I used to read that phrase and let it slide past me.
Verify once, reuse across chains and applications. It sounds clean. It sounds like a slogan. And slogans in crypto have a way of becoming meaningless through repetition before anyone stops to ask what they are actually describing.
So I sat with it longer than usual.
What Sign Protocol is describing is not a login system. It is not a credential wallet. It is something more specific and, I think, more structurally important than either of those things.
Sign Protocol's docs define attestations as portable, verifiable proofs that encode a statement, bind it to an issuer, and make it verifiable later. That last part — verifiable later — is where the real idea lives.
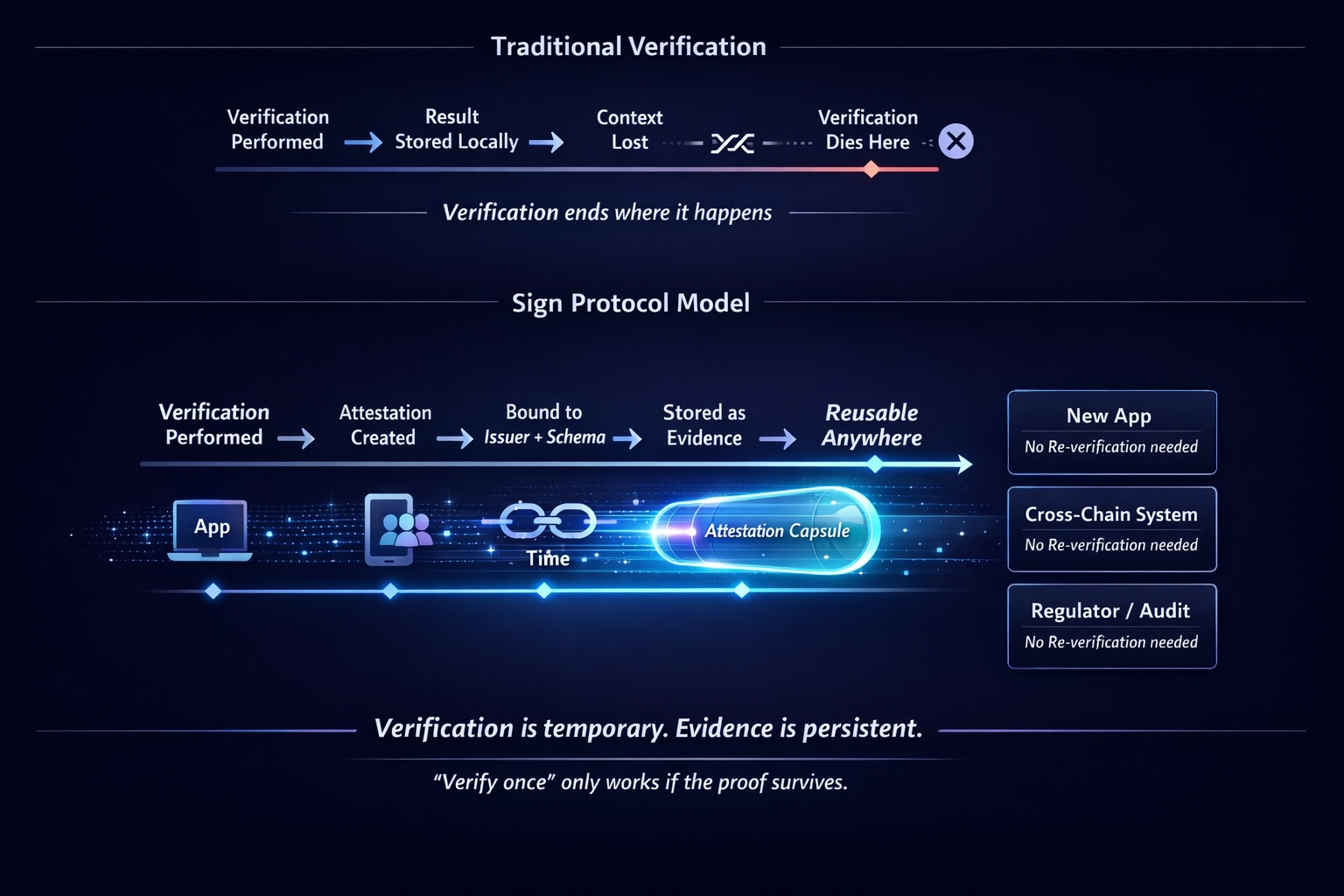
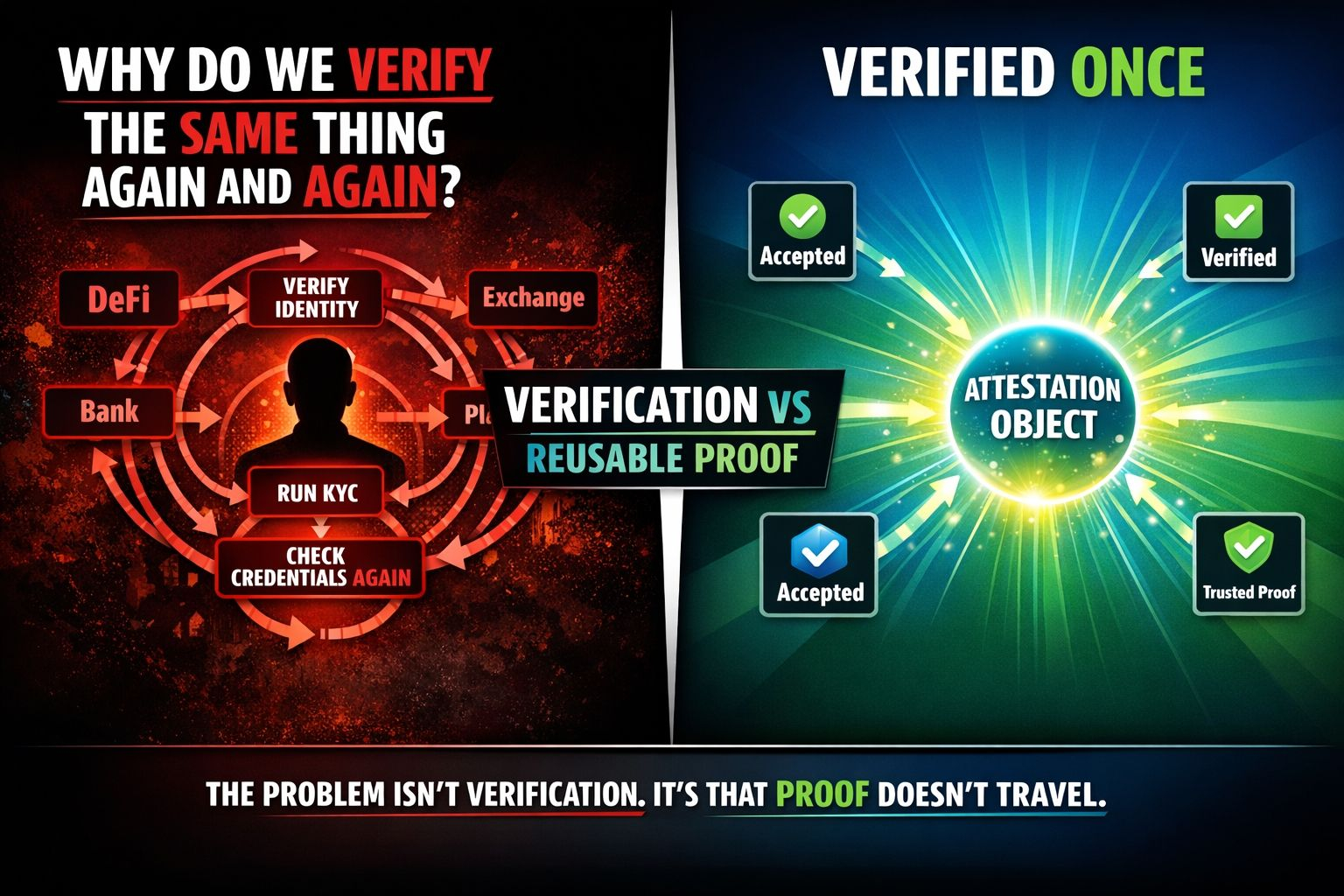
Most digital verification expires at the edge of the moment it happens. A system checks something. The check passes. The result lives inside that system and nowhere else. The next system that needs to know the same fact runs its own check from scratch. Not because it wants to. Because there is no shared format for the result to travel in.
That is the problem Sign Protocol is trying to solve at the infrastructure level.
Not by creating a universal database. Not by centralizing the credential. By standardizing the shape of the attestation itself — the schema, the issuer binding, the revocation status, the proof semantics — so that a verified fact can move between systems without losing meaning on the way.
EthSign started as a document signing platform. Number one contract signing app in Web3. Integrated with SingPass under Singapore's Electronic Transactions Act. Over 300,000 users. That is a real product with real adoption.
But the more interesting thing is what the team noticed while building it.
Every signed document is an attestation. Every signature is a structured claim that a specific party, at a specific time, under a specific context, consented to a specific thing. Once you see it that way, the question becomes obvious. Why should that claim expire at the edge of the document? Why can it not become a reusable evidence object that downstream systems can query without reconstructing trust from scratch?
That question is what became Sign Protocol.
And TokenTable followed the same logic from a different direction.
Token distribution is usually framed as a logistics problem. How do you get the right tokens to the right wallets at the right time. But Sign's docs are explicit that TokenTable is not just a distribution engine. It is a capital system that delegates evidence, identity, and verification back to Sign Protocol. Who qualified. Under which rule. Which credential counted. Which policy was active at the moment of distribution.
That evidence layer is Sign Protocol. TokenTable carries the distribution logic. Sign Protocol carries the proof underneath it.
That division of labor is quiet. It does not sound impressive at a product launch. But it means that every TokenTable distribution carries an auditable evidence trail that is structured, queryable, and inspection-ready — not reconstructed manually after the fact by a compliance team hoping the records are somewhere findable.
SignPass sits inside this same logic.
Reusable identities authenticated via SignPass can be utilized across multiple platforms and protocols without requiring each platform to run its own identity check from scratch. A credential issued once through SignPass travels with its issuer binding, its revocation status, and its proof semantics intact. The receiving system does not need to trust the user. It needs to trust the attestation format. And the format is Sign Protocol.
I am not saying this means verification is solved.
Reuse only works when the receiving application actually trusts the schema, understands the issuer model, and can interpret revocation and privacy modes correctly. A claim can move. Whether it remains useful without introducing new ambiguity in a new context is a harder question that Sign's architecture points toward but does not automatically answer.
That tension is real. And Sign's own docs acknowledge it directly. The path to real infrastructure is never linear.
But that acknowledgment is part of what makes the idea feel serious to me.
Sign Protocol is not promising that attestations will work everywhere. It is building the conditions under which they could — standardized schemas, omni-chain support across EVM, Starknet, Solana, and TON, Arweave-backed storage for long-term durability, and SignScan as the indexing layer that makes credentials queryable rather than just stored.
Verify once is not a feature. It is a design philosophy about what verified facts should be able to do after the moment of verification passes.
That is a quieter story than most crypto infrastructure tells. But it might be the more important one.