I was reading through SIGN Protocol stuff again — litepaper, product docs, a bit of TokenTable context — and i had the same reaction i usually have with this category: at first glance it feels almost too simple. attestations, credential verification, token distribution. ok, sure. useful, probably. not exactly the kind of thing people romanticize when they talk about crypto infra.
And i think that’s how most people file it away. SIGN is the thing for credentials and airdrop-ish distribution, maybe with some identity rails attached. a practical stack for proving someone did something, or is allowed to receive something, and then handling the payout. clean enough story. easy to understand.
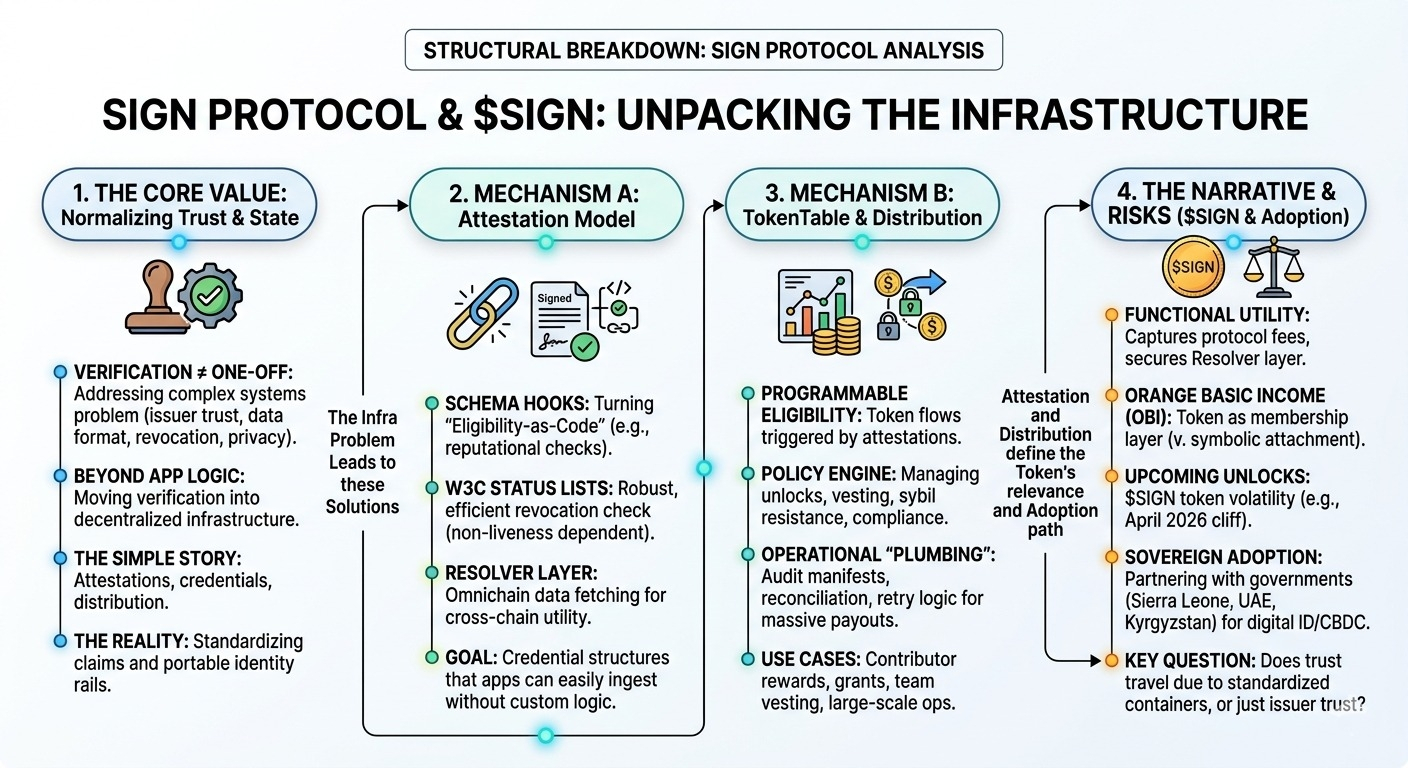
But that’s not the full picture. the simple story hides a deeper systems problem, which is that “verification” is never just verification. it’s issuer trust, data format, revocation, portability, timing, privacy, and then the uncomfortable part: whether another app or institution agrees that the claim means what the issuer says it means. and that’s where it gets interesting, because SIGN is trying to turn that whole mess into infra instead of one-off app logic.
The first mechanism that seems more important than it looks is the attestation model itself. on paper, an attestation is just a signed claim. but in production, that’s not enough. a useful credential system needs schemas, issuer identity, support for updates or revocations, and some way for third parties to verify without rebuilding everything from scratch. SIGN’s design seems aimed at making credentials structured and portable enough that different apps can issue and consume them with less bespoke glue. that’s a lot more ambitious than “sign a message onchain.” if this works, the value isn’t the signature — it’s the normalization layer around what’s being asserted and who gets to assert it.
The second mechanism is the token distribution side, and honestly this might be the most real part of the system today. TokenTable and related flows solve something people tend to oversimplify. distribution sounds like a transfer problem, but it’s usually a policy and state management problem. who qualifies, how much they get, when they unlock, whether they can claim across chains, whether sybil resistance or compliance checks are baked in. if attestations become the input layer for that, then token distribution starts to look less like a one-off campaign tool and more like programmable eligibility infrastructure. contributor rewards, grants, user incentives, team vesting — same underlying pattern, different surface UX.
Then there’s the third piece: $SIGN. this is where i slow down a bit. the token is presented as part of the broader network architecture, helping align governance and maybe economic activity around the credential/distribution layer. maybe that happens. maybe it even becomes necessary if protocol usage and verification markets deepen enough. but right now, at least from an operator lens, the products feel more concrete than the token thesis. the attestation and distribution rails are understandable as software. the token role is more phased, more conditional on future adoption patterns. not a red flag exactly, just something i’d separate carefully instead of treating as one unified thing.
That live-versus-promised split feels important here. what’s live now is tangible: credential issuance, attestation workflows, token distribution tooling, real usage. what’s less settled is whether SIGN becomes shared infrastructure across unrelated ecosystems, instead of a successful set of products used inside its own orbit. those are different outcomes. a lot of systems say “global verification layer,” but in practice they become trusted within a narrower network of issuers and apps. still valuable, just not quite the same thing.
My main question is whether the semantics travel. if one app issues a credential and another app accepts it, was that because the protocol made the attestation portable, or because both apps already trusted the same issuer? that distinction matters. a credential network only gets stronger when verification composes beyond the original context. otherwise you end up with standardized containers for siloed trust.
Also, the closer this gets to real-world institutions — schools, governments, compliance providers, employers, maybe exchanges — the more the protocol inherits their messiness. revocation rules, privacy expectations, legal constraints, identity disputes. i don’t think that breaks the model, but it does mean “decentralized credential infra” may eventually look a lot more institution-shaped than people expect. but here’s the thing, maybe that’s unavoidable if the credentials actually matter.
watching:
- whether third-party apps verify SIGN attestations without custom issuer-specific logic
- how revocation and credential updates are handled over time, not just at issuance
- whether TokenTable usage keeps showing up in boring recurring ops, not just token launch moments
- how much $SIGN becomes functionally necessary versus symbolically attached
- which issuers end up carrying the most trust, because that may define the network more than the protocol does.
$SIGN @SignOfficial #signdigitalsovereigninfra