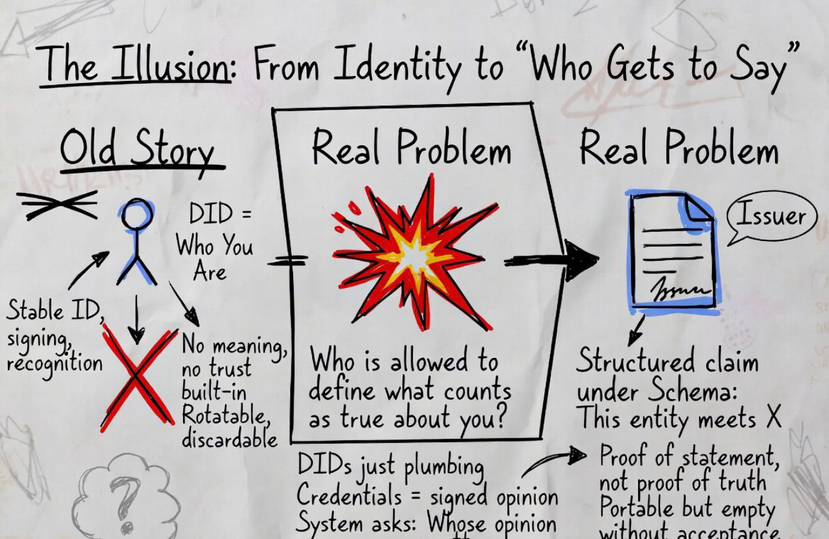
I used to think this whole stack DIDs, credentials, registries was about identity. The way it’s usually explained makes it sound like we’re solving “who you are” on-chain. But the more I sat with it, the less that felt true.
Because identity was never the real bottleneck.
The real problem is simpler, and more uncomfortable: who gets to say something about you and why anyone else should accept it.
A DID looks important at first. It gives you a stable reference, a way to sign and be recognized again later. But after a point, it becomes clear that a DID doesn’t carry meaning. It doesn’t carry trust. It just makes interactions consistent. You can rotate it, create more of them, discard one entirely nothing about it forces the system to care.
The same thing happens with credentials.
A verifiable credential feels like “proof,” but it’s not proof in the way people assume. It’s a structured statement, signed under a schema. Something like: this issuer says this entity meets these conditions. That’s precise, and it’s portable, but it still doesn’t answer the real question.
Because now the system isn’t asking what is true.
It’s asking who is allowed to define what counts as true.
That’s where most explanations stop, but that’s exactly where the system actually begins.
Once multiple issuers exist, the problem shifts. You don’t need more credentials. You need a way to filter them. Someone or something has to decide which issuers matter in a given context. That’s what trust registries really are, even if they’re not always framed that way.
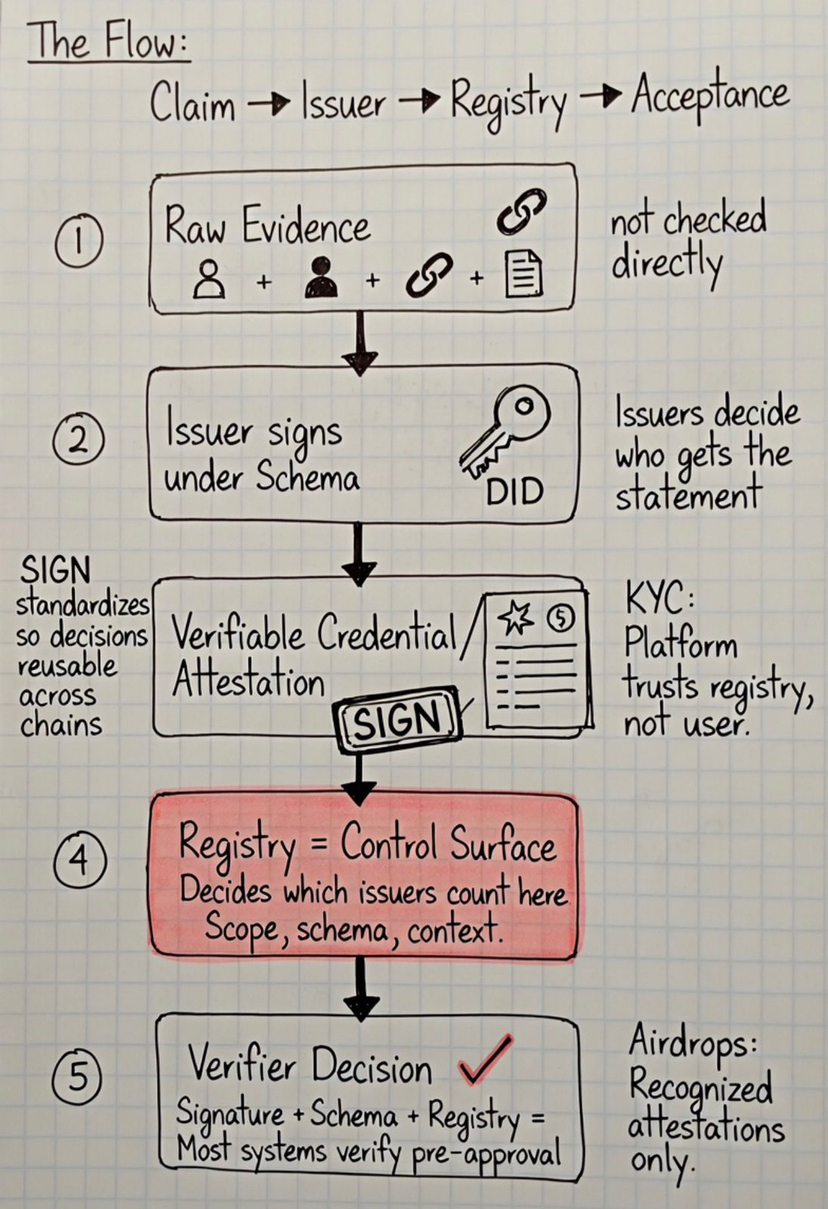
They’re not just lists.
They’re control surfaces.
They define which issuers are recognized for a schema, under what scope and for which decisions. And once that layer is in place, the whole system behaves differently.
Now verification is no longer just about checking a signature.
It becomes a combination of three things:
• the schema that defines meaning
• the issuer that signs the claim
• the registry that decides whether that issuer counts
In practice, every decision becomes:
claim → issuer → registry → acceptance
SIGN doesn’t just connect these layers.
It standardizes how they interact schemas, attestations and acceptance logic so different systems can trust the same decision without re-checking it. Its on-chain schema registry and attestation model make these coordination points queryable and reusable across chains.
What made this click for me was watching how this plays out in real flows.
Take something like KYC. A user holds a credential that says they’re verified. The platform doesn’t inspect the user directly. It checks whether the issuer of that credential is part of its accepted registry. The decision is already shaped before the user even enters the system.
Most systems today don’t verify users.
They verify whether someone else already approved them.
Or take contribution-based airdrops. Instead of measuring raw activity, projects can rely on attestations issued by recognized contributors or programs. That makes the system cleaner but it also means contribution is no longer something the system evaluates directly. It’s something an issuer interprets.
That’s a very different model.
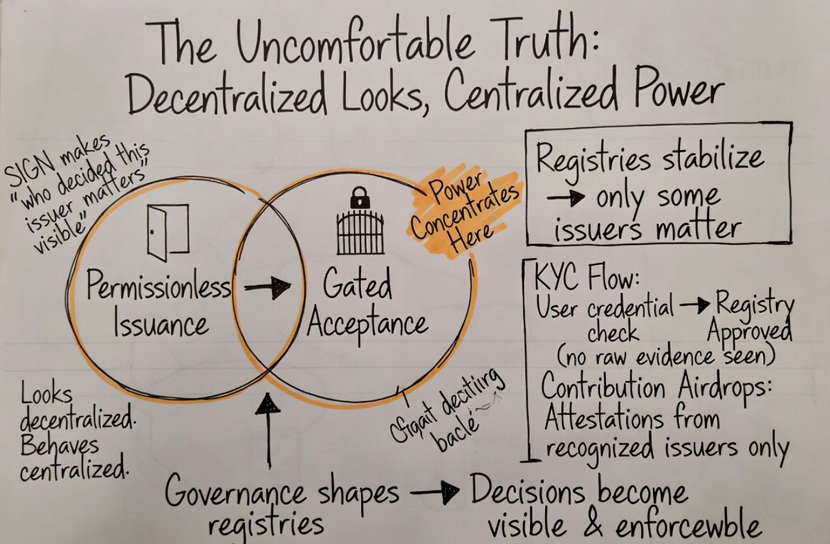
At this point, it stopped looking like a decentralized identity stack to me.
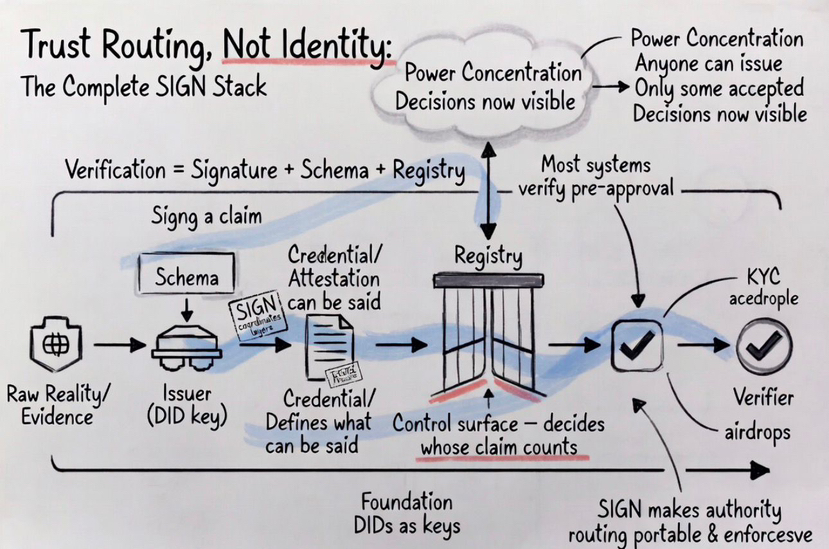
It started looking like a system for routing trust, not discovering it.
Schemas define what can be said.
Issuers decide who gets that statement.
Registries decide which issuers are relevant.
And everything downstream follows from that.
It looks decentralized because anyone can issue.
It behaves centralized because only some issuers are accepted.
This is why I don’t see SIGN as just an attestation tool anymore.
It’s closer to a coordination layer where meaning, authority, and acceptance are all linked. It doesn’t remove trust from the system. It reorganizes it into something that can be read and enforced across different environments.
But that also means something people don’t like to say out loud.
Once registries start stabilizing, power doesn’t disappear.
It concentrates often in the hands of those who shape registry governance, whether through on-chain voting, community processes, or institutional coalitions.
And that’s the part that makes this stack more real than most explanations.
Because now the question isn’t whether a credential is valid.
It’s not even whether the issuer signed it correctly.
It’s this:
who decided that this issuer should matter in the first place.
That’s where SIGN becomes important.
Not because it proves things.
But because it makes that decision visible on-chain, queryable and portable.
#SignDigitalSovereignInfra @SignOfficial $SIGN

