Hello everyone……. Imagine a world where proving who you are, sending money, and accessing services is as easy as unlocking your phone no stress, no long lines, no “please wait” moments.
Every country already has an identity system. The only question is whether it is coherent.
There is a fantasy that shows up in too many strategy decks: a country will “build a digital ID.” As if identity starts at zero. As if there is no history, institutions do not exist, and the first database solves the last mile.
Reality is harsher and more interesting.
Most countries already have a patchwork:
a civil registry,
a national ID card,
agency databases,
login providers,
benefits systems,
bank KYC files,
border systems,
and a lot of manual work that keeps the whole thing from falling apart.
Digital identity does not replace that overnight. It connects it.
So the core problem is architecture.
And architecture is policy, written in systems.
In practice, most national approaches cluster into three families.
The Three Families
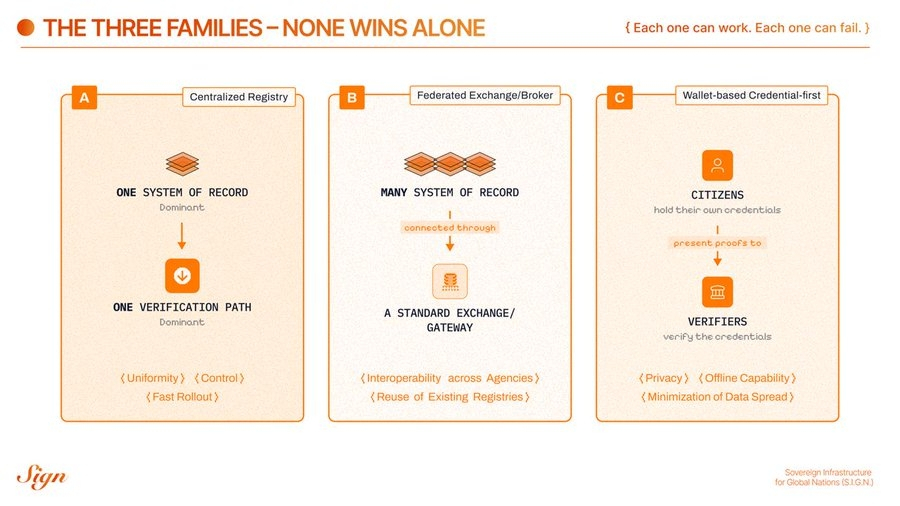
the three distinct models that are emerging
Each one can work.
Each one can fail.
None wins alone.
Let us walk through them, step by step.
Model 1: Centralized Registry
This is the simplest story.
One national system becomes the source of truth.
Relying parties integrate once.
Verifications flow through a central pipe.
Why governments choose it
It is easy to explain. It is easy to mandate. It can reach high coverage quickly.
However, it also feels like control, albeit sometimes that is the political goal.
Operationally, it can deliver:
a single identifier,
standardized onboarding,
consistent assurance levels,
straightforward reporting.
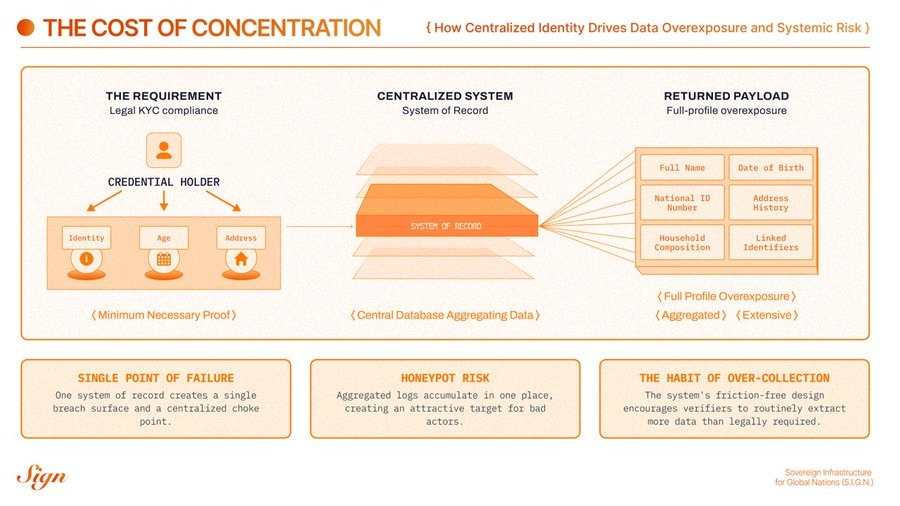
What it costs
The cost is concentration.
A centralized identity system becomes:
a single point of failure,
a single breach surface,
a single place where logs accumulate,
a single choke point that can be captured by bureaucracy, vendors, or politics.
It also tends to create a quiet habit, where every verifier asks for more than they need, because the system makes it easy.
Consider an everyday example where you register an account for a new app you just downloaded. Let’s say, a FinTech app.
The company needs to perform KYC.
Legally, it must confirm:
Your identity.
Your age.
Your address.
That is the compliance requirement.
In a centralized identity architecture, the app integrates with the national identity backbone for “verified onboarding.”
One authentication. The system confirms you are real.
But the integration does not return a narrow confirmation.
It returns the full identity profile tied to that identifier.
Full legal name.
Date of birth.
National ID number.
Address history.
Household composition.
Linked identifiers.
Possibly occupation or demographic classifications.
Now pause.
The company is legally required to perform KYC. It is commercially incentivized to understand its users. And the marginal cost of pulling more data is close to zero.
So what happens?
The company likes to have as much data on its customers as possible for possible advertising and its own monetization purposes. So, if the pipe is wide, it gets used. Not only for compliance. But for risk scoring. For cross-selling. For targeted advertising. For data enrichment. For resale to analytics partners where permitted.
The logic is simple: If companies have access to the full profile, they are incentivized to ingest the full profile.
Compliance becomes the justification.
Monetization becomes the motive.
Architecture makes it effortless.
From the citizen’s perspective, opening an account becomes the moment their entire civic identity can be mirrored into a private database.
Not because anyone broke the rules. But because the system delivered abundance instead of minimum necessary proof.
That is how centralized identity quietly feeds commercial profiling.
Not through abuse.
Through incentives.
And that is how privacy dies. Not with malice. With convenience.
The predictable failure mode
This system is also prone to failures, like data breaches. The predictable failure mode is a national honeypot.
When everything routes through one place, that place attracts:
attackers,
insiders,
and mission creep.
So, although the system might be efficient, it becomes fragile and even harmful for citizens.
Model 2: Federated exchange or broker
This model starts from a more honest premise. Agencies already own data. They will keep owning data. So, they do not pretend there will be one registry.
Instead, they build a standard exchange layer, build an interoperability fabric, and let systems talk with clear rules.
The shape varies. Some countries use a secure data exchange backbone; others use a centralized API gateway for private sector access; and others use federated identity providers with contracts and assurance levels. But the logic is the same.
Keep systems where they are.
Connect them safely.
Why governments choose it
This system respects institutional reality.
It can reduce duplication because agencies stop rebuilding the same verification logic.
It can speed up services because data flows become standardized.
It also maps well to program delivery.
A benefits agency does not want to build a new identity stack. It wants eligibility, payment rails, and audit. Federation can deliver that faster.
What it costs
the cost of power concentration
The cost is governance.
Federated exchange is never only technical.
It is always political and operational.
You need to define:
who is allowed to call which endpoints,
what legal basis applies,
how consent is captured and recorded,
how logs are retained,
who pays for integration and uptime,
what happens when systems disagree.
And because data still moves server to server in many broker models, you often still get centralized visibility.
Sometimes you need it.
Sometimes it becomes surveillance by default.
Let’s do a short example here. Consider applying for unemployment benefits through a digital identity broker.
You authenticate once, and the broker routes verification requests between the labor agency, tax authority, and civil registry.
Each agency only sees what it needs. But the broker sees everything.
Every login.
Every verification request.
Every agency interaction.
Every timestamp.
The agencies are decentralized.
The visibility is not, which gets kind of annoying and invasive for users.
Sometimes that centralized view is necessary for fraud detection.
Sometimes it quietly becomes a comprehensive map of a citizen’s interactions with the state.
The predictable failure mode
The predictable failure mode is a gateway that turns into a bottleneck.
A well-intentioned exchange layer can quietly become a new monolith. Not because it stores all data, but because everything depends on its uptime, its contracts, and its change approvals.
If your interop layer is not designed for scale and exceptions, it will slow the country down.
Model 3: Wallet-based, credential-first
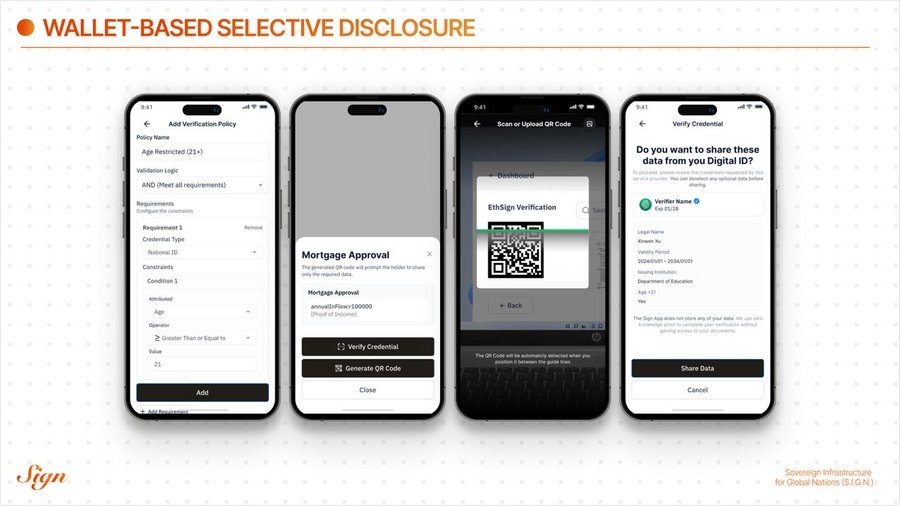
Sign's VC model
This model flips the direction of verification.
Instead of verifiers pulling data from databases, citizens present proofs from a wallet.
Authorities issue credentials.
Citizens hold them.
Verifiers request what they need.
The wallet shows the request in plain language.
The citizen consents, or refuses.
The verifier verifies authenticity and status.
It is direct. It is local. It is closer to how the physical world already works.
Why governments choose it
Because it is the cleanest path to data minimization.
Wallet-based systems can:
reduce the spread of personal data,
support offline checks (critical in real queues),
make consent visible and meaningful,
let the same credential be reused across agencies and regulated partners.
It is also, quietly, a sovereignty move.
If a country defines a credential layer and trust framework, it can evolve applications without rewriting the foundations.
What it costs
The cost is maturity.
Wallet systems force you to solve hard, real-world issues early:
relying party onboarding (who is allowed to request what),
device loss and recovery,
revocation freshness (what works offline, what requires online checks),
user experience that does not confuse or scare people,
consistent schemas across sectors.
If you ignore these, you get a beautiful pilot that collapses the first time a phone is lost.
The predictable failure mode
The predictable failure mode is a privacy story with no operational spine.
If wallets exist without a strong trust registry, without clear verifier authorization, and without inspection-grade evidence, you get chaos.
Everyone asks for everything.
No one can prove what happened later.
Auditors do not trust it.
Regulated partners do not adopt it.
Then the old database calls “come back.”
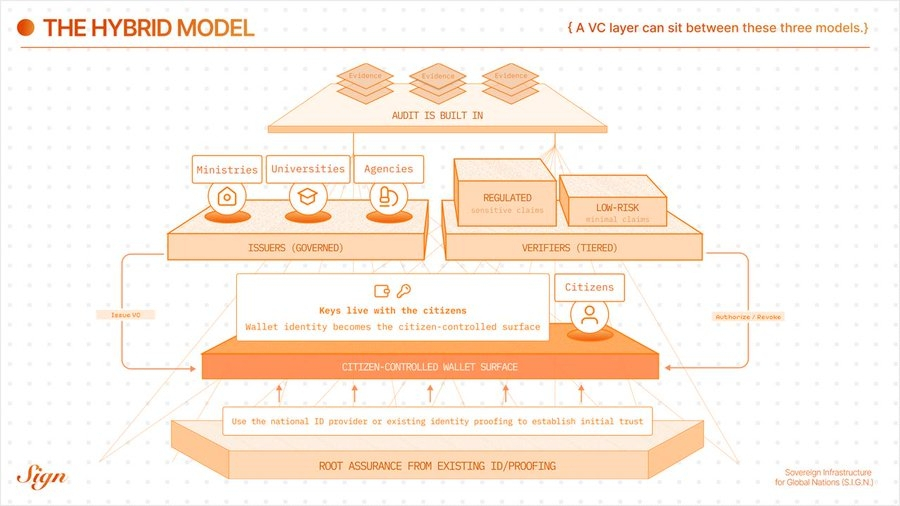
So why does none of this win alone?
Most countries adopt one mode, but unfortunately, the reality is that countries do not live in one mode.
A country needs:
centralized capabilities for governance (trust lists, schema approval, emergency powers),
federated capabilities for inter-agency reality (existing registries, existing authority boundaries),
wallet capabilities for consent and minimization (citizen control, offline checks).
Even the most wallet-forward designs still need a shared trust layer.
Even the most centralized systems still need interoperability.
Even the best exchange fabrics still need a better way to prove facts without copying databases everywhere.
This is why hybrid approaches are not a compromise.
They are an inevitability.
The bridge: a verifiable credential layer
A VC layer can sit between these models. It can let countries keep what works and fix what does not.
A practical hybrid often looks like this:
Root assurance stays where it already is. Use the national ID provider or existing identity proofing to establish initial trust.
Wallet identity becomes the citizen-controlled surface. Keys live with the holder. Credentials live with the holder.
Issuers are many, but governed. Ministries, regulators, universities, banks, and agencies can issue credentials under an explicit authorization chain.
Verifiers are tiered. Low-risk verifiers get minimal claims. Regulated verifiers get sensitive claims, with higher onboarding rigor.
Status and trust are shared. Revocation and authorization are distributed to verifiers through cached lists and periodic sync.
Audit is built in. Governance actions and key events produce standardized evidence, without centralizing raw citizen payloads.
It is not hype.
It is plumbing.
Good plumbing disappears.
Bad plumbing becomes politics.
How to choose your starting posture
Countries rarely choose one model outright.
They choose a starting posture, then evolve.
Here is a grounded way to decide where to start.
Start more centralized when
you need fast national coverage,
institutions are fragmented and need a strong initial coordination point,
the private sector needs one simple integration path to begin adoption,
you can enforce strong oversight and limitation on data access.
Start more federated when
agencies already have strong registries that will not be merged,
your biggest pain is duplication of verification and slow data exchange,
you need interoperability without rewriting every system of record.
Start more wallet-forward when
privacy and minimization are explicit national requirements,
offline verification matters (border, mobility, inspections, queues),
you want a durable identity layer that outlives any one vendor or gateway,
you are willing to invest in relying party onboarding and recovery design early.
Common mistakes to avoid
These are the mistakes that show up again and again.
Treating identity like an app.
Identity is infrastructure. It needs governance, operations, and evidence.
Centralizing raw data for convenience.
Convenience becomes breach surface. It also becomes mission creep.
Ignoring verifier authorization.
If anyone can request anything, the system will leak.
Ignoring recovery.
Phones get lost. Keys rotate. Institutions change names. Plan for it.
Building audit after launch.
You cannot retrofit trust in a scandal.
The simple ending
A country does not need a perfect architecture.
It needs a coherent one.
The best identity systems do three things:
they scale under national load,
they minimize unnecessary exposure,
they produce evidence that holds up under oversight.
Centralized systems deliver uniformity.
Federated systems deliver interoperability.
Wallet systems deliver minimization and consent.
You will need all three instincts.
So build the bridge.
Govern the trust fabric.
Make privacy controllable.
Make verification cheap.
Make audit real.
Then the rest can evolve.
That is sovereignty in practice.
A note on SIGN
SIGN does not argue that one national identity architecture should replace all others.
We work on the layer beneath that debate.
Our focus is the trust fabric that allows different institutions to issue, verify, and govern credentials without forcing every interaction through a single database or invisible broker.
In practice, that means designing:
Clear issuer governance, so authority is explicit and auditable.
Selective disclosure by default, so verifiers receive facts, not files.
Revocation and status infrastructure that works under real national conditions.
Evidence standards that produce audit trails without creating surveillance trails.
We believe architecture should encode policy, not bypass it. A centralized registry can exist. Sector systems can exist. Private operators can exist. But the trust layer should ensure that proof travels while payloads do not, and that visibility is deliberate rather than accidental.
Digital identity will never start from zero.
The question is whether it evolves toward concentration or toward structured, accountable trust.
@SignOfficial builds for the latter.
