Last week, when I was on a video call with Old Chen across the ocean, I was almost choked by the smell of cooking oil on his side. The broken range hood in the background roared like a tractor stuck in the mud, and Old Chen's face was glowing darkly under the West African sun, full of that kind of anxiety that comes from being beaten down by life after gaining citizenship.
He directly shoved that Redmi Note 7 (4GB+64GB version) with a screen shattered into a spider web, and even the middle frame was slightly cracked, right in front of the camera and yelled at me: "Little Lucky🌸, you quickly look! According to what you said, running that @SignOfficial 'mathematics witness', this broken phone is so hot it could make pancakes! The bank clerk stared at me as if I were a thief, saying what kind of evil thing I was doing. Your logic works in the lab, but in my kitchen, it’s about to burn my old buddy!"
I watched the 'electronic antique' still steaming in the video, and what I thought was: Old Chen, this anger is just right. This is the kind of commotion that digital sovereignty should have when it lands hard in the mud.
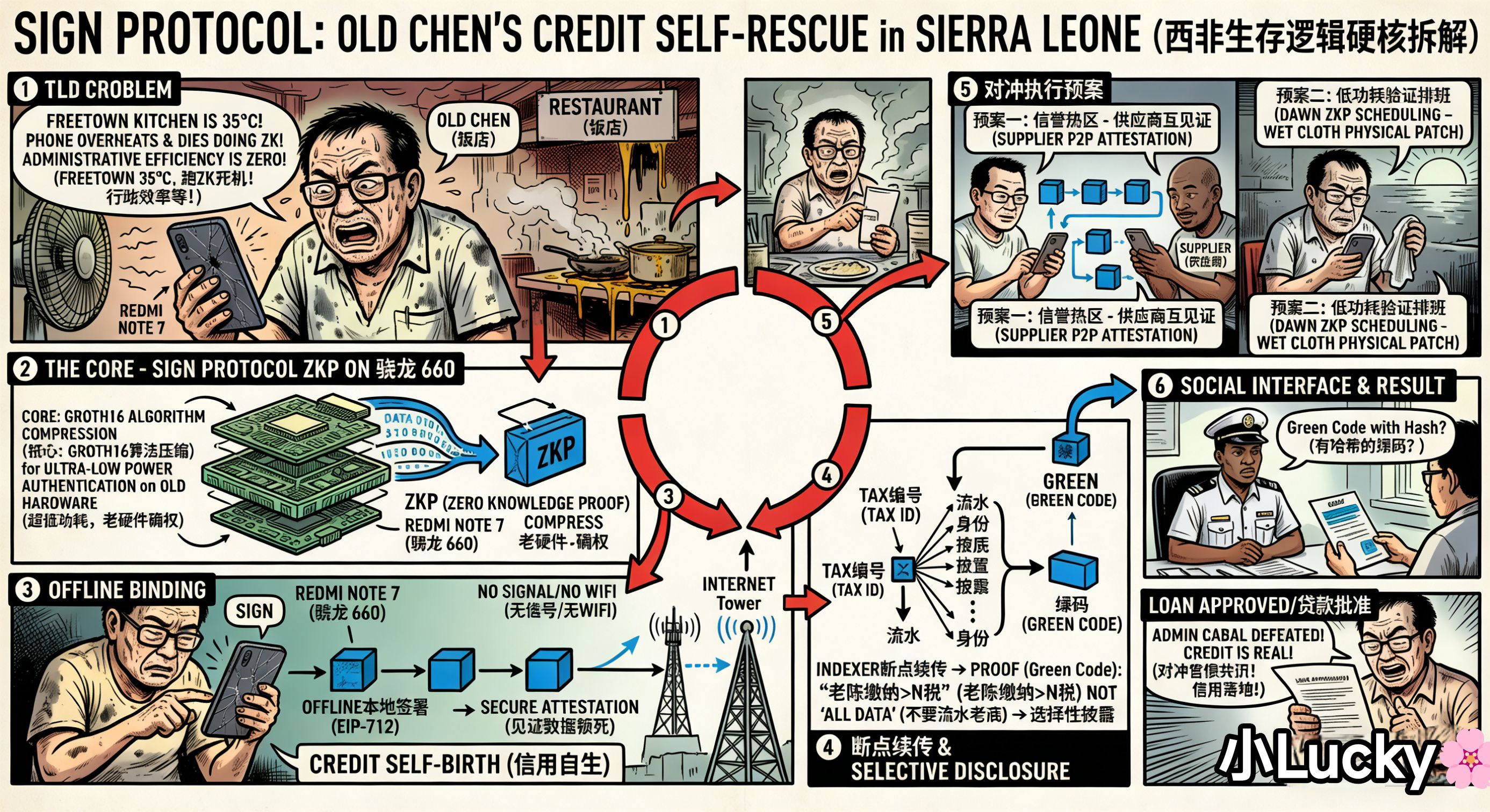
What Old Chen encountered is a typical 'sovereign witness (Attestation)' efficiency gap. In a place like Sierra Leone, the administrative system is worse than their roads. You have been naturalized, become a legal citizen; on paper, you are effective, but in the face of physical verification, you are a transparent person. You need that physical identity card printed with anti-counterfeiting watermarks and stamped with a big steel seal for the bank to recognize you as a person. But the problem is, when will that card be printed? 73% of the population has a tax identification number, but only 5% have the card in hand. The remaining 68%, like Old Chen, are stuck in the gap between the digital world and the physical world.
This is the core reason I must keep an eye on SIGN Protocol ($SIGN ) - it’s not about grand narratives that change the world in the white paper; it aims to forcibly uphold the credit dignity of ordinary people like Old Chen in this kind of mud.
The entire internet is making a fuss, saying how safe and private ZKP (Zero-Knowledge Proof) is, as if everyone is a Silicon Valley elite living in a temperature-controlled apartment.
But I stared at Old Chen's broken phone, and the depth I saw was just two words: power consumption.
You should know that Old Chen's Redmi uses the Snapdragon 660 processor released in 2017, and the 14nm process in West Africa in 2026 is practically 'electronic archaeology'. In the 35°C tropical heat, the kitchen doesn’t even have decent air conditioning, just a creaky fan. Running ZKP proof generation in this environment is not simple computation; it's a 'self-harm' of the chip’s main frequency under full load. Each hash operation overdrafts the last bit of lifespan of this old buddy.
But the brilliance of Master Bin lies in compressing the Groth16 algorithm to an astonishing degree. What I taught Old Chen is actually very 'primitive', even with a hint of hand-crafted steel-making: I had him forcefully kill all those messy short videos and shopping apps on his phone to free up that little bit of precious memory, then stick a wet towel on the back of the phone, and within the golden three minutes before the CPU gets throttled down from overheating, he squeezed out that timestamped Schema credential.
This kind of 'maxed-out expert returning to the novice village' technical ambush fundamentally competes with physical laws for time. It addresses the discontinuity of physical world data in extreme environments - no matter how poor your hardware is or how high the temperature is, credit cannot be interrupted.
At that time, I directly taught him how to execute 'digital self-rescue' step by step in the video; each action was to extract some credit from that pile of scrap metal:
Step one: offline blind signing and Schema anchoring. The base station signal in Sierra Leone is even less stable than the spatula in Old Chen's hand. I told Old Chen, regardless of whether there’s a signal, directly trigger EIP-712 signing locally. The moment Old Chen clicked on that Schema credential, even if the phone was in offline flight mode, this witness was mathematically locked. This is 'credit self-generation'. Once the network is connected, it can be instantly resumed through the Indexer. Old Chen doesn’t need to wait with bated breath for the government to open the door; at that moment, he himself is the certificate issuing center.
Step two: extreme squeezing of 4GB memory running ZK. This is the most solid detail of the game. Old Chen's Redmi only has 4GB of memory, and running a ZK verification almost fills up the swap partition. I told Old Chen to force a memory cleanup before verification, keeping only the core process of SIGN. When the verification progress bar turned to 80%, Old Chen's Xiaomi even flickered due to unstable current. This is the most solid truth in the review - although the Xinyan team simplified the algorithm, the physical limits of the old chip in executing high-intensity hash calculations are there.
Step three: selective disclosure in social games. The bank clerk insisted on checking his transaction records. Old Chen directly followed my instructions, checked the 'tax amount verification' option, and generated a green code with a hash anti-counterfeiting feature. The clerk was stunned on the spot; what he got was not Old Chen's business details, but an irrefutable mathematical conclusion. This kind of 'result delivery rather than data delivery' is the ultimate dignity of digital sovereignty. The ability to run privacy games on low-performance terminals is the strongest moat of this infrastructure.
Therefore, the 'credit hedging execution plan' I devised for Old Chen is a practical survival guide for West Africa:
Plan one: establish a 'decentralized reputation hot zone'. I taught Old Chen to unite surrounding spice suppliers also using SIGN to mutually provide 'business witness' through the Relayer mechanism. Old Chen settles accounts with the suppliers, and the suppliers in turn give Old Chen a 'reputation endorsement'. Even if the government’s physical cards take a year to issue, as long as Old Chen has this stack of 'digital credit assets' built from real transactions and tax amounts, he can directly bypass those inefficient local administrative counters and connect with those new cross-border financial services that recognize ZK logic.
Plan two: implement 'low-power verification scheduling'. To address Old Chen's phone overheating and crashing, I suggested he generate credentials concentratedly during the early morning when the base station load is lowest, or just after the phone is turned on when the CPU temperature hasn't risen yet. This 'computing power diversion plan' is to ensure that the success rate can remain above 95% in a hardware floor-level environment. Credit is not something you wait for; it’s calculated by Old Chen with a stopwatch, figuring out the thermal threshold of the Snapdragon 660.
Plan three: promote the social integration of 'UI simplifying complexity'. I had Old Chen take a screenshot of the generated Schema witness and save it as a simple QR code. This operation aims to lower the cognitive barriers of local bureaucrats - you don't need to understand what ZK is, nor do you need to understand blockchain; you just need to scan and see the green light, compare it with the tax hash in the system, and you can confirm that Old Chen is that legal, wealthy citizen. This logic of encapsulating the complex Attestation layer into an intuitive QR code is the only way for SIGN to penetrate a 'pre-modern society' like Sierra Leone.
In simple terms, Little Lucky’s straightforward approach is that this set of combinations is not meant to show off skills, but to ensure that ordinary people like Old Chen can truly grasp their digital credit with a broken phone.
And this is precisely the point where I am completely different from the vast majority of people in the market during my research project.
Many people only focus on the slight fluctuations of SIGN's K-line, studying the ups and downs on the screen every day, fantasizing about getting rich overnight; that’s speculation. My 'squatting point' review focuses on the real-time temperature of Old Chen’s phone and his straightened back in front of the bank clerk.
The greatness of technology does not lie in how high it flies or how fantastical the code is, but in whether it can catch ordinary people like Old Chen, who are about to be forgotten by the world in the corner. The value of technology should not be in the elite's PPTs, but in the shattered screens of ordinary folks.
Digitalization must be as practical as Old Chen's iron pot, able to withstand the grind. Next time in the video, let’s not talk about the abstract; let’s look at the results - see if your 'digital proof' made those eye-rolling clerks completely shut up! As long as it goes through, this matter is settled! I can say that I didn’t waste my time in your kitchen for half a year.