$SIGN #SignDigitalSovereignInfra @SignOfficial

I used to think identity systems fail because of weak tech. Poor UX, bad integrations, maybe scaling issues. That’s how most people explain it. But the more I’ve looked at real deployments, especially the ones tied to institutions and sovereign infrastructure, it doesn’t really fail there.
It fails earlier.
At who is allowed to issue, revoke and accredit. That part looks small from the outside. It isn’t. It kind of becomes the system itself.
And this is starting to matter more now, not less. Because systems are moving out of small experiments into actual usage. More partners, more regions, more rules. That’s exactly where issuer decisions stop being simple.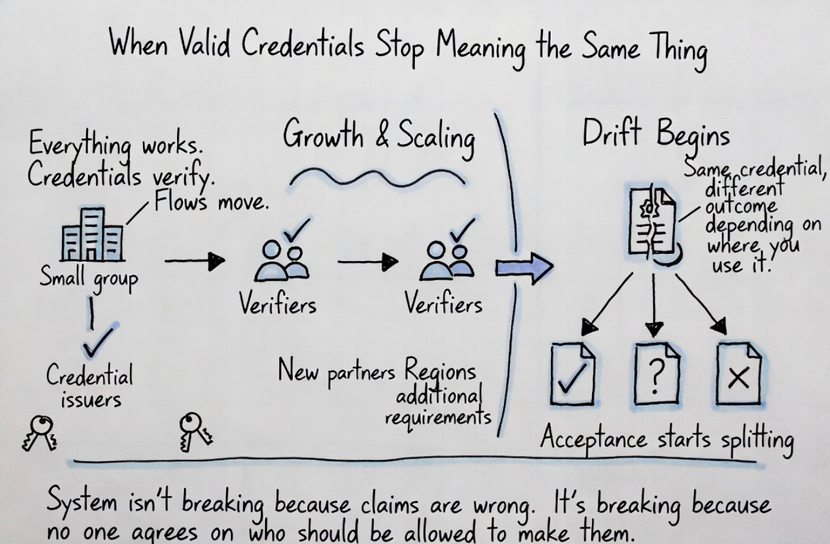
What kept bothering me is how these systems don’t fail immediately. In the beginning everything works. Credentials verify, flows move, nothing looks broken. But after some time, something just starts drifting.
The same credential doesn’t get accepted everywhere anymore. Different teams start trusting different issuers. And if you ask who should still be allowed to issue, there’s no clean answer.
That’s when it started to click for me. The system isn’t breaking because claims are wrong. It’s breaking because no one really agrees on who should be allowed to make them.
When I looked at Sign Protocol with that in mind, it stopped feeling like just another attestation setup. At first it looks clean.
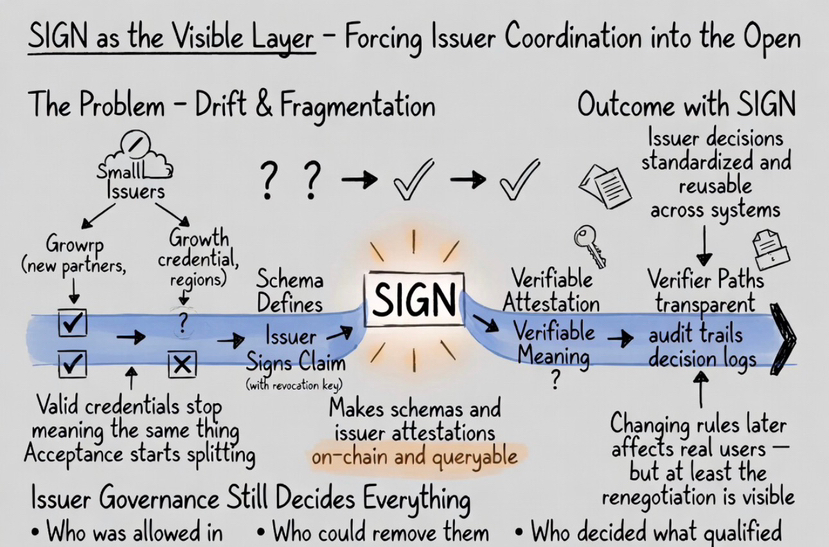
Schema defines the claim, issuer signs it, verifier checks it.
Done.
But the more I sat with it, the more I kept seeing the same flow underneath everything. Schema defines meaning, issuer is allowed to operate, claim gets created and then someone decides if that issuer still counts.
Once I noticed that, it was hard to not see it everywhere.
What caught me off guard is that defining a schema doesn’t just define data. It quietly shapes who gets to operate inside that meaning, who can lose that access later through revocation and how others decide to accept or ignore those claims.
SIGN doesn’t tell you who to trust. But it doesn’t let you ignore that question either. It forces the structure into the open by making schemas and issuer attestations on-chain and queryable. It standardizes how trust is expressed so different systems can rely on the same issuer decisions without re-checking everything again and again.
That’s why it started to feel less like a tool to me and more like a layer where these decisions just become unavoidable.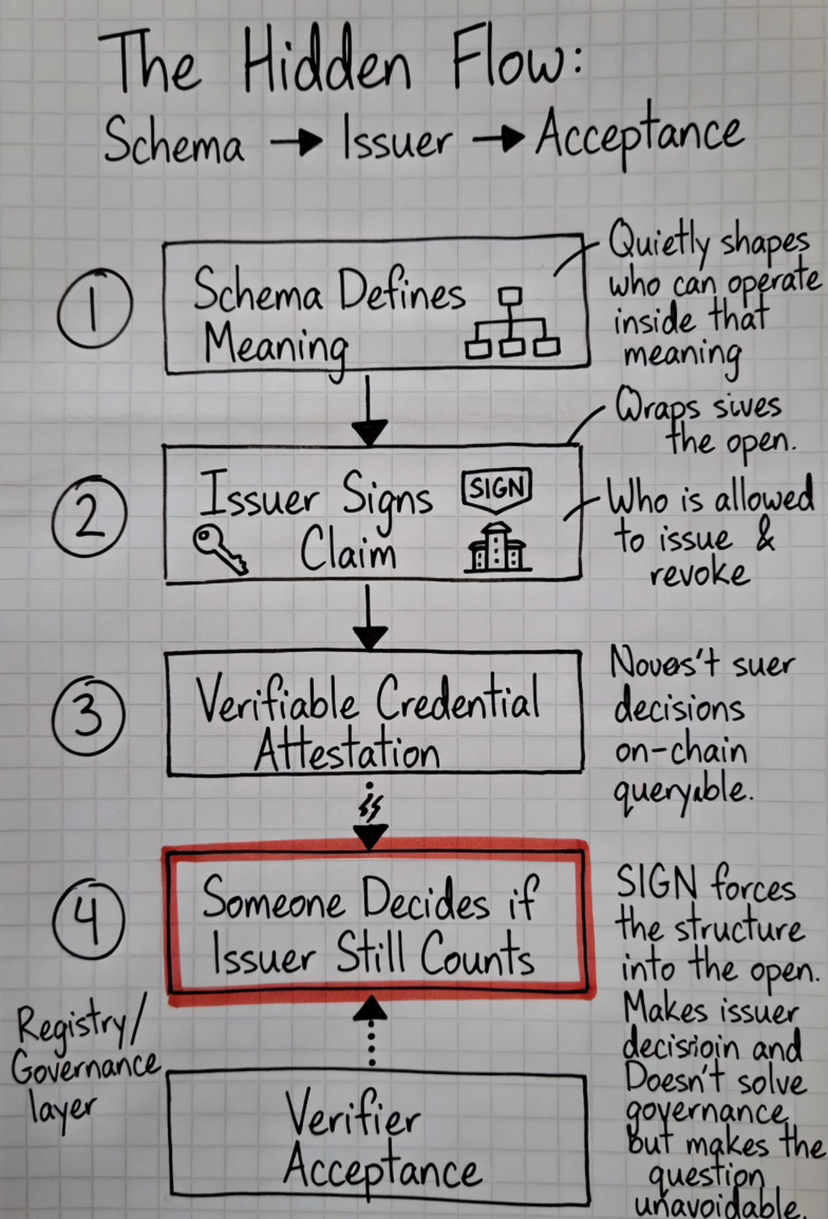
I’ve seen this play out in simple setups. A network starts with a small group of approved issuers and everything works fine. Credentials are consistent, decisions are easy, everyone trusts the same few sources.
Then it grows.
New partners come in. New regions. New requirements.
You can already see this starting to show up in newer systems. As soon as they scale even a little, issuer decisions stop being obvious.
Now suddenly you have to decide who gets added, who gets removed, who keeps their authority. And this is where it stops being clean.
Some parts of the system accept new issuers. Others don’t. Old issuers keep operating even when they probably shouldn’t anymore. Nothing really breaks on the surface, but acceptance starts splitting.
Same credential, different outcome depending on where you use it.
You see the same thing in airdrops and reputation systems. If a small group controls issuance, things stay consistent but narrow. If you open it up, low-quality signals start creeping in. Then projects start adding manual filters, off-chain checks, extra validation.
At that point, the on-chain credential isn’t enough on its own. It becomes just one signal among many.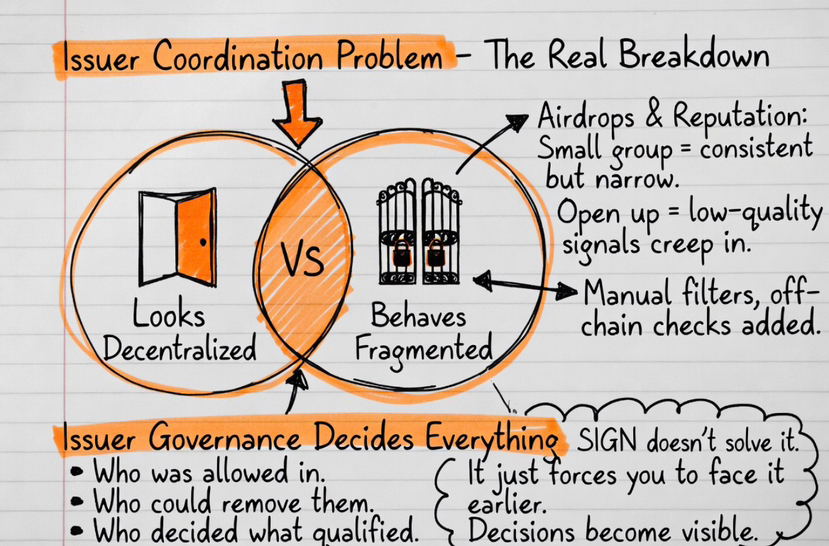
That’s when I stopped thinking of this as an identity problem. It looks like a credential system, but honestly it behaves more like an issuer coordination problem.
It still feels decentralized on the surface. Anyone can issue, anyone can verify. But in practice, only some issuers actually matter.
This is why issuer governance ends up deciding everything. Schemas define what can be said, issuers decide who gets that statement, and verifiers decide which issuers they accept. Everything else kind of follows from that.
And what really changed for me is realizing that SIGN doesn’t solve this part for you. It just forces you to face it earlier than most systems do.
Because once schemas are live and credentials are already in use, changing issuer rules later isn’t just a small update. It affects real users, real workflows, real decisions. You’re not just tweaking the system at that point, you’re basically renegotiating trust.
So now when people ask why identity systems fail, I don’t really look at the credentials anymore.
I look at the issuer layer.
Who was allowed in.
Who could remove them.
Who decided what “qualified” even meant.
Because if that part is weak, the system doesn’t fail loudly. It keeps producing valid credentials.
They just stop meaning the same thing to everyone.
And that’s usually where trust actually breaks.