The more I sit with SIGN, the less I see it as something that makes sense only through one feature, one token, or one app.
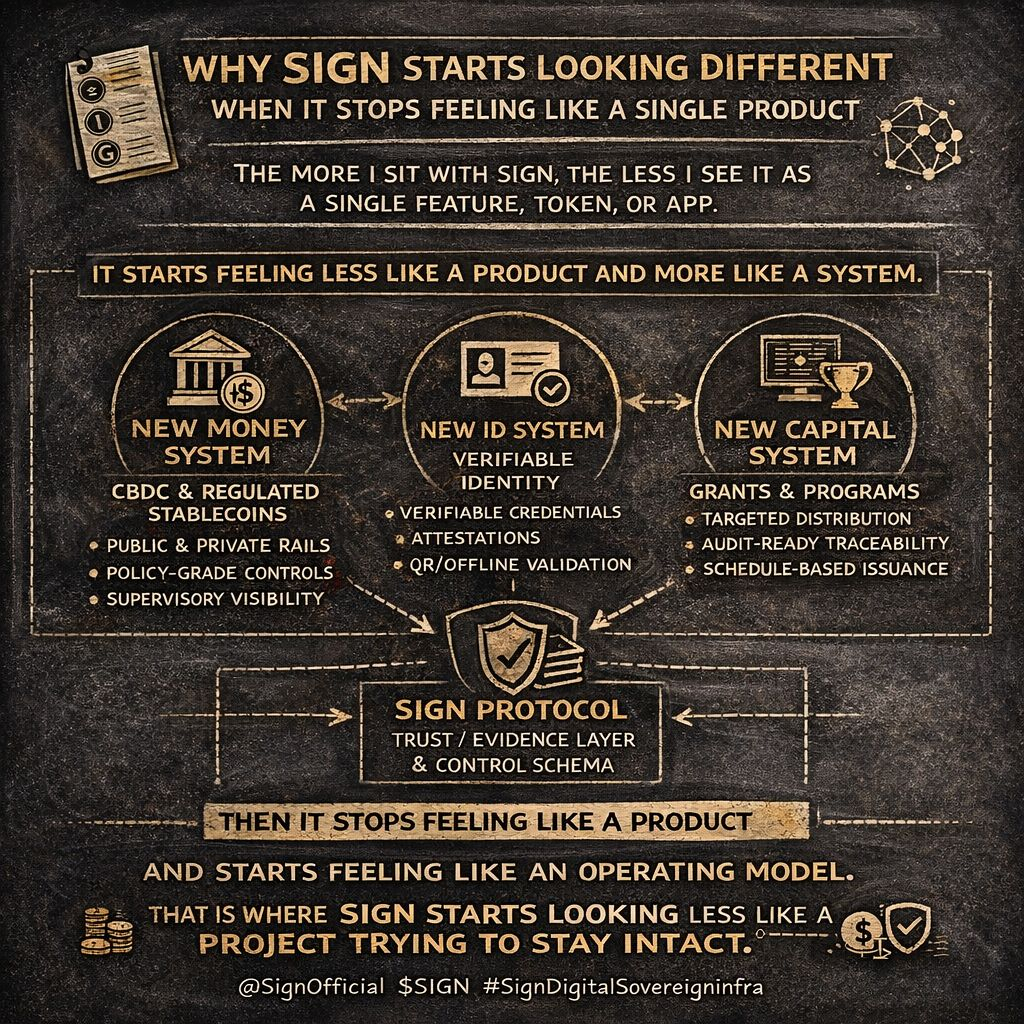
That is usually how a lot of projects get packaged. Find one simple label, repeat it enough times, and the market starts treating the whole system as if it can be understood from that one angle alone. What makes SIGN more interesting to me is that the official material keeps pushing in the opposite direction. S.I.G.N. is framed as sovereign-grade digital infrastructure for money, identity, and capital, with Sign Protocol as the shared evidence layer across those systems. The docs are also explicit that S.I.G.N. is not a single blockchain, a single ledger, or a vendor-style product shell. It is a system-level blueprint and operating model.
That difference matters more than it first appears.
Most people are used to judging a project by what it does on the surface. Can it move money? Can it verify identity? Can it distribute value? Those are fair questions, but they are still narrow questions. What started pulling me deeper into SIGN is that it seems to be built around a harder one: what kind of system has to exist underneath if money, identity, and capital all need to stay governable, auditable, and operable at the same time? The more I read, the more that started feeling like the real point.
That is also why the stack feels more coherent to me than it did at first.
The New Money System is described as infrastructure for CBDC and regulated stablecoins across public and private rails, with policy-grade controls and supervisory visibility. The New ID System is built around verifiable credentials, DIDs, selective disclosure, trust registries, revocation checks, and offline presentation patterns like QR and NFC. The New Capital System is framed around grants, benefits, incentives, and compliant capital programs, with identity-linked targeting, schedule-based distributions, and audit-ready traceability. Then underneath those systems sits Sign Protocol, which the docs describe as the trust and evidence layer used to define, write, verify, and query structured claims over time.
To me, that changes the way the whole project reads.
It stops feeling like a collection of separate products and starts feeling more like an operating model. One layer handles execution. Another handles credentials. Another handles capital logic. And then there is a shared evidence layer that keeps the process explainable later. That is a much more serious design than the usual “here is our feature” pitch. It suggests the project is not only asking whether something can happen, but whether the logic behind it can still be carried across agencies, systems, audits, and policy constraints without breaking apart.
This is where SIGN starts feeling different to me from a lot of things in the market.
A normal product story usually wants me to focus on the visible output. A system story makes me focus on continuity. It makes me ask whether the same structure can survive changing rules, different operators, compliance demands, and the need for oversight later. SIGN’s own docs lean into exactly that reality. They describe S.I.G.N. deployments as systems that must remain governable, operable, and auditable, not just technically functional. The governance model itself is split into policy governance, operational governance, and technical governance, which tells me the project is thinking beyond code and into institutional durability.
And honestly, that is the part I find strongest.
A lot of projects sound impressive while everything is still in the “what can this do?” phase. Fewer start sounding stronger when the question becomes “how does this stay coherent once real responsibility enters the picture?” That is the lens through which SIGN has been getting more interesting to me. Not because it is trying to look bigger than it is, but because it seems willing to define the harder layer most people usually skip — the layer where policy, identity, execution, evidence, and auditability all have to stay connected instead of drifting into separate silos.
That is why I do not read SIGN like a single-product story anymore.
I read it more like an attempt to answer a harder systems question: what does digital infrastructure look like when trust cannot stay vague, when evidence has to travel, and when the system still has to make sense long after the action is complete? For me, that is where SIGN starts feeling less like a project trying to impress from the outside and more like one trying to stay intact from the inside.