I keep coming back to one thought with Sign: most people are still looking at it too narrowly.
They see attestations, signatures, credentials, and assume that is the full story. A claim gets issued, a fact gets verified, a user proves something, and the job is done. Useful, sure. But that reading feels too small to me. The more I sit with Sign, the more I think its real ambition is not about proving a fact once. It is about stopping that proof from becoming trapped in the first place it was created.
That is the part I find genuinely important.
Digital systems waste an unbelievable amount of effort re-checking the same reality again and again. One app wants identity proof in one format. Another wants eligibility proof in a different one. A third needs compliance evidence, but cannot directly use what already exists because the chain is different, the data structure is different, the storage is different, or the trust model does not carry cleanly. We call that normal system design, but honestly it is just fragmentation with better branding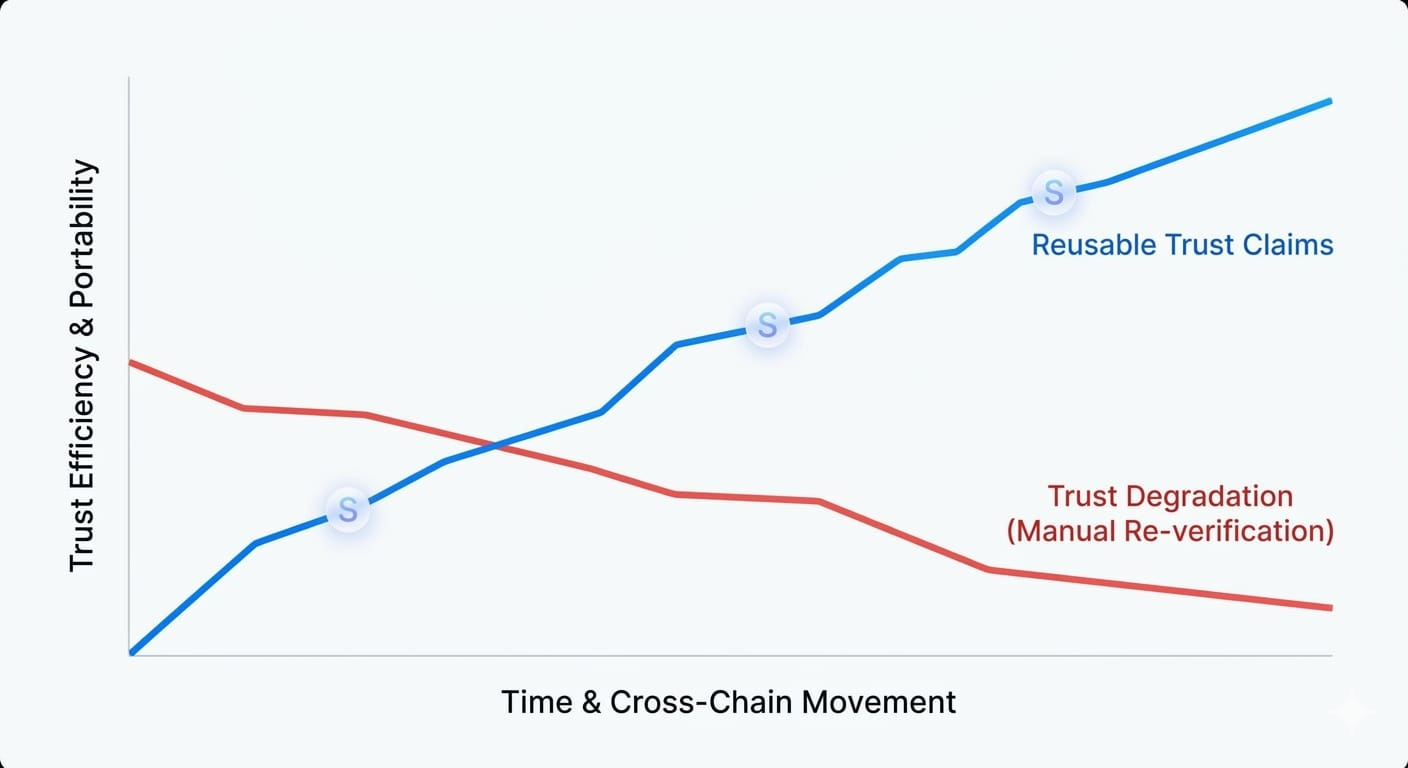
What Sign seems to understand is that the real problem is not only verification. It is continuity.
A fact should not lose its usefulness just because it moves to another chain, another application, or another workflow. If something has already been verified, tied to an issuer, structured properly, stored in a readable way, and made queryable later, then that evidence should be able to travel without forcing every new system to start trust from zero. That is why I think Sign matters more as infrastructure than as a product category.
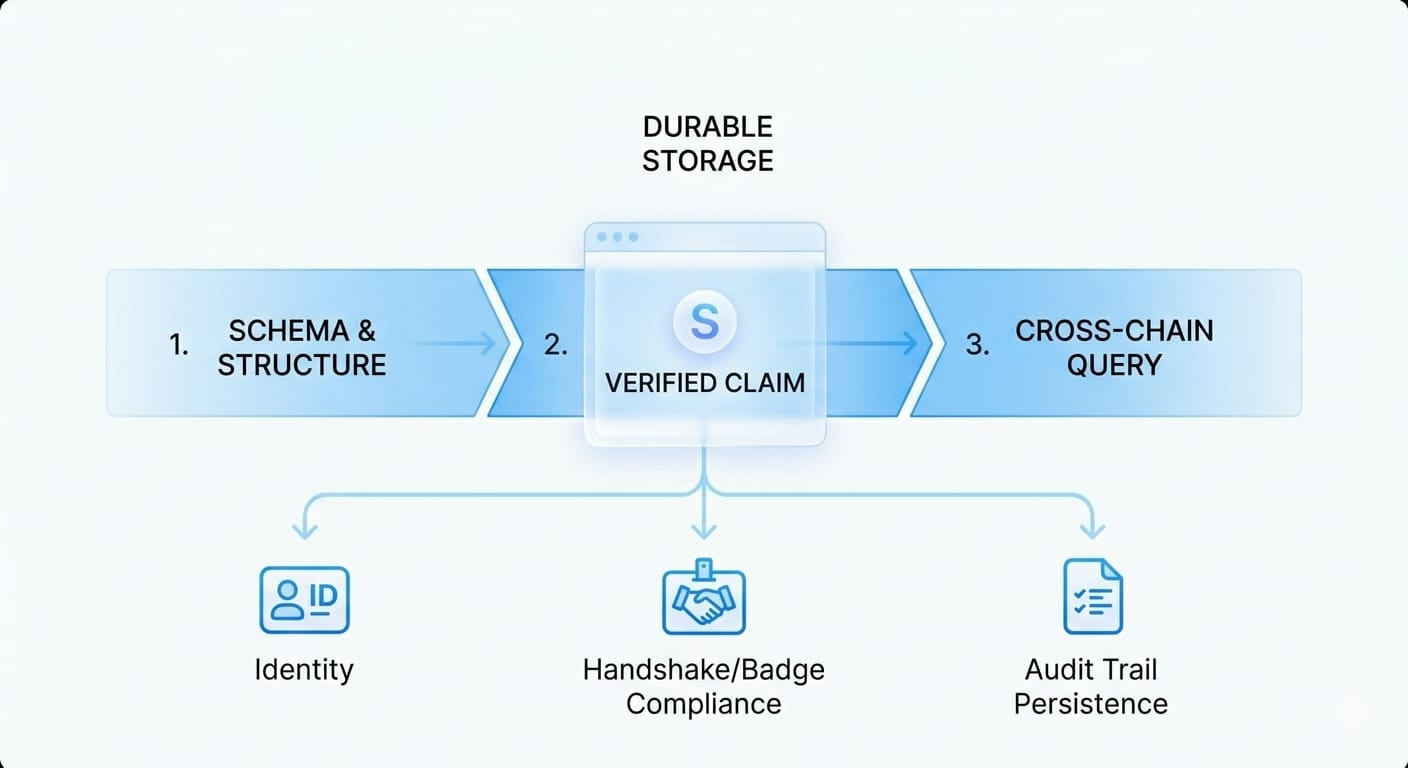
To me, the most important unit here is not the chain. It is the claim.
That changes how I read the whole design. Once the claim becomes the center, the bigger picture starts to make sense. Cross-chain verification is no longer just a technical feature. It becomes a way of preserving meaning across environments. Storage options are no longer a side detail. They become part of making evidence durable, accessible, and useful over time. Schemas stop looking like dry developer language and start looking like the shape that lets a fact survive movement without falling apart.
That is a much stronger idea than just saying Sign handles attestations.
And I think the “across time” part matters just as much as the “across chains” part. A lot of systems can verify something in the present moment. Far fewer can preserve the evidence trail in a way that still holds up later during audits, disputes, policy reviews, or institutional checks. That is where Sign starts to feel less like an app layer and more like a persistence layer for trust. Not just “is this true right now?” but “can this still be traced, understood, and relied on later?”
That opens a much bigger future.
Once verification becomes reusable, the same primitive can support identity, compliance, approvals, distribution, signatures, credentials, and capital movement without every sector rebuilding its own trust stack from scratch. That is when you stop seeing separate products and start seeing one deeper substrate underneath them. In that kind of world, Sign is not just helping systems verify users. It is helping systems share evidence without losing the original meaning of the proof.
Of course, I do not think portability automatically solves everything. A claim moving across systems does not guarantee it will be interpreted correctly. The receiving side still has to trust the issuer, understand the schema, handle privacy settings, and make sense of revocation rules. So no, this is not magical composability. But it is still a serious step forward, because it treats trust as something that should persist beyond the first use instead of expiring at the edge of one application.
That is why Sign keeps my attention.
Its strongest idea may not be that it can verify things. A lot of systems can do that. Its strongest idea may be that verification should stay useful after the first check. It should remain structured enough to move, clear enough to inspect, and durable enough to be reused.
That is not the loudest story in crypto. But I think it may end up being one of the most important.