Schema Hooks are a way for developers to run custom logic when an attestation is created or revoked on Sign Protocol. They allow schema creators to extend behavior beyond simple data recording. With schema hooks, developers can introduce rules such as access control, payment handling, or any custom verification logic before an attestation is accepted.
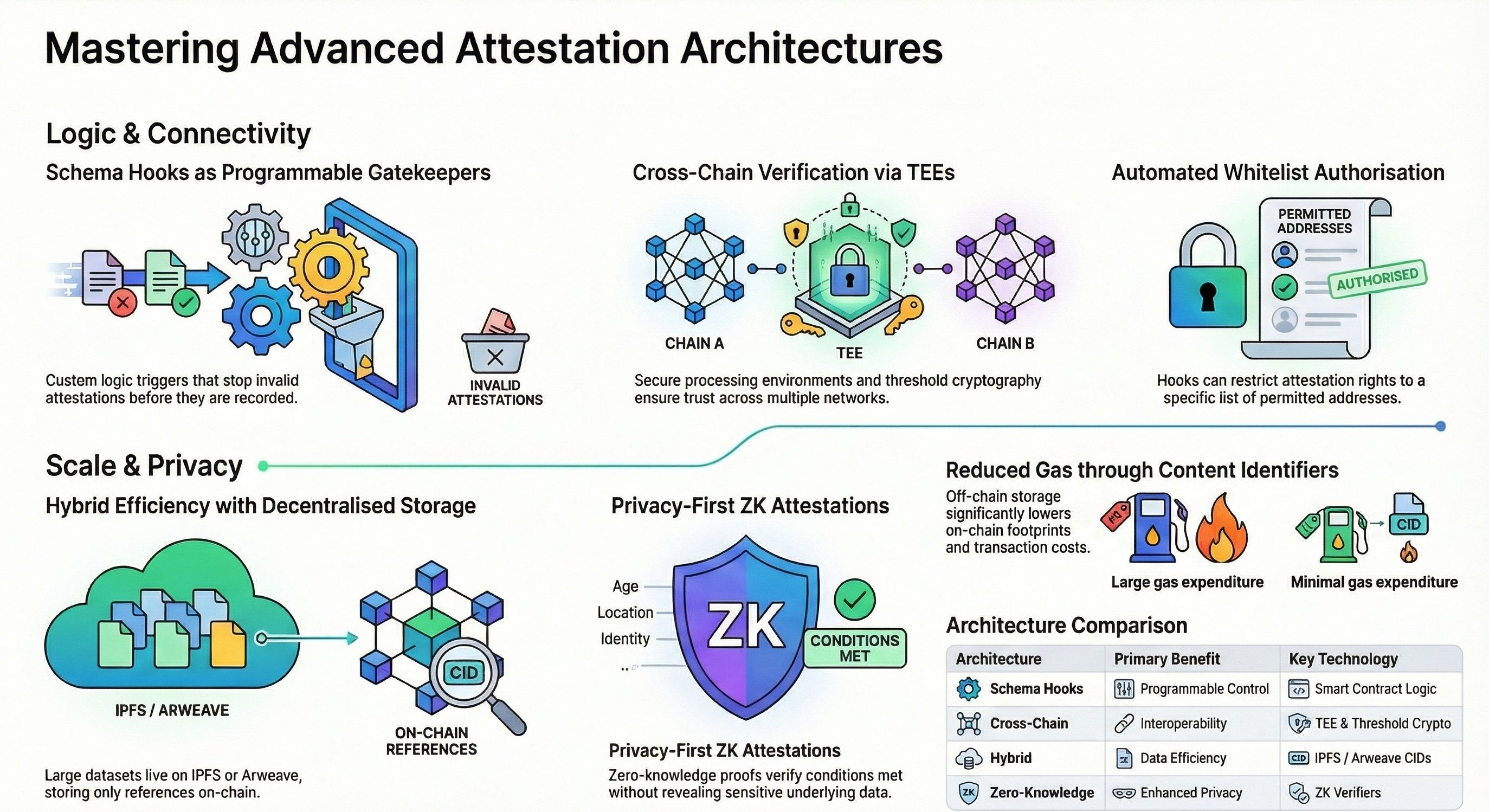
When a schema hook is used, it is executed through a smart contract that follows a defined interface. Every time an attestation request comes in, the hook is triggered. If the logic inside the hook fails, the entire attestation process is stopped. This gives full control to the schema creator to decide what conditions must be satisfied before an attestation becomes valid. In this way, schema hooks act as a gatekeeper for both attestation creation and revocation.
A common use case is a whitelist system. In this setup, only approved addresses are allowed to create attestations. The contract maintains a list of permitted users, and the hook checks whether the attester is included in that list. If the user is not authorized, the transaction is rejected. This pattern is useful for private systems, restricted communities, or controlled applications where only selected participants should interact with the schema.
Cross chain attestations solve another major challenge in blockchain systems. Data is usually isolated within a single network, which means information recorded on one chain cannot be directly used on another. This creates limitations for developers who want their attestations to be valid across multiple networks. For example, an attestation created on one chain should ideally be recognized on another chain without losing trust.
To address this, Sign Protocol integrates with a decentralized verification approach using a trusted execution environment. A trusted execution environment is a secure processing space that isolates sensitive computations from the rest of the system. Even if the main system is exposed, the operations inside this environment remain protected. This ensures that verification logic and cryptographic operations are executed safely without interference.
In the cross chain workflow, a user submits an attestation request that includes details such as the target chain and the attestation data. This information is encoded efficiently and passed through the hook. The hook may require a fee to cover verification costs, often paid using $USDC where one unit represents credits for processing. The hook then emits an event that carries the required data for off chain verification systems.
A specialized process then listens to this event and performs the verification steps. It retrieves the target attestation from the specified chain, compares it with the provided data, and checks whether both match. After validation, a signed response is generated using threshold cryptography. This response is produced by multiple independent nodes that must reach consensus, ensuring that no single party controls the result. Once verified, the attestation is finalized on the protocol.
Hybrid attestations offer another approach for handling data. Instead of storing all information directly on chain, the actual data is stored on decentralized storage systems such as Arweave or IPFS. Only a reference to that data, usually a content identifier, is stored within the attestation itself. This makes the process more efficient and reduces costs, especially when dealing with large datasets.
In this model, developers first upload their data off chain. After that, the returned content identifier is included in the attestation. This allows applications to quickly retrieve the data without repeatedly interacting with the blockchain. It also improves scalability and reduces gas usage. Hybrid attestations are especially useful for applications that require frequent reads or handle large structured data.
ZK attestations introduce an additional layer of privacy and verification. Zero knowledge proofs allow a user to prove that certain conditions are met without revealing the underlying data. By integrating a ZK verifier into a schema hook, developers can validate proofs directly within the attestation flow. This enables use cases where sensitive information must remain hidden while still being mathematically verified.
For developers building on Sign Protocol, these features together create a flexible and powerful system. Schema hooks provide programmable control, cross chain attestations extend interoperability, hybrid attestations improve data efficiency, and ZK attestations enhance privacy. Combined, they allow applications to build secure, scalable, and interoperable identity and verification systems across multiple environments.
@SignOfficial continues to expand these capabilities to support builders who need reliable infrastructure for modern decentralized applications.