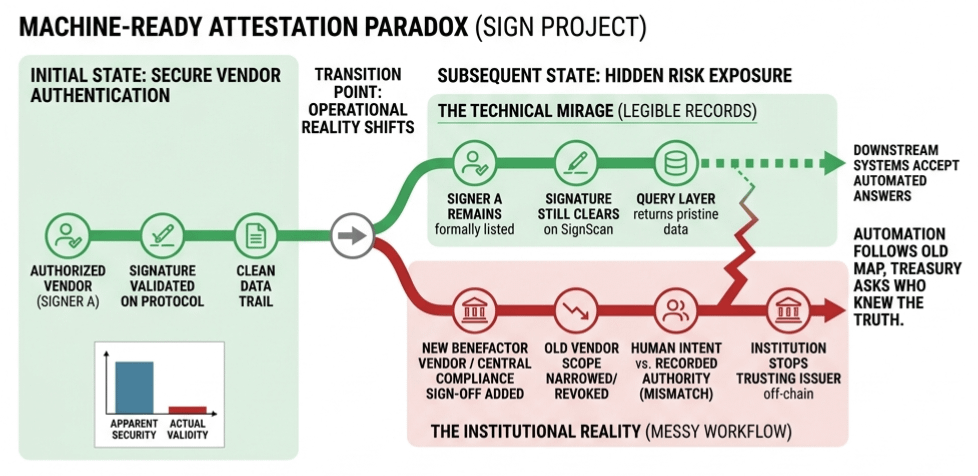
I was staring at a set of attestations on Sign the other day and realized we are still falling for the same old trap of confusing a clean trail with a current truth. It is the kind of technical mirage that makes sense on a screen but falls apart the second you step into a messy back office. The signer was formally there and the signature cleared perfectly on the protocol. SignScan showed the attestation exactly the way it was supposed to look and the query layer pulled it back without a single error. Everything looked pristine but the actual workflow had already stopped trusting that issuer somewhere off to the side as if the digital record did not even matter. It is a specific brand of stupidity where the schema is fine and the signature is valid but the institutional reality has already shifted into a completely different shape.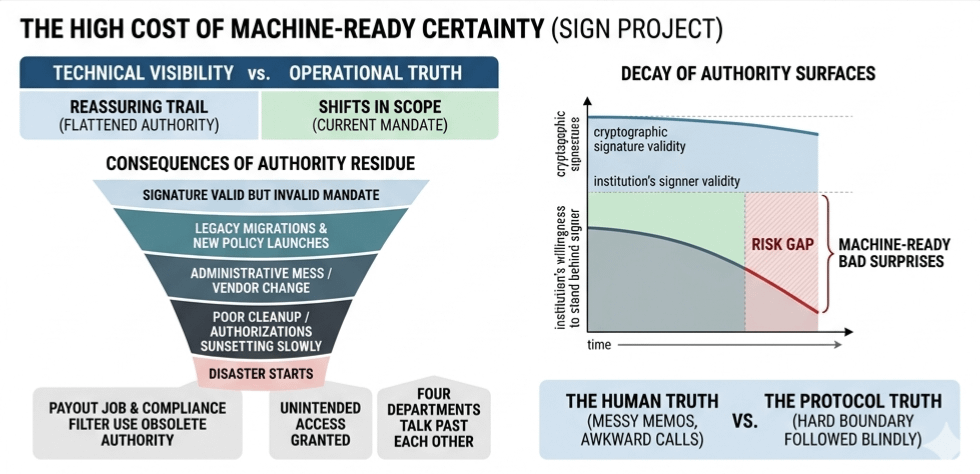
The setup usually starts out looking neat because someone has to be allowed to sign the thing or nothing moves. The program launches and the internal ops team keeps the approvals flowing through a specific vendor or a designated partner. It works well enough to get the records out and for a while the digital authority matches the physical intent. Then the institution does what institutions always do and they change the furniture. They bring in a new vendor or they narrow the scope of who gets to say yes. Maybe the original issuer was supposed to finish old cases but stay away from the new ones or maybe a second sign off got added to the chain while the old signer technically stayed listed on the registry. It is an administrative mess and the record on Sign just stays calm through all of it.
This is the ugly part of the transition from paper to protocol. An authorized issuer produces a signed record and leaves a clean trail which is incredibly reassuring if you are a downstream system looking for an automated answer. The problem is that the system is not a person trying to figure out if the answer still belongs to the correct version of the institution. We have this habit of flattening recorded authority and current authority into one thing the second a protocol makes the history look legible. Nobody is arguing with the history since the original permission was real and the schema relationship was valid. The disaster starts later when a payout job or a compliance filter reads that old authority as if it survived the vendor change or the new review boundary. It did not really survive but humans love moving the goalposts without updating the parts that the machines are programmed to read.
I have seen this play out in enough legacy migrations to know that the phrase machine ready is often just code for a bad surprise waiting to happen. Maybe the first issuer was a regional vendor handling early eligibility and then the institution tightened the screws and demanded central compliance sign off for everything. That is a better process on paper but if the old signer remains formally recognizable on the protocol because nobody closed the loop then the downstream systems will just keep moving. Why would they not. The record does not come back with a warning label saying this signer is only still alive on paper. It just comes back clean. Then the money moves or the access is granted and suddenly you have four different departments talking past each other while the treasury department asks who was actually supposed to know the truth from the data they were given.
It usually comes down to authority residue where the signature still clears even though the institution has become less willing to stand behind what that signer is doing. You want the traceability and the history that a protocol like Sign provides but you also end up with these old authority surfaces that look much safer than they actually are. Someone always says the signer will be sunset soon or assumes that the new cases will naturally stop flowing toward the old gatekeeper. They leave the permissions cleanup for the next sprint because the launch is more urgent and the records look fine enough for now. Then that old signer keeps showing up in records that verify perfectly and those records get used for things they were never meant to authorize.
The protocol is not wrong in these scenarios because it is only doing what it was told to do by recording the state of the world at a specific moment. The failure is entirely human because we mistake a clean issuer trail for a current mandate. It is always easier to trust the thing with the cryptographic signature than the thing with the messy memos and the awkward phone calls and the internal emails saying do not use them for new approvals anymore. We fail to translate that human language into a hard system boundary and then we act shocked when the automation follows the old map. It is the difference between a lighthouse that still shines its beam over a coastline that has already eroded away and a functioning harbor that actually knows where the ships are supposed to land.