I was tracing one simple claim through Sign the other day and it genuinely messed with my head.
Everyone keeps calling it a “trust layer.” Attestations, schemas, reusable proofs. It all sounds clean and elegant when you read the docs. But the moment you actually follow a real-world decision from its messy beginning all the way through to TokenTable or SignScan, something shifts. It stops feeling like verification and starts feeling like compression. Mechanical, deliberate compression.
The claim never starts inside Sign. It begins somewhere ugly and human, stacks of documents, internal judgment calls, exceptions, approvals that don’t fit neatly into any form. That full, chaotic reality is what we usually mean by “trust.” Sign doesn’t take the whole thing. It takes what can survive the first filter.
That filter is the Schema.
It doesn’t ask “Is this true?” It asks something much quieter: “Can this even be expressed here?” Fields, types, constraints, versioning anything that doesn’t fit simply disappears from the protocol’s point of view. Not rejected. Not marked false. Just never becomes legible. I felt that cut the first time I saw it happen in a test flow. Something real existed… and then it didn’t exist for the system anymore.
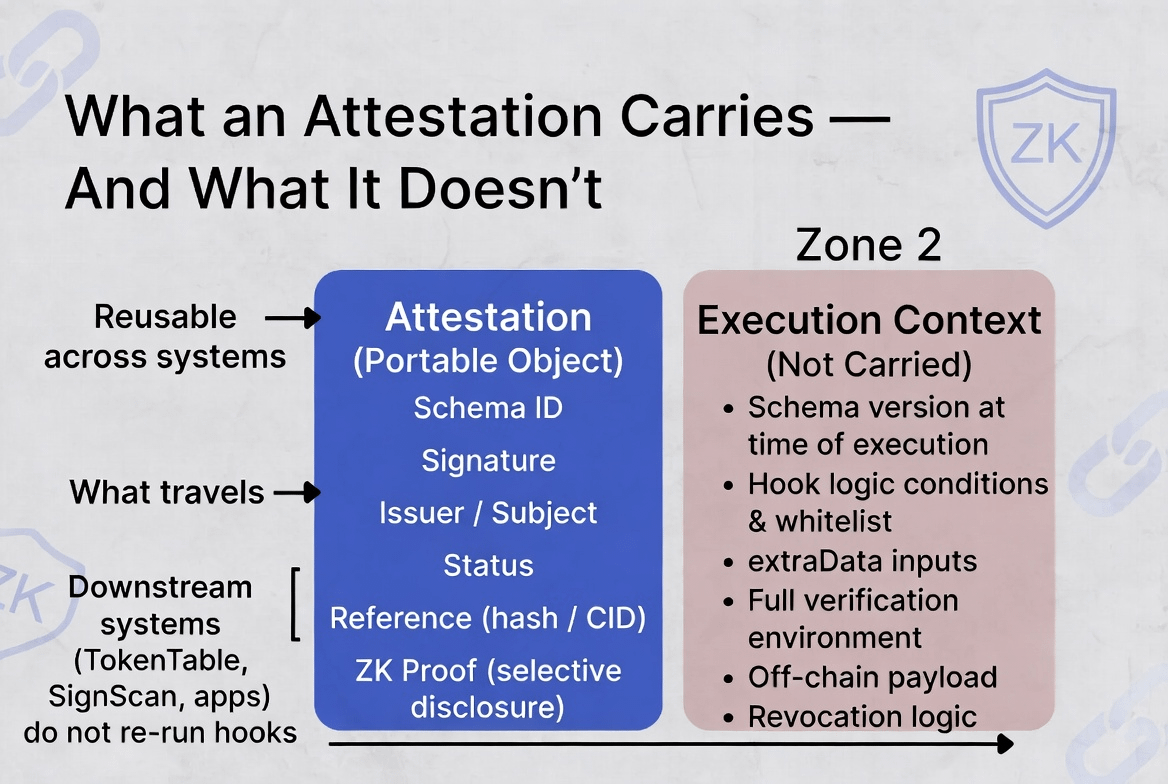
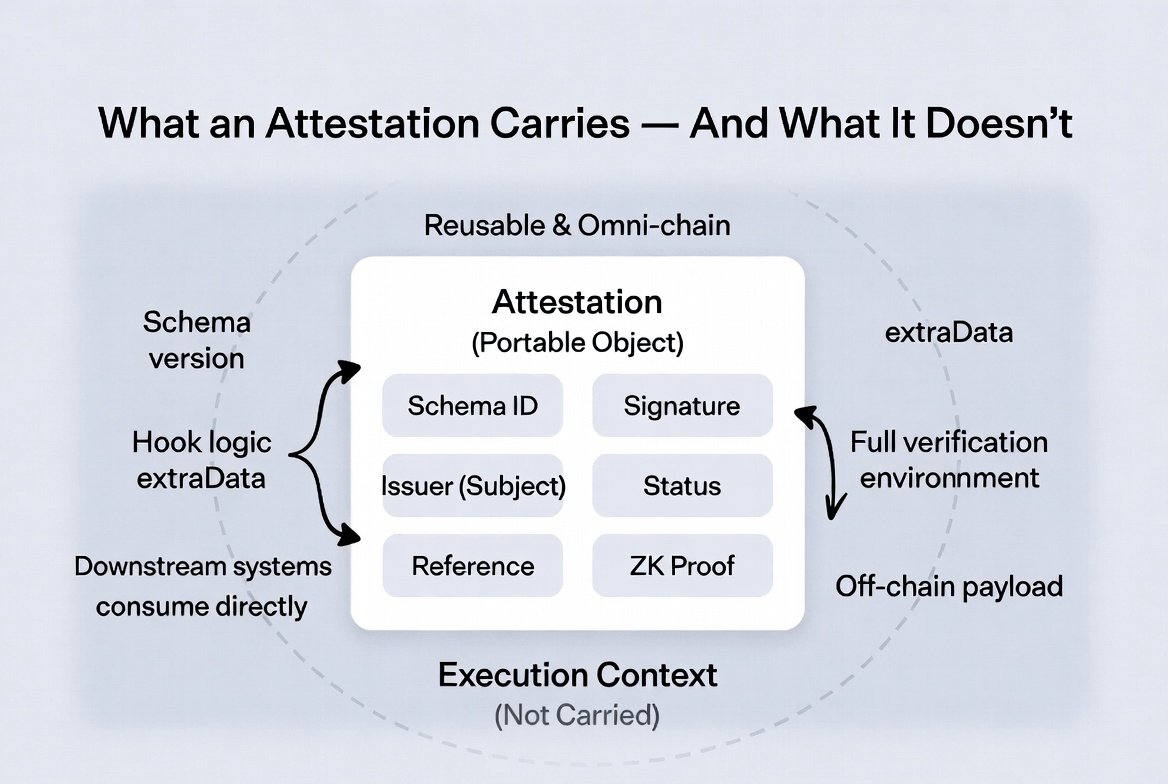
Whatever survives gets pulled into attestation creation. And this is where the layers start tightening, one by one. Schema check. Issuer binding. Authority validation. Hook logic. ZK selective disclosure. Storage decisions. Each step strips away a little more context. By the time you get a signed, portable attestation, it’s no longer the original situation. It’s the compressed residue that made it through every single filter.
And here’s the part that still sits with me: if something fails any of those steps, the system doesn’t give you a rejection notice. It gives you silence. No record. No failure trace. No error object. Just… absence.
No attestation means no evidence.
No evidence means no eligibility in TokenTable.
No eligibility means no distribution, no payment proof, no audit trail, no nothing.
The downstream apps don’t argue with it. They just move on like it never existed.
Technically, I have to admit it’s brilliant. The ZK selective disclosure lets you prove something without dumping raw personal data on-chain. The omni-chain design means the same attestation works across Ethereum, Solana, TON without rebuilding trust every time. Storage separates the payload from the anchor so things stay lightweight. Indexing makes it searchable and reusable instantly. That’s the real impact trust finally becomes small enough and fast enough to actually move at crypto speed instead of getting rebuilt from scratch in every app.
But the tradeoff is brutal once you see it clearly.
What you gain in portability and reusability, you lose in context and transparency. The system isn’t proving truth every single time. It’s proving “this is what survived our compression.” The attestation you see on SignScan isn’t the full story. It’s the surface layer of something that already got filtered, reduced, and reshaped long before it reached you.
I left that session respecting the engineering more than ever, but I also can’t unsee the asymmetry. Sign isn’t just creating evidence. It’s deciding, at every layer, which parts of reality are allowed to exist inside the evidence layer and quietly erasing everything else.
That’s heavier than most people realize when they talk about “portable trust.”
It works. It scales. It makes real distribution and compliance actually possible. But it also forces us to accept that by the time something becomes verifiable, the harder part of the original judgment has already been compressed out.
And what we’re left with is not the whole truth just the part the protocol decided was worth keeping.
Still turning that one over in my head.
$SIGN #SignDigitalSovereignInfra @SignOfficial
