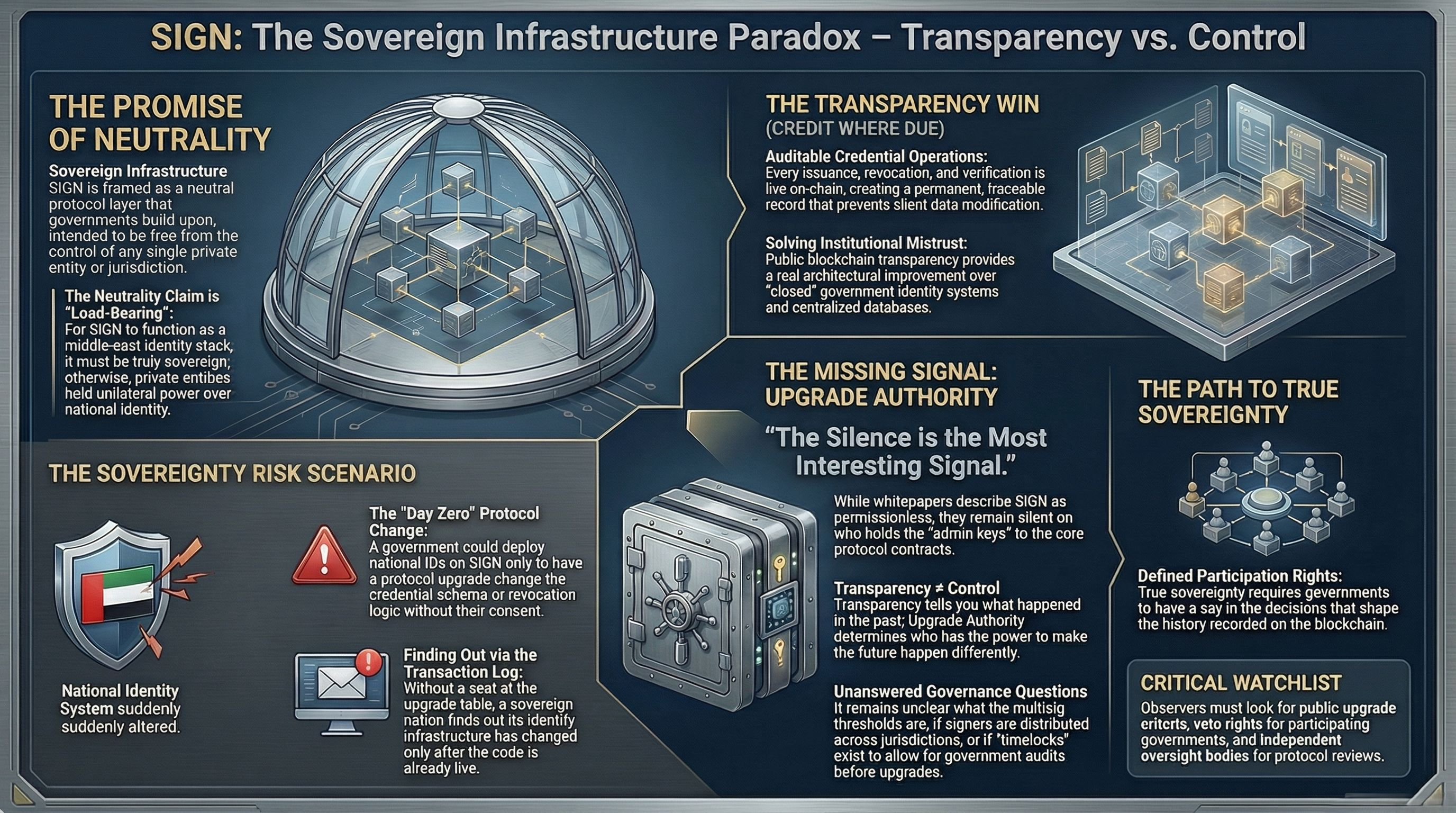
nobody in the $SIGN conversation is talking about upgrade authority and honestly? that silence is the most interesting signal in the entire architecture
the claim worth examining
the whitepaper positions SIGN as sovereign infrastructure, a neutral protocol layer that governments and institutions build on top of, not controlled by any single entity, not subject to any single jurisdiction. the framing is deliberate. sovereign infrastructure cannot be sovereign if a private entity holds unilateral upgrade authority over the base layer. the neutrality claim is load-bearing for everything SIGN is trying to do in the Middle East identity stack.
the context matters here because deployment is targeting national digital identity infrastructure where the smart contracts governing credential issuance, revocation, and verification are live on-chain and processing real citizen data across real government services.
credit where it's due
the decision to build on a public blockchain with transparent contract logic is genuinely meaningful. every credential operation is auditable. every state change is recorded. no single government can silently modify the registry without leaving an on-chain trace. for a region where institutional trust in centralized databases is complicated, on-chain transparency is a real architectural improvement over closed government identity systems.
the upgrade question
transparent contracts and immutable history do not answer who controls the next version. smart contract systems have admin keys, proxy patterns, multisig controllers, or governance modules that allow the logic to be changed after deployment. the transparency tells you what happened. it does not tell you who had the power to make it happen differently.
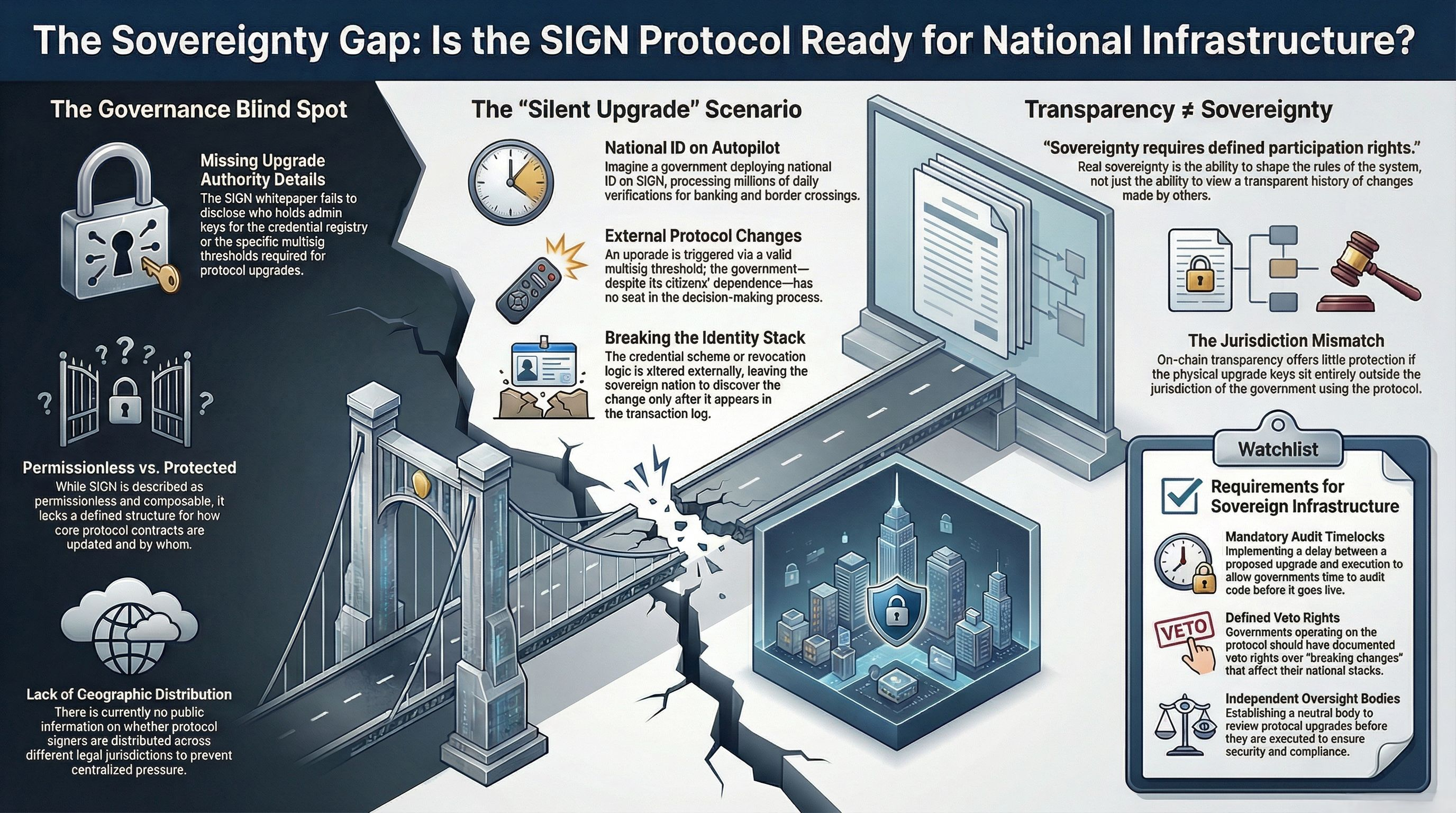
the whitepaper describes SIGN as permissionless and composable. it does not describe the upgrade authority structure of the core protocol contracts. who holds the admin keys on the credential registry? what threshold of signers is required to push a protocol upgrade? are those signers distributed across jurisdictions? is there a timelock between a proposed upgrade and its execution that gives governments time to audit before it goes live?
the scenario nobody's modeled
a government deploys national digital ID on SIGN. citizens receive credentials. millions of verifications happen daily across banking, border crossing, and government services. then the core protocol receives an upgrade. the upgrade is technically valid, the multisig threshold was met, the on-chain process was followed. but the government whose citizens depend on this infrastructure had no seat in the upgrade decision. the credential schema changes. the revocation logic changes. and the sovereign nation running its identity stack on SIGN finds out the same way everyone else does, by reading the transaction log.
sovereignty requires more than transparent history. it requires defined participation rights in the decisions that shape what that history contains.
watching: whether any SIGN deployment documents public upgrade governance criteria, whether governments operating on the protocol have defined veto rights over breaking changes, and whether any independent oversight body reviews protocol upgrades before execution.
what is your take, does on-chain transparency actually protect a government's sovereignty if the upgrade keys sit outside their jurisdiction??