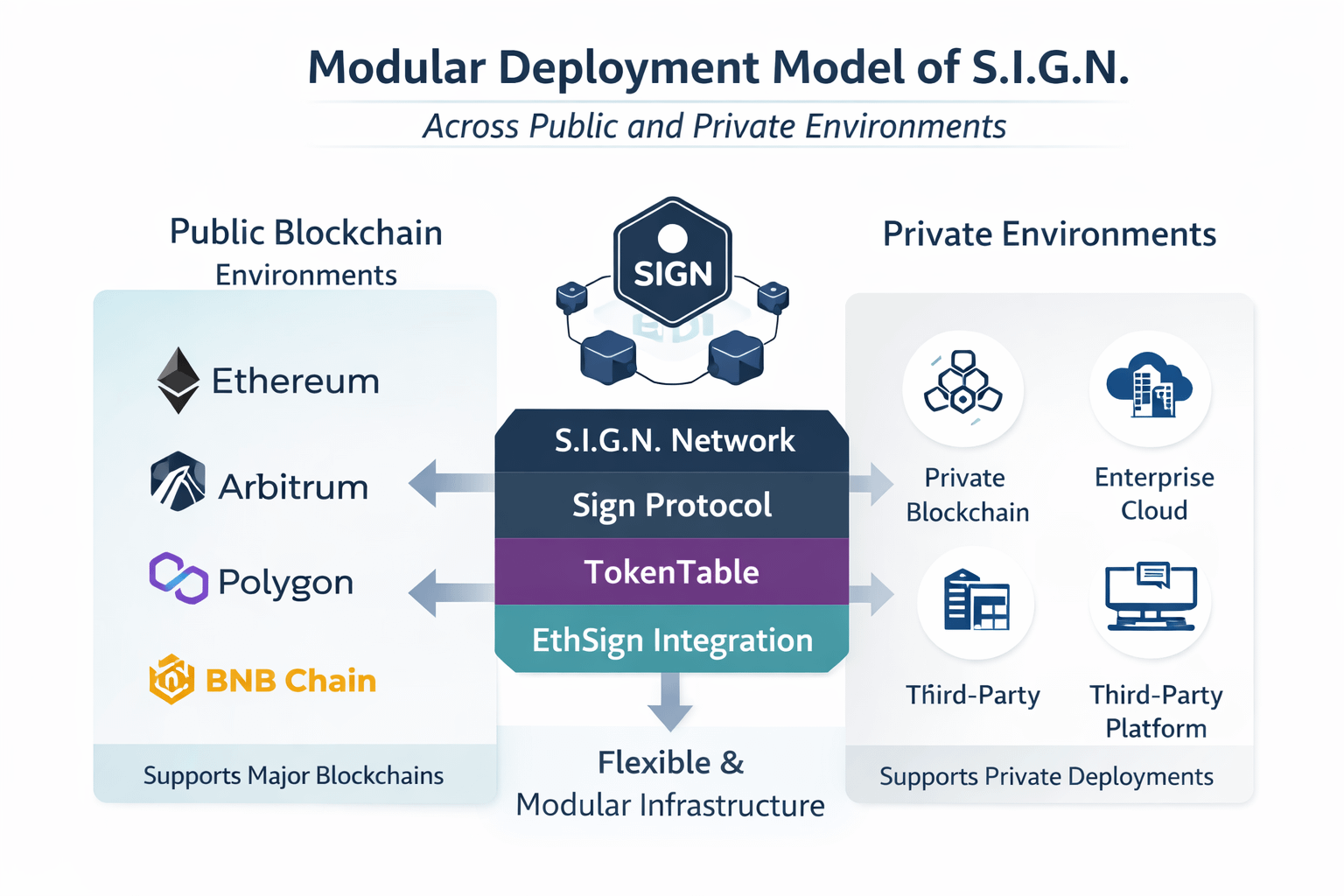
S.I.G.N. does not define a single network. It does not enforce a unified stack. It defines how systems can be structured especially in environments where sovereignty, regulation, or institutional control matter.
It is not trying to replace systems. It is trying to structure how they relate.
Instead of asking whether identity can be decentralized, the framing becomes more precise:
Can identity act as a stable anchor across systems, while attestations carry reusable, verifiable context?
Can verification persist even when execution environments differ?
This is less about standardizing everything, and more about enabling continuity without forcing uniformity.
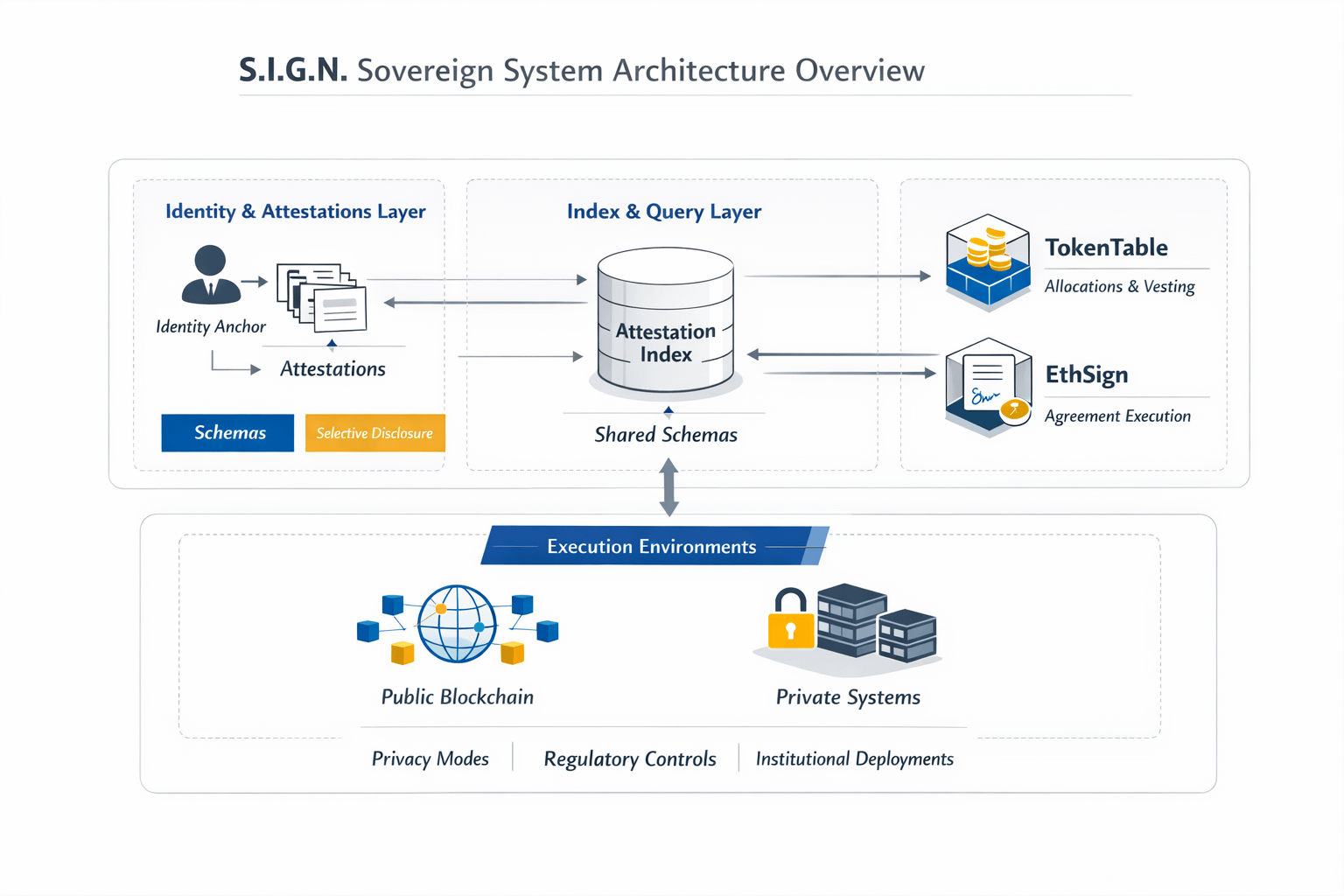
At the core of this architecture is $SIGN Protocol, which introduces schemas and attestations.
Schemas define the structure of claims, acting as a coordination layer that allows different systems to interpret attestations consistently. They reduce ambiguity not by enforcing sameness, but by aligning meaning.
Attestations are structured claims tied to an identity. They represent statements about eligibility, reputation, compliance, or action that can be verified and referenced across contexts.
But what matters is not just their creation. It’s their lifecycle.
Attestations can be public or private depending on context. They can be selectively disclosed rather than fully exposed. And importantly, they are indexed and queryable, allowing systems to retrieve and reuse verification without restarting the process.
Reuse, however, is not automatic. It depends on shared schemas and trusted issuers, which means interoperability is structured rather than universal.
Then there are components like TokenTable and EthSign.
TokenTable structures allocation and distribution defining how capital is released over time, under specific conditions, and to specific participants.
EthSign formalizes agreements into verifiable proofs of execution, turning signatures into attestable outcomes that can be referenced beyond the moment they occur.
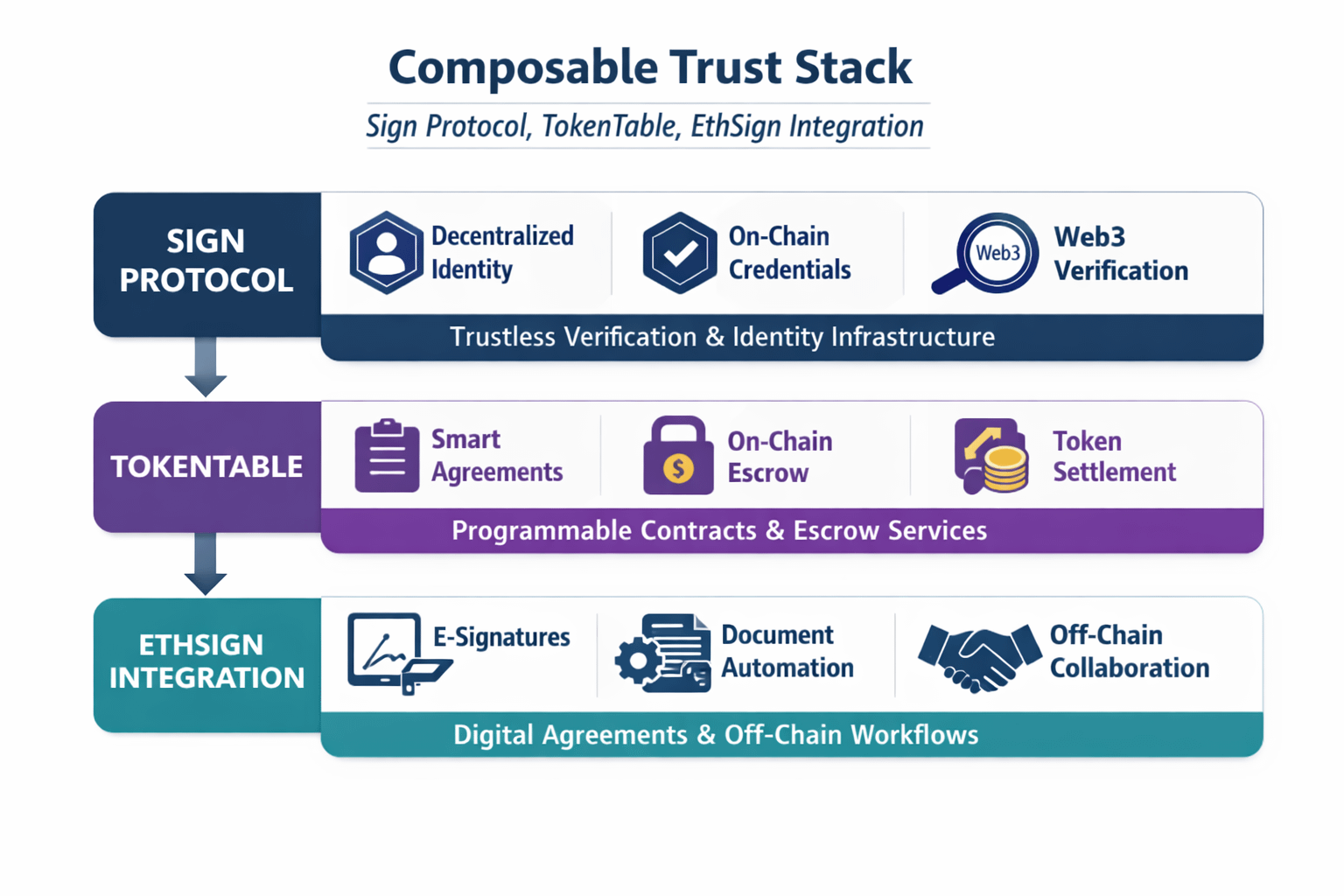
An important architectural detail is that these are not subsystems of S.I.G.N.
They remain independent, deployable components. Within a S.I.G.N. deployment, they are composed only when their specific capabilities are required.
This preserves flexibility while enabling structure.
Most real world systems don’t operate in a single environment.
Financial workflows, for example, span public interfaces, private systems, and regulated processes. Identity is verified once but used repeatedly. Execution happens in different layers but references prior validation.
S.I.G.N. aligns with this pattern.
It allows identity to act as an anchor, while attestations carry forward context across systems. Execution can happen in controlled environments, while verification remains portable.
Privacy modes reinforce this. Not every claim needs to be public. Not every system requires full disclosure. Information can be revealed selectively, aligning with how institutions actually operate.
What this reflects is a shift in how digital trust is being structured.
In many emerging regions, including parts of the Middle East and South Asia, digital infrastructure is expanding rapidly but often without continuity.
Systems are built quickly, but they don’t always connect. Identity becomes fragmented. Verification becomes localized. Trust becomes situational.
An architecture like S.I.G.N. doesn’t solve this automatically. But it introduces a way to structure systems so that trust can persist across them.
Not by forcing uniformity, but by enabling reuse where coordination exists.
Markets tend to reward what is visible.
New features, token activity, and narrative cycles generate attention. But attention is not the same as usage.
Usage is quieter.
It appears when users don’t need to repeat actions. When systems don’t need to revalidate identity. When workflows carry forward instead of restarting.
S.I.G.N. depends on this kind of usage.
Not one time interaction, but repeated reliance on attestations, schemas, and structured verification.
That’s harder to measure. And slower to emerge.
There’s a real possibility that this model doesn’t reach its intended form.
If identity is not embedded into real workflows, attestations remain optional. And optional systems rarely sustain usage.
If developers treat these primitives as add ons rather than foundational layers, the system won’t produce continuity, it will reproduce fragmentation.
There’s also the issue of threshold.
For reuse to matter, there needs to be enough repeated interaction across systems. Without that, the benefits remain theoretical.
The architecture can exist without adoption. But it cannot function as infrastructure without it.
I’ve become more cautious about equating complexity with progress.
More components don’t necessarily mean better systems. What matters is whether behavior becomes simpler, more consistent, more predictable.
#SignDigitalSovereignInfra doesn’t eliminate complexity. It reorganizes it.
It places identity, verification, and execution into a structure where they can be reused rather than rebuilt.
But whether that leads to clarity depends on how it is implemented.
I don’t look for announcements anymore. I look for patterns.
Applications where identity is required, not optional.
Users interacting multiple times without re-verification.
Attestations being referenced across contexts, not recreated.
Sustained activity from issuers and verifiers over time.
Not spikes, continuity.
That’s when a system starts behaving like infrastructure.
I used to think that if something made logical sense, it would eventually become necessary.
But necessity doesn’t emerge from logic alone.
It emerges from repetition.
From systems that stop asking users to prove themselves again.
From processes that remember prior interactions.
From structures that allow trust to carry forward.
The difference between an idea that sounds necessary and infrastructure that becomes necessary isn’t design.
It’s whether it gets used again quietly, repeatedly, and without being noticed.