Okay so I want to switch gears today and go a bit more technical. Not excessively technical. But technical enough to give you a real picture of what it actually looks like to build on @SignOfficial infrastructure rather than just reading the marketing descriptions. 🛠
Because I think there is a huge gap between how infrastructure projects describe themselves and what building on them actually feels like. And for $SIGN I think the actual developer experience is one of its genuinely underrated strengths.
Let me start with something that matters a lot to me personally as someone who has built on various blockchain platforms: the abstraction quality. When you are building for institutional or government use cases you do not want developers to be cryptography experts. Most enterprise developers are not and should not need to be. The infrastructure should abstract the complexity while preserving the guarantees.
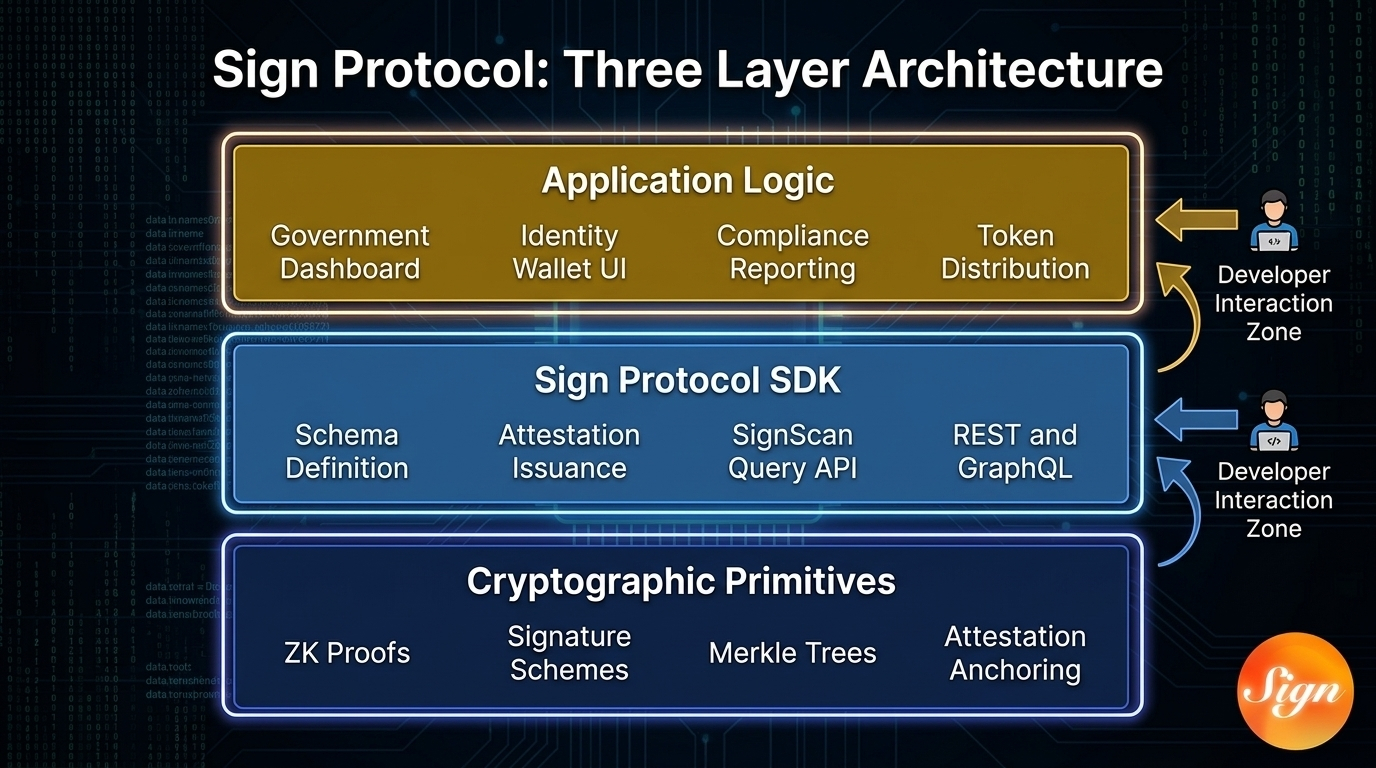
Sign Protocol does this through what I think of as a clean three layer model. At the bottom you have the cryptographic primitives. Zero knowledge proofs signature schemes Merkle trees for attestation anchoring. This layer is highly specialized and you do not need to touch it as an application developer.
In the middle you have the Sign Protocol contracts and SDK. This is where developers actually work. You define a schema for your data structure. You issue attestations using the SDK. You query existing attestations through SignScan's REST or GraphQL APIs. The SDK abstracts the cryptographic operations into clean function calls.
At the top you have your application logic. Your government program management interface. Your identity wallet UI. Your compliance reporting dashboard. This layer looks like any other web application because the SDK handles the blockchain interaction layer.
What I appreciate about this design is that it does not force you to be a ZK proof engineer to build something valuable on top of it. You define what facts you need to express. What level of privacy is required and the protocol handles the cryptographic heavy lifting.
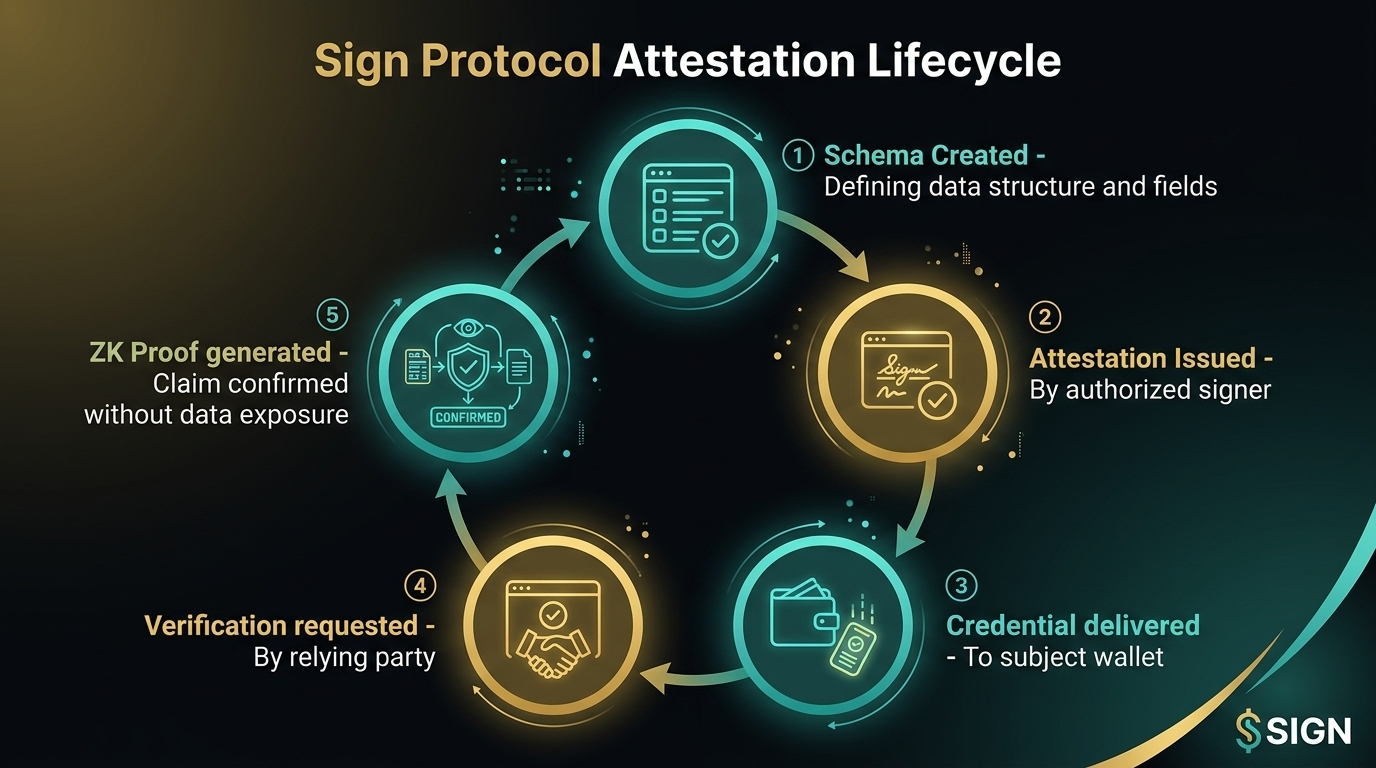
The attestation model specifically is elegant in its simplicity. A schema is just a structured template. Think of it like a JSON schema that defines the fields, types and validation rules for a specific type of claim. Once you have a schema you can issue attestations against it. An attestation says
"Here is a specific instance of this schema, signed by me, about this subject."
For a government identity use case this might look like a schema called Employment Eligibility with fields for employment status, sector, contract validity date and issuer identifier. An employment ministry issues an attestation for each worker using this schema. The worker carries their attestation in their digital wallet. Any employer or border system that needs to verify employment eligibility sends a verification request and gets back a signed confirmation without ever seeing the raw data fields.
This is genuinely useful. It is not just theoretically clever. I can imagine building this integration in a few weeks with a competent small team using the Sign SDK. And I say that having looked at how painful similar integrations are on platforms that do not have clean abstraction layers.
The cross chain aspect is also practically important for the Middle East context. Gulf nations are not going to standardize on a single blockchain. Different agencies will have different preferences. Some will use Ethereum based infrastructure. Some will use private Hyperledger deployments. Some will use newer sovereign chains. Sign Protocol's design allows attestations to be anchored across multiple chains and queried through a unified interface. This interoperability is not just a nice to have. It is essential for building infrastructure that works across a fragmented government technology landscape.
The querying infrastructure through Sign Scan is also worth highlighting. Being able to query all attestations of a certain schema type issued by a certain issuer about a certain subject within a certain time range gives compliance officers and auditors a genuinely powerful toolset. This is the kind of query capability that audit systems need and that most blockchain data structures do not naturally support.

Honestly the more I dig into the developer facing parts of Sign the more I feel like this was designed by people who have actually sat in rooms with enterprise clients and understood what those clients need in practice. Not just technically but operationally. The evidence artifact design the Trust Registry for issuer governance the schema versioning support. These are details that matter enormously in production deployments and they indicate a level of practical
sophistication that I respect.
If you are a developer in the crypto space and you have not looked at what @SignOfficial is building I genuinely think you are missing a significant opportunity. Not just to invest in $SIGN ut to think about what building on this infrastructure could enable. The application layer above this evidence and identity stack is wide open.
#SignDigitalSovereignInfra $SIGN

