Today I realized that I am troubled by the issue of verification and identification, namely its security and ultimate intent. From verification at the state level, banking to the primitive downloading of applications on the phone.
In every country there is already an identification system. The question is whether it is comprehensive.
In most strategic documents, there is such an illusion when a country 'creates a digital identifier'. Supposedly identification starts from scratch. Supposedly there is no history, no institutions, and the first database will solve all the problems.
Reality is harsher and more interesting.
Most countries already have a mosaic, it is:
registry of civil status acts;
national identification card;
agency databases;
login providers;
social welfare systems;
KYC bank files;
border systems;
and a lot of manual work that prevents all this from falling apart.
Digital identification will not replace this overnight. It connects this.
So... the main issue is the architecture. And it is.
And the architecture is the policy written into the systems.
In practice, most national approaches are grouped into three categories.
Each of them can work.
Each of them can fail.
No one wins alone.
Let's consider them one by one, step by step.
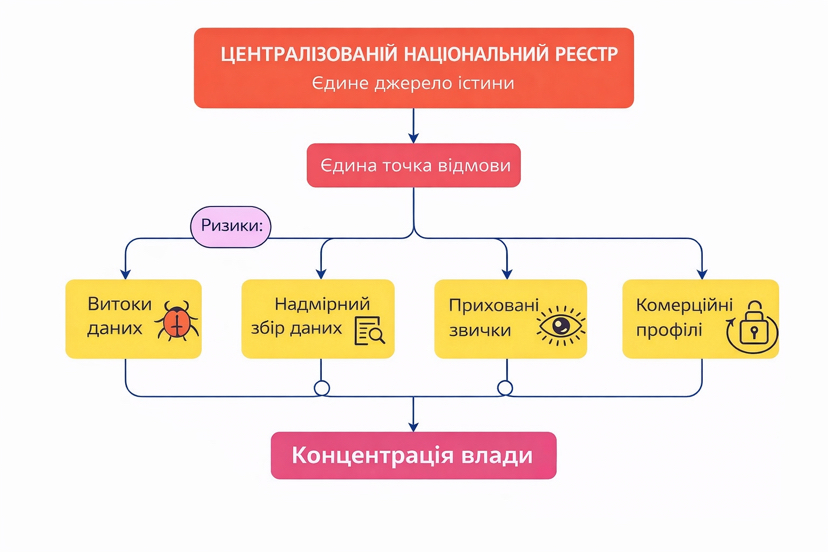
Let's talk about the CENTRALIZED REGISTER
This is the simplest option.
One national system becomes a source of truth. Parties relying on it are integrated once.
Verifications go through the central channel.
Why do governments choose this? Because. It is easy to explain. It is easy to implement. It allows for rapid high coverage. However, it is also perceived as control, although sometimes it is a political goal.
From an operational point of view it can provide:
unique identifier;
standardized onboarding procedure;
consecutive levels of guarantees;
simple reporting.
But what is the price for all this good?
The price is concentration!
A centralized identification system becomes:
the only point of failure;
the only plane for breaks;
the only place for log accumulation;
the only bottleneck that can be influenced by bureaucracy, suppliers, or politics.
It also fosters the formation of a hidden habit, where each verifier requires more than they need, as the system simplifies this.
Let's consider a daily example when you register an account for a new app that you just downloaded, any.
The company must conduct a KYC procedure. A common thing.
According to legislation, it must confirm:
Your identity.
Your age.
Your address.
This is a requirement for compliance with regulations.
In a centralized identification architecture, the application integrates with the national identification database for 'verified registration'.
One verification. The system confirms that you are a real person.
But integration does not return limited verification.
It returns the full identity profile associated with this identifier.
Full official name.
Date of birth.
National ID number.
Address history.
Household composition.
Related identifiers.
Perhaps profession or demographic classifications.
And now let's stop. And think about this once again. Just imagine. Oh my.
The company is legally required to conduct a KYC procedure. From a commercial point of view, it is beneficial to understand its users. And the marginal cost of collecting additional data approaches zero.
So what is actually happening?
The company seeks to have as much data as possible about its customers for potential advertising and its own monetization goals. So if the channel is broad, it is used. Not only for compliance. But also for risk assessment. For cross-selling. For targeted advertising. For data enrichment. For reselling to analytical partners where permitted.
The logic is simple: if companies have access to the full profile, they... obviously... are interested in obtaining the full profile.
Compliance becomes a justification.
Monetization becomes a motive.
Architecture makes this easy.
From the citizen's perspective, opening an account becomes the moment when all of his civic identity can be reflected in a private database.
Not because someone broke the rules. But because the system provided excess instead of the minimally necessary evidence.
This is how the centralized identification system subtly contributes to the creation of commercial profiles.
Not due to abuse.
And through incentives.
And this is how privacy dies. Not out of malice. But out of convenience.
Predictable failure mode.
This system is also prone to failures such as data leaks.
When everything passes through one place, that place attracts:
malefactors;
insiders;
and expanding the boundaries of the mission.
So, although the system may be effective, it becomes vulnerable and even harmful to citizens.
The architecture must consider the policy, not circumvent it. A centralized registry can exist. Sectoral systems can exist. Private operators can exist. But the level of trust must ensure that evidence is transmitted, and useful data is not, and that the availability of information is targeted, not random.
Digital identification will never start from scratch.
The question is whether it will develop towards concentration or towards structured, accountable trust.

and the more I appreciate the true sovereign essence of the concept @SignOfficial the clearer I understand that the project builds an independent infrastructure for creating, storing, and verifying any digital evidence#SignDigitalSovereignInfra 👏$SIGN ✨