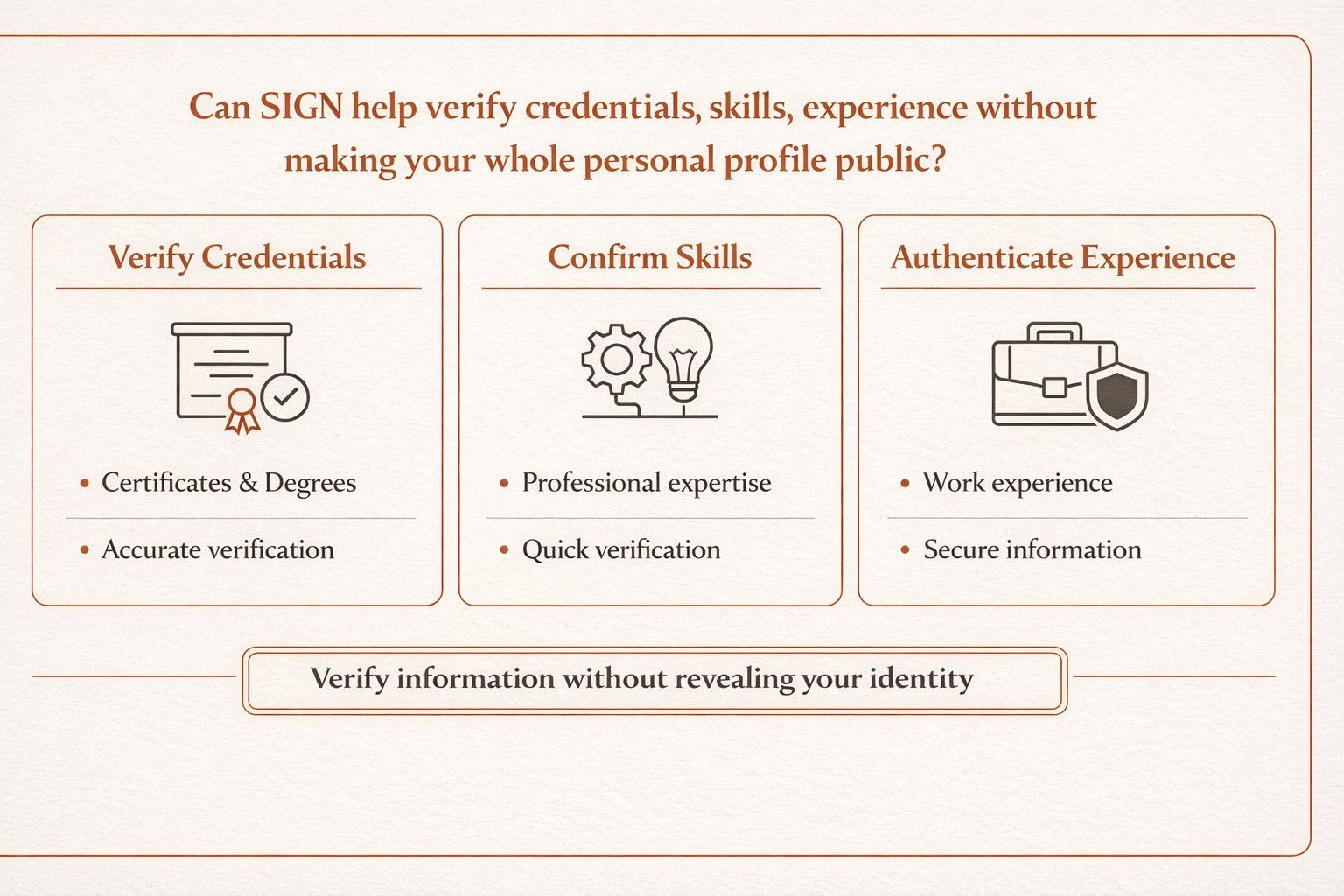
I sat down reading the docs of $SIGN until nearly 2 AM and there was one idea that made me stop for quite a while: perhaps what they are trying to build is not just an attestation protocol, but a way to prove qualifications, skills, and experience without having to publicize the entire personal record online.
In my view, this is the most noteworthy part of Sign 😀
Because in real life, often the app doesn't need to know everything about you. A recruitment platform doesn't necessarily need to see the entire educational history, every past job, or the complete personal record.
Often they just need to know that you truly have that degree, have that skill, or have had related work experience. If one still has to expose the entire profile just to prove such a small thing, then Web3 is actually still solving the trust problem in a rather crude way.
Sign is trying to go in the opposite direction: only presenting the necessary evidence while still maintaining the ability to verify and audit when needed. Their docs describe the Sign Protocol supporting public, private, and hybrid attestations, while emphasizing selective disclosure and privacy-preserving proofs as part of the evidence layer.
The point I find noteworthy is that Sign does not start from 'identity' in a pure sense, but from a claim that has been verified.
This is quite a significant difference. An identity system can tell you who you are. But in many real-world flows, what others need is not 'all of who you are', but a specific claim about you that has been verified by someone, according to which standard, and whether it is still valid.
Sign correctly addresses this part with schema + attestation + query/verification layer. The schema helps define what a type of claim should look like. Attestation is a record with a signature linking that claim to the issuer and the subject.
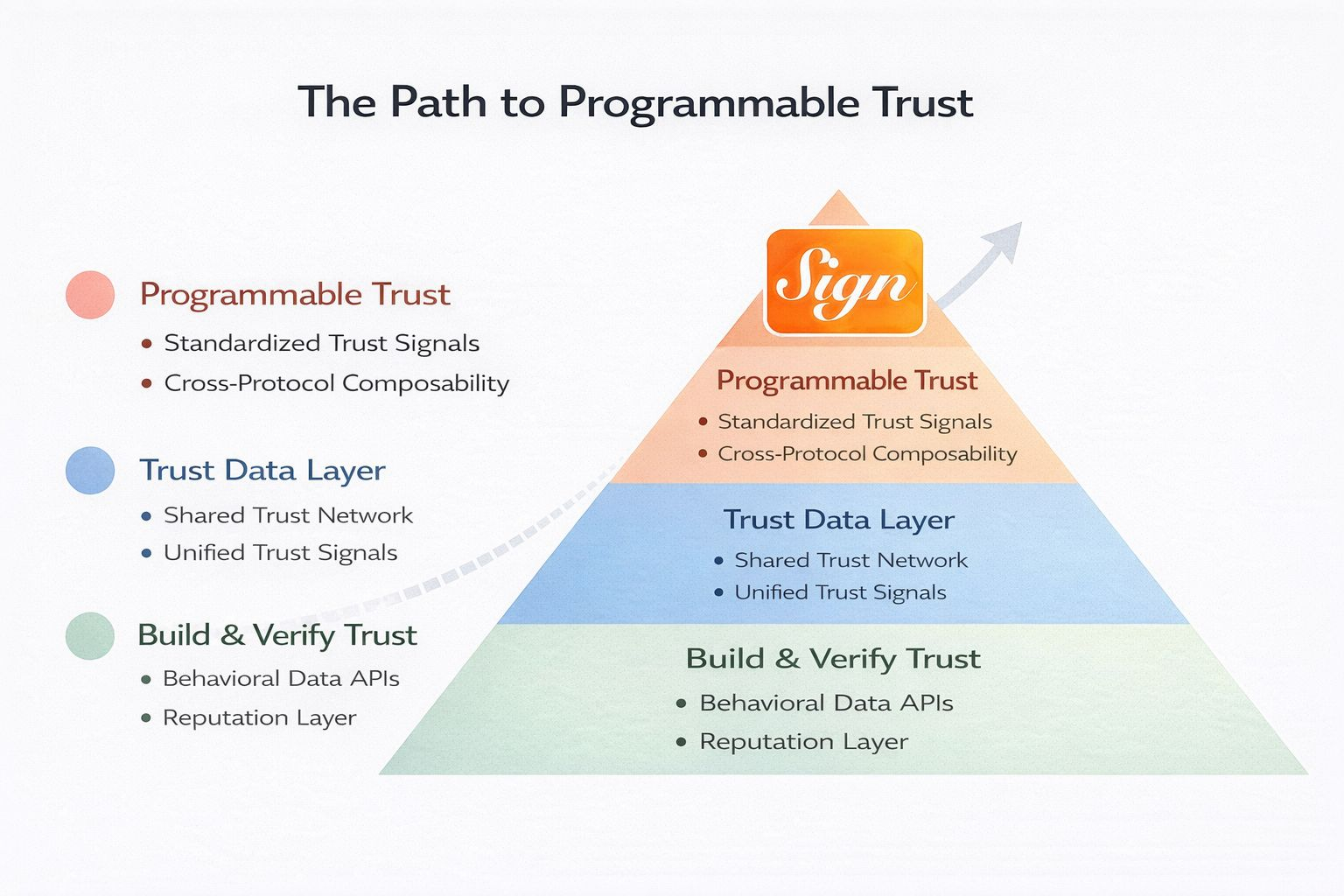
The query/verification layer allows third parties to verify without blindly trusting the backend of the issuing app. For me, this is a very suitable foundation for handling degrees, skills, and experiences in a way that 'proves just the necessary part'.
I think the strongest part of this thesis lies in the schema.
Because without a schema, every credential ultimately remains just signed data. It may be correct, but very difficult to reuse.
An educational app can define a degree in one format. A different recruitment app defines experience in another format. An onboarding app has its own KYC and skills logic. In that case, the data may be 'verified', but still not truly portable.
The schema in Sign is the encapsulation of the semantics of the claim: what this claim is about, what fields it has, who the issuer is, who the subject is, whether it can be revoked, and whether there are expiration conditions.
From my perspective, this is what allows a 'university degree', a 'skill credential', or a 'proof of work experience' to be understood according to a standard clear enough for other apps to reuse without having to build everything from scratch.
But the part where I find Sign truly interesting lies in selective disclosure.
This part is very relevant to the topic you asked about. If a person only needs to prove that they have graduated from university, it is not necessary to publicize the entire transcript, file number, date of birth, address, or other sensitive information.
If a person only needs to prove 'has skill X' or 'has worked in field Y', then the app does not need to see the entire CV.
The Sign docs emphasize that the protocol supports privacy-enhanced modes, including private attestations, hybrid attestations, and where appropriate, ZK attestations / privacy-preserving proofs.
For me, this is where Sign can stand between two seemingly contradictory sides: one side is the need for strong verification, and the other side is the need not to disclose the entire personal record.
Another point that makes me find this argument quite solid is that Sign not only cares about 'recording evidence', but also about how that evidence is used afterward.
Schema hooks are very clear examples. When an attestation is created or revoked, application logic can follow it. This is important because degrees, skills, or experiences are not just for showcasing a nice profile.
They are often inputs for access, hiring, eligibility, compliance, or participation rights in a certain flow.
If a skill credential is revoked, the app can block access. If a degree is verified to the required standards, another app can unlock a layer of features or workflows accordingly.
From my perspective, this is the moment Sign transforms the 'verified credential' from static data into actionable data.
I also see the multi-environment support of Sign very relevant to degrees and professional records.
Because things like education credentials, work experience, or certifications rarely exist neatly within one chain.
Sometimes original evidence should be off-chain or in decentralized storage because the data is lengthy, sensitive, or needs to be kept more private. The builder docs of Sign show that they support fully on-chain, fully off-chain payloads with verifiable anchors, and hybrid models.
From my perspective, this is a very practical point. A system that wants to handle degrees, skills, and experiences while insisting that everything must be public on-chain is almost impossible to sustain.
Sign seems to understand this, so they standardize the logic of evidence more than forcing all data to be absolutely public.
But I also don't think it should be overstated that Sign has solved this problem.
This is where I still want to keep some distance. A protocol with selective disclosure and privacy-preserving proofs does not automatically become a standard for credentials in the real world. For this to have real value, there must be at least three things.
First, the issuer quality must be strong enough. A degree is only valuable when the issuer is trustworthy. A skill credential only makes sense when the issuer truly has the authority to issue it.
Second, schema adoption must be broad enough. If each app defines 'work experience' or 'skill proof' in its own way, then portability remains weak.
Third, there must be real production flows where the verifier accepts reading just the necessary evidence instead of requiring the entire record.
From my perspective, Sign is building very correctly the primitives to make this happen, but real-world adoption is the decisive part.
So if you ask me if SIGN can help prove degrees, skills, and experiences without needing to publicize the entire personal record, the answer is quite clear.
They do not just provide you with a place to store a credential. They are trying to create a layer of evidence where the claim is clearly defined by a schema, issued by a trustworthy issuer, allowing for the appropriate level of disclosure, and then queried and verified by other apps without needing to pull out the entire record.
For me, this is a very correct direction.
But the real value of this thesis will only be revealed when there are many real issuers, many real apps, and many real flows that accept the kind of 'prove just the necessary part' rather than requiring users to expose their entire profiles to gain trust.