I was checking a recipient address on an attestation this morning.
Zero transactions.
Zero history.
The credential was valid.
The address had never done anything.
I pulled another one.
Different schema.
Different issuer.
Same result.
The `recipients` field was populated. ABI-encoded. Struct looked clean. The credential passed every check the system required.
But the recipient never showed up anywhere outside the attestation itself.
That’s where it started to feel off.
So I traced it back.
Where the recipient actually gets set.
The attester assigns it.
The schema accepts it.
The attestation is recorded.
After that, verification only checks whether the credential resolves against the schema.
Nothing in that path requires the recipient to ever appear.
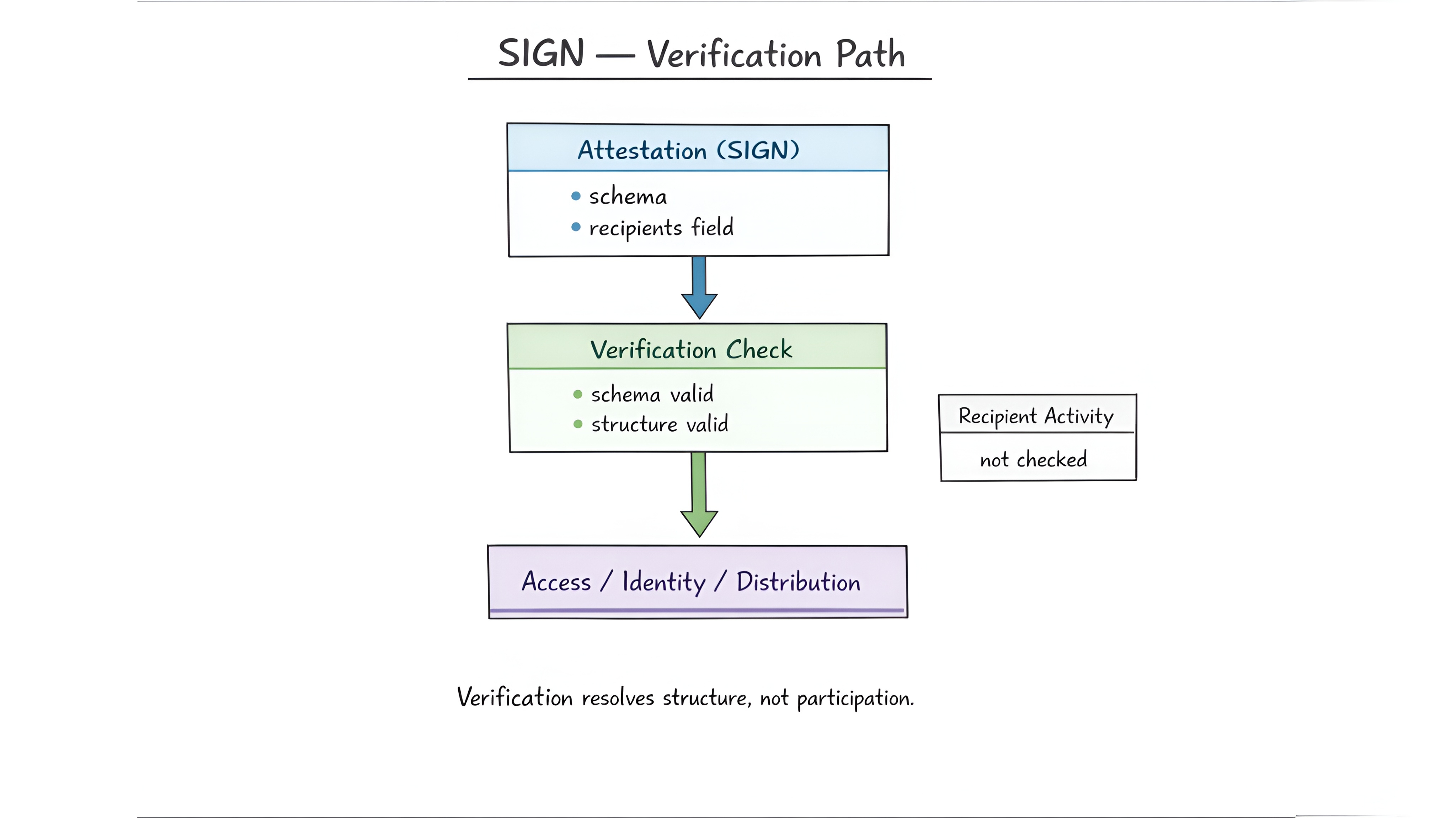
No signature.
No acknowledgment.
No interaction tying the address back to the credential.
The credential completes anyway.
I ran more.
Different attestations.
Different recipients.
Different contexts.
Same boundary.
The system never checked whether the recipient had done anything.
Only whether the field existed.
Phantom recipient.
After that I stopped looking at individual credentials.
And started looking at how systems use them.
An access layer reads `recipients` and grants entry because the credential verifies. There’s no signal anywhere showing whether the recipient ever interacted with it.
Identity linking behaves the same way. An address gets associated with a claim. The claim resolves cleanly, but nothing confirms the address ever accepted that relationship.
Distribution systems go further. Multiple credentials can point to the same address. All valid. All verifiable. None acknowledged. From the outside it looks like repeated participation. Underneath it’s just repeated assignment.
That’s where the behavior stabilizes.
The protocol preserves what was assigned.
It doesn’t track whether it was accepted.
Assignment resolves as acceptance.
Nothing in the attestation shows that distinction.
You only see the final state.
And that’s where it starts to break.
Access assumes presence.
Identity assumes confirmation.
Distribution assumes participation.
All reading the same field.
All depending on a signal the protocol never produces.
$SIGN only matters if a system where `recipients` defines identity without requiring acknowledgment can still distinguish between credentials that were assigned...
and those that were actually accepted.
Because once that boundary disappears...
there’s no way to separate them.
So the real question becomes this.
When a credential says it belongs to someone...
what proves they were ever part of it?
#SignDigitalSovereignInfra #Sign


