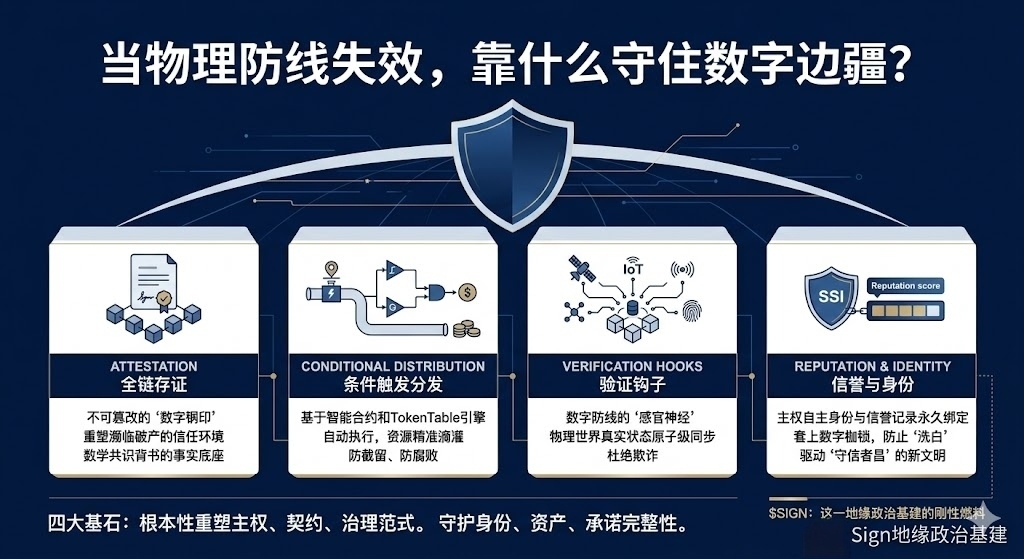
At three in the morning, I was once again awakened by notifications about the situation in the Middle East. What I was staring at on the screen wasn't the casualty numbers, but the code in my portfolio that was showing green against the trend: $SIGN . In this era where artillery can easily tear apart geographical boundaries, I, a long-time observer in the cryptocurrency space, clearly saw the outline of another defense line for the first time. It is not constructed from concrete and barbed wire, but built from the four cornerstones of Attestation, Conditional Distribution, Verification Hooks, and Reputation & Identity, forming a digital Great Wall.
At the geopolitical game table, the most vulnerable asset is commitment. A piece of paper may become worthless due to regime change, and the terms of international aid may become distorted in layers of execution. The core of the SIGN protocol is to use blockchain technology to forge the intangible 'verbal commitment' into an unalterable 'digital seal.' Through full-chain attestation, any important declaration, inter-state treaties, citizens' identities, and asset ownership can be transformed into verifiable credentials with cryptographic signatures, permanently anchored on the chain. This is equivalent to rebuilding a factual foundation backed by mathematical consensus in an international environment on the brink of trust bankruptcy. When the notarization system of the physical world collapses due to conflict, this globally visible and unerasable on-chain signature becomes the last refuge of trust.
With credible commitments, how to execute? Traditional financial and aid systems are inefficient and easily intercepted or corrupted in conflict areas. The TokenTable engine in the SIGN stack, at its core, is based on Conditional Distribution. Governments or international organizations can preset rules: this aid can only be given to specific refugees verified through zero-knowledge proofs; funds can only be used to exchange for food and medicine and cannot be withdrawn; reconstruction funds will be automatically released according to project milestones. All of this is executed automatically by smart contracts, with no one able to intervene. This is not just a technical optimization but a governance revolution, encoding policy intentions into code, allowing goodwill and resources to be delivered as precisely as a scalpel, ignoring the chaos and obstacles of the physical world, directly drip-feeding to those in need.
However, how does on-chain code know what happens in the offline world? How is the status of aid reaching refugee camps automatically confirmed? This relies on 'Verification Hooks.' They act as sensory nerves for the digital defense line, transmitting real-world state changes to the blockchain through IoT devices, satellite data, or multi-party signed evidence. When sensors confirm that supplies have arrived, or authorized agencies validate an event, the hooks automatically trigger the execution of subsequent steps in the on-chain contract. This mechanism ensures atomic-level synchronization between digital rules and offline facts, eliminating fraud that exploits information asymmetry, providing a uniquely reliable factual baseline in complex information warfare.
The ultimate goal of the defense line is to regulate behavior and establish order. Based on the Self-Sovereign Identity (SSI) framework, SIGN establishes an unforgeable digital identity for each entity. More importantly, all on-chain behaviors, whether contractual obligations are fulfilled or whether there is integrity, will become indelible reputation records permanently bound to the identity. A vendor with multiple defaults will have their tainted record accessible throughout the network, unable to wash it away by changing identities. This effectively places digital shackles on potential deceivers and fraudsters, raising the cost of wrongdoing to an unbearable level. In national cooperation, good on-chain reputation becomes a core asset for obtaining collaboration, credit, and markets, driving the formation of a new digital civilization where 'trustworthy individuals thrive.'
Looking at these four cornerstones, what they collectively build is not a simple pile of technology, but a fundamental reshaping of national sovereignty, the spirit of contract, and governance paradigms in the digital dimension. When physical borders become fragile, this defense line based on cryptography and global consensus protects the integrity of digital identity, assets, and commitments.@SignOfficial What is done #Sign地缘政治基建 is precisely to provide the scarcest certainty for this uncertain era.$SIGN As the rigid fuel driving all of this, its value will be anchored in the real and expanding demand for sovereign digital activities. Holding it, in my view, is not speculation, but a clear stance, standing with a more resilient order protected by code.