@SignOfficial I think the most important thing Sign is trying to solve is not digital payments, digital identity, or even blockchain adoption in the abstract. It is the older and more stubborn problem underneath all of them: whether a government decision can still be proven, inspected, and trusted after the moment has passed. That matters now because digital public infrastructure is moving from theory into implementation, and OECD guidance has emphasized that governments need shared digital systems that are secure, interoperable, and usable across public services. In that setting, “proof” stops being a technical extra and starts becoming part of institutional credibility.
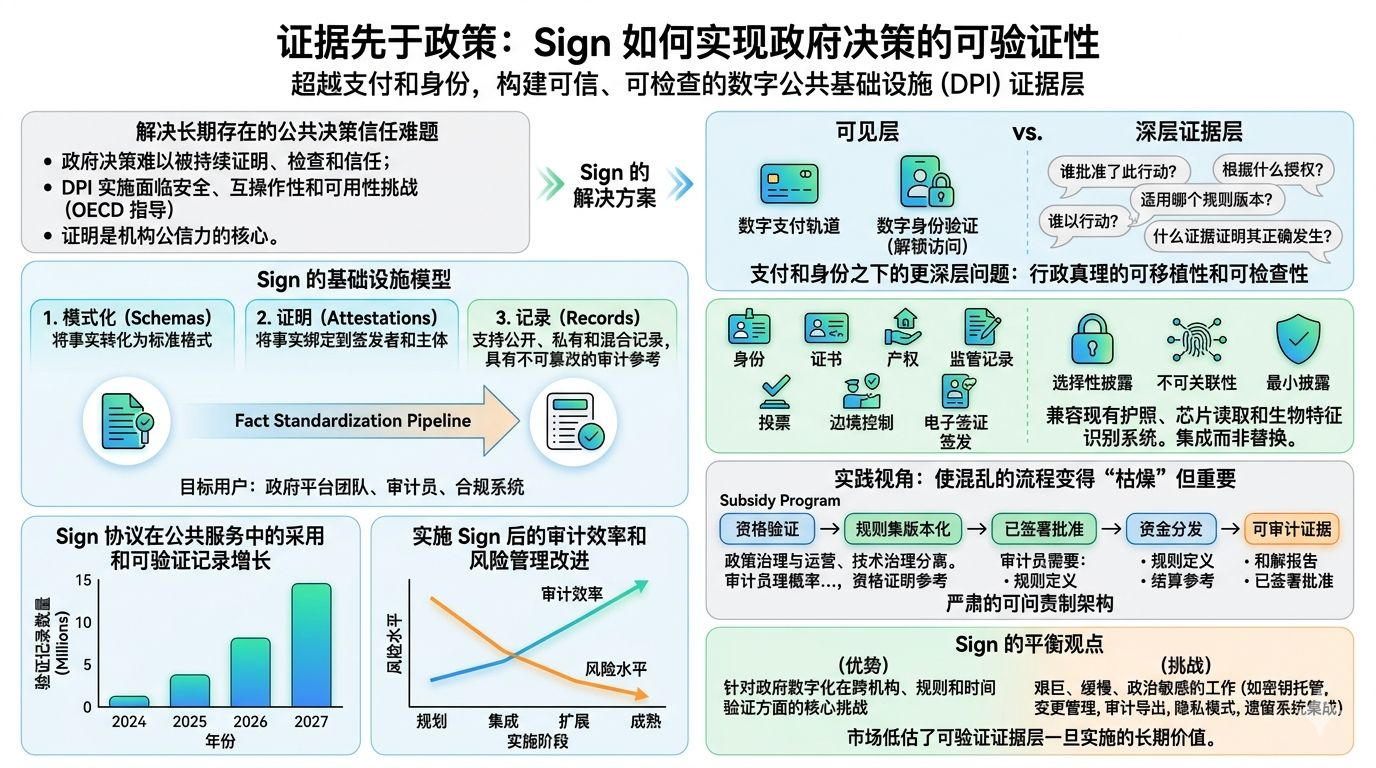
What I find compelling about Sign is that it defines itself as infrastructure, not as a consumer app. Its core idea is simple enough to explain without jargon: facts need a standard format, someone needs to sign them, and those records need to be queryable later. In Sign’s model, schemas standardize how a fact is expressed, attestations bind that fact to an issuer and subject, and the system supports public, private, and hybrid records with immutable audit references. The current product docs are explicit that this is meant for government platform teams, auditors, and compliance systems, which tells me the company wants to sit inside decision pipelines rather than on the marketing surface around them.
That framing matters because the market often overvalues the visible layer of government tech and undervalues the evidence layer underneath it. A payments rail can move money. A digital ID can unlock access. But the hard public-sector question is usually more mundane: who approved this action, under what authority, under which rule version, and what record proves it happened correctly? Sign’s broader documentation leans directly into that question. It describes the evidence layer as the place that answers who approved what, when it occurred, what ruleset version applied, and what proof supports eligibility, compliance, and settlement. To me, that is the real thesis here: Sign is trying to make administrative truth portable and inspectable.
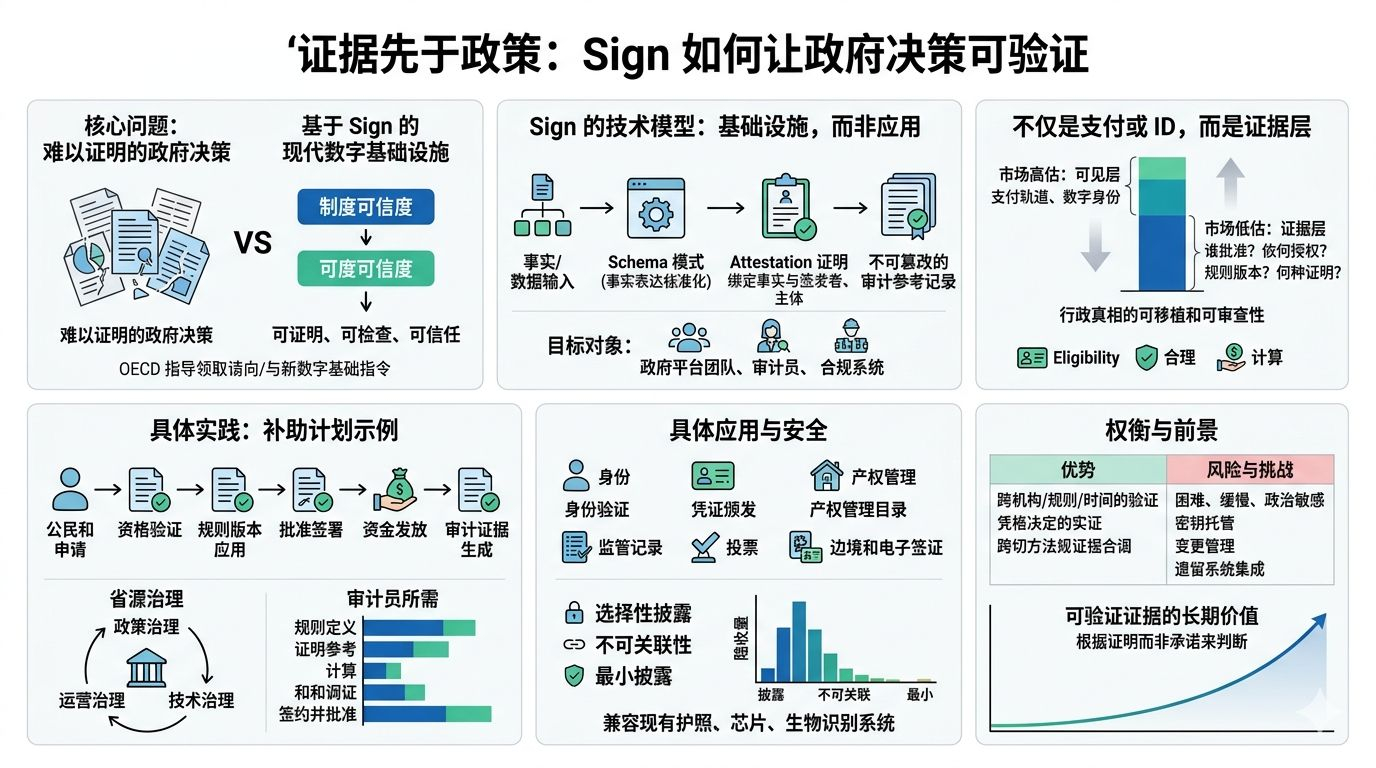
There has also been real progress in how concrete the product story has become. Sign is no longer speaking only in generalities about attestations. Its materials now map the protocol to specific government functions: identity, credentials, property rights, regulatory records, voting, border control, and e-visa issuance. The whitepaper also emphasizes selective disclosure, unlinkability, and minimal disclosure, which is crucial because government verification that exposes too much data can become its own failure mode. I also take seriously the emphasis on compatibility with existing passport, chip-reading, and biometric systems. That suggests Sign understands that public adoption will come through integration, not replacement theater.
If I were thinking about Sign from a practical market perspective, I would not judge it by headline excitement. I would judge it by whether it can make a messy workflow boring in the best way. Imagine a subsidy program: eligibility is verified, the rule set is versioned, approvals are signed, funds are distributed, and the resulting evidence can be audited later without rebuilding the whole case from emails and spreadsheets. Sign’s governance and operations docs are unusually clear on this point. They separate policy governance from operational and technical governance, and they specify that auditors need rule definitions, eligibility proof references, settlement references, reconciliation reports, and signed approvals. That is a serious architecture for accountability.
My balanced view is that Sign’s strength is also its risk. The strength is obvious: it is aimed at the exact layer where government digitization often breaks down, which is verification across agencies, rules, and time. The risk is that this is hard, slow, politically sensitive work. Key custody, change management, audit exports, privacy modes, and integration with legacy systems are not side issues; they are the job. In the short term, that can make progress look less dramatic than the market wants. In the long term, though, I think the market may be underestimating how valuable a verifiable evidence layer becomes once public systems are judged not by what they promise, but by what they can prove.
