Habibies! Do you know? I used to think identity systems failed because they were outdated. Old databases, fragmented agencies, too much paperwork. It felt like a technical problem waiting for a better system. But the more I looked at how countries actually run identity, the more it became clear that nothing is truly broken in isolation. The system works, just not coherently.
That realization changes how you see everything.
Most countries are not starting from zero. They already operate a dense web of identity signals. A civil registry records births and deaths. A national ID assigns a number. Banks run KYC checks. Telecom companies verify SIM ownership. Border systems track movement. Welfare programs determine eligibility. Each piece works within its own logic, its own incentives, its own constraints.
The friction shows up in between.
That is where architecture starts to matter, not as a technical diagram but as a reflection of policy. Who is trusted. Who can ask for what. What gets recorded. What gets shared. What stays invisible. You begin to realize that identity architecture is less about databases and more about power moving through systems.
Three patterns keep appearing when countries try to make sense of this.
The first is the centralized instinct. It is understandable. If everything is messy, create one source of truth. One identifier. One system that everyone plugs into. It simplifies integration. It accelerates rollout. In some cases, it reaches tens of millions of users within a few years, which is not trivial at national scale.
On the surface, it feels clean. A bank integrates once and can verify identity instantly. A government agency no longer needs to reconcile multiple records. Reporting becomes straightforward because everything flows through one place.
But underneath, something else starts to form.
When a system makes data easily accessible, it does not stay minimal for long. A fintech app might legally need three data points to comply with regulation. Identity, age, address. But if the system returns fifteen fields at nearly zero cost, the incentive shifts. More data gets pulled, not because it is required, but because it is available.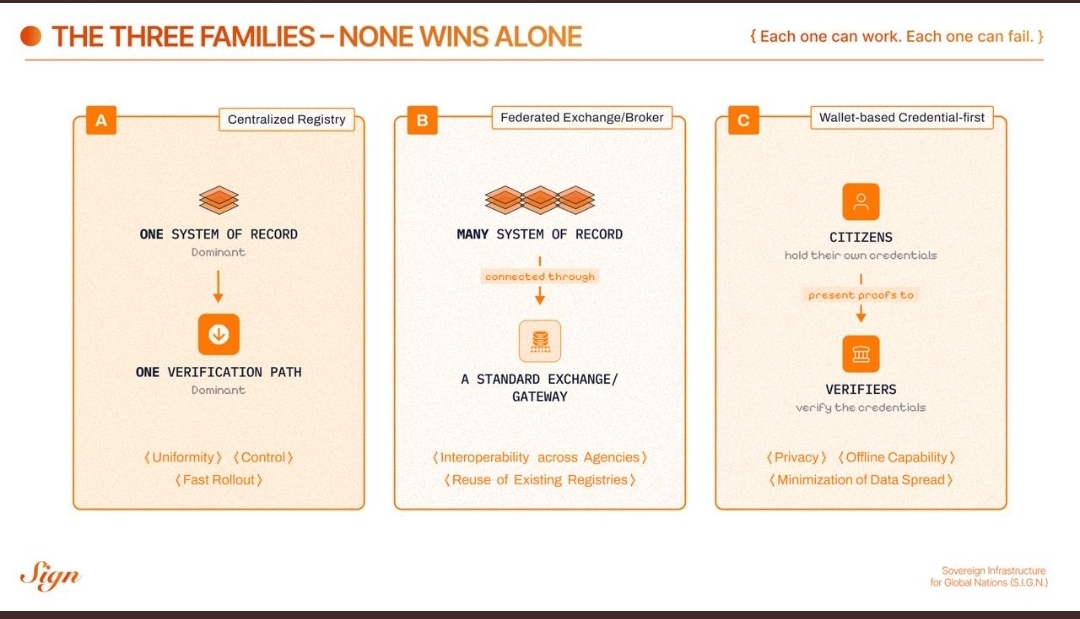
That is where behavior quietly changes.
A single onboarding request can expand into a full profile transfer. Name, birthdate, ID number, household links, sometimes even classifications that were never meant for commercial use. Each individual request feels justified. Over time, the system builds a shadow economy of replicated identities across private databases.
The risk is not just breach, although that risk scales with size. A centralized system serving 50 million users becomes a high-value target simply because of concentration. The deeper issue is that convenience rewrites boundaries. What started as verification becomes surveillance by accumulation, often without a clear moment where anyone decided that should happen.
That pressure leads some countries toward a different approach. Instead of forcing everything into one registry, they accept fragmentation and try to coordinate it.
Federated systems take the existing institutions as they are and connect them. Data stays where it originates. Agencies expose endpoints. A broker or exchange layer routes requests between them. It is more honest about reality. Ministries do not want to give up control of their data. They want interoperability without losing authority.
This model solves a different problem. It reduces duplication. It speeds up service delivery. A benefits system can verify income from tax records without rebuilding the logic itself. In practice, this can cut processing times significantly. If a claim used to take weeks due to manual checks, it can drop to days or even hours when systems talk to each other directly.
But again, what happens underneath is where it gets interesting.
Even if data is decentralized, visibility often is not. The exchange layer sees every request. Every authentication. Every interaction between agencies. It becomes a quiet observer of the entire system.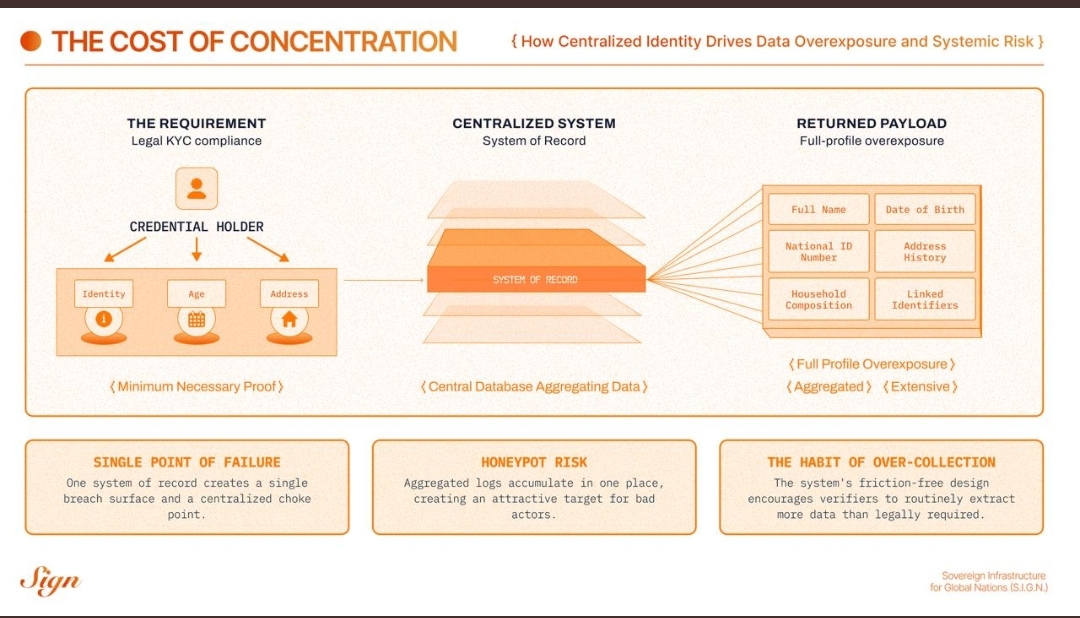
That visibility can be useful. Fraud detection improves when patterns are visible across domains. But it also creates a new concentration point. Not of raw data, but of behavioral data. Over time, it forms a map of how citizens interact with the state. When they apply for services. How often they authenticate. Which agencies they touch.
If that layer becomes critical infrastructure, everything starts to depend on it. Latency, outages, policy changes at the broker level can ripple across the system. What was designed as a connector can slowly become a gatekeeper.
Then there is the third model, which feels closer to how identity works in the physical world.
Instead of systems pulling data, individuals present proofs. Credentials are issued by trusted authorities and stored in a wallet. When needed, the person shares exactly what is required. Not a full profile, just a claim. Over 18. Resident of a specific region. Licensed for a certain activity.
On the surface, it feels almost too simple.
But the shift is deeper than it looks. It changes the direction of data flow. Instead of copying identity into every system, it allows verification without replication. A verifier checks the authenticity of a credential without needing to store the underlying data long term.
That enables something important. Data minimization becomes practical, not theoretical.
It also introduces new challenges. If 30 percent of users lose access to their devices at some point, which is not unrealistic over several years, recovery becomes critical. If revocation status is not updated frequently, a credential might appear valid when it should not be. If user interfaces are unclear, people might consent to sharing more than they intend.
These are not edge cases. They are operational realities.
And that is where the idea that one model will win starts to fall apart.
A country cannot rely entirely on centralization without risking concentration. It cannot rely entirely on federation without creating hidden chokepoints. It cannot rely entirely on wallets without building strong governance and recovery systems.
The pattern that keeps emerging is not replacement but layering.
Root identity often still comes from a centralized authority because initial trust needs a strong anchor. Interoperability still depends on federated connections because institutions are not going away. User-facing interactions increasingly move toward credential-based systems because they align with privacy and usability in real-world scenarios.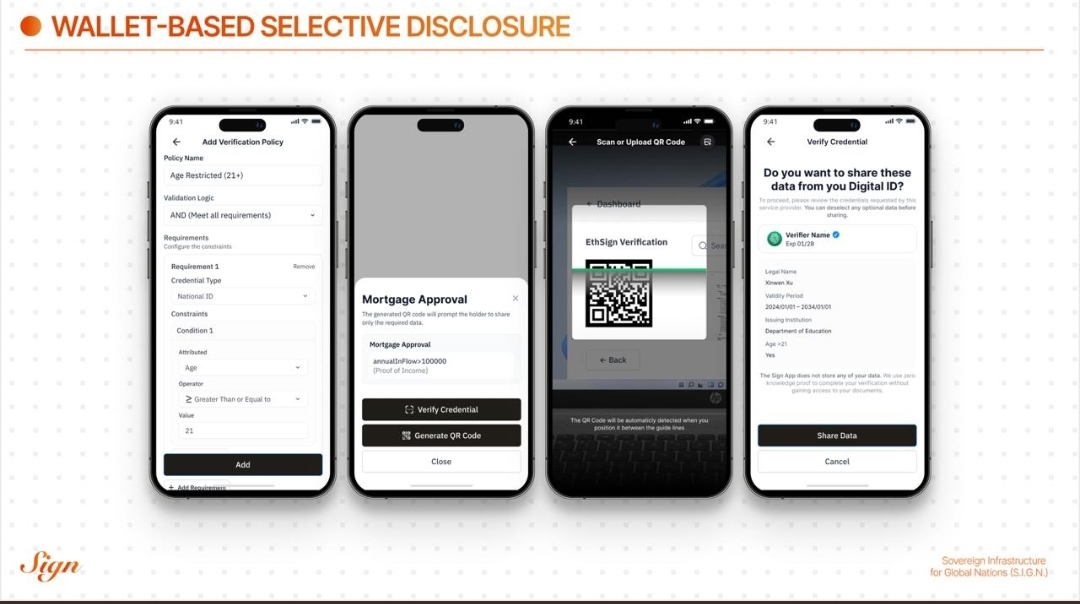
When you look at it this way, hybrid architecture is not a compromise. It is a reflection of reality.
What becomes interesting is the layer that connects these models. A verifiable credential layer starts to act as a bridge. It allows institutions to issue proofs without exposing full datasets. It allows individuals to present claims without revealing everything. It allows systems to verify without storing unnecessary data.
If this layer is designed carefully, it changes the incentives.
Instead of asking for everything because it is easy, systems ask for what is necessary because that is what is available. Instead of storing data for future use, they rely on proofs that can be revalidated. Instead of building larger databases, they build better verification logic.
That shift is subtle, but it compounds.
In markets right now, you can already see early signs. Digital identity projects are moving away from pure onboarding solutions toward reusable credentials. Regulators are starting to emphasize data minimization, not just data protection. At the same time, large-scale systems still rely on centralized anchors for assurance.
The tension between these forces is not going away.
If anything, it is becoming more visible. Countries are under pressure to digitize quickly, especially in areas like financial inclusion and cross-border services. But they are also under pressure to protect citizens from overexposure and misuse of data. Those two goals do not naturally align.
Architecture becomes the place where that tension is resolved.
Or ignored.
What struck me after spending time with these models is that failure rarely comes from choosing the wrong one. It comes from overcommitting to one logic and ignoring the others. A centralized system without constraints expands. A federated system without governance drifts. A wallet system without infrastructure collapses under real-world conditions.
The systems that seem to hold up are the ones that treat identity as a living structure. Something that evolves, but within boundaries that are clearly defined and enforced.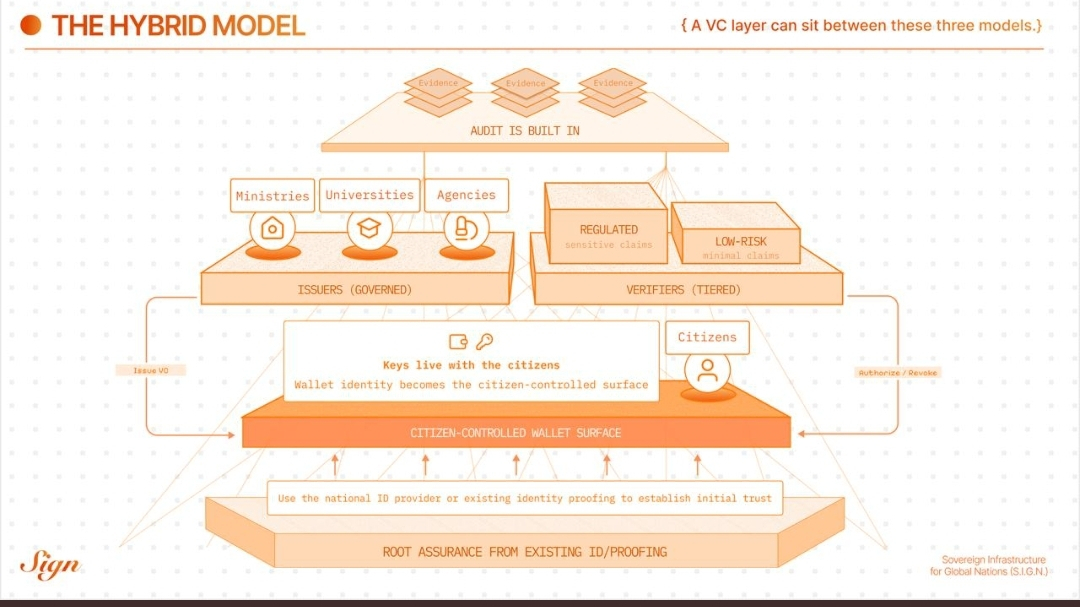
If this holds, the future of identity will not be about who owns the database. It will be about who controls the flow of proof.
And that is a quieter kind of power, but far more durable.
@SignOfficial #SignDigitalSovereignInfra $SIGN

