I thought the weird part would be money moving between rails.
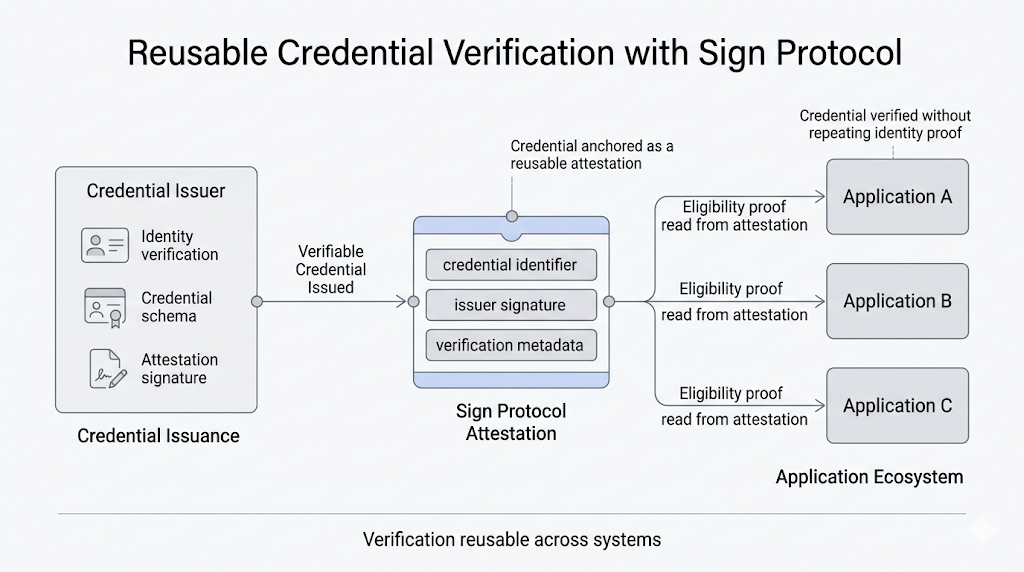
Public side here. Private side there. Fine. Annoying, maybe, but legible. Sign’s architecture is built to support that split anyway: one sovereign stack, different money modes, different privacy settings, same evidence layer underneath. From a systems view, that sounds healthy. Controlled even. Public where interoperability matters. Private where confidentiality is the whole point.
That is not where it got strange.
The strange part was watching the same person turn into two different operational beings depending on which rail their case touched.
A routine program at first. Nothing dramatic. A citizen qualifies through Sign-backed identity and eligibility checks. The first payment goes through the private rail because it is a retail-facing benefit and nobody wants that history hanging open for the whole world to inspect. Later, part of the same broader case touches a more public lane, maybe reporting, maybe interoperability, maybe a market-facing leg that has to settle in a mode built for wider visibility. Still the same program family. Still the same human. Still the same sovereign system. TokenTable can execute across those environments, and Sign Protocol keeps the evidence and policy references linked tightly enough that the stack remains coherent on paper.
On paper. That phrase kept bothering me.
Because the paper version is exactly where Sign looks strongest. Policy says this flow uses a private mode. Another flow uses a public or semi-public mode. Governance decides privacy level per program. Identity stays anchored. Evidence stays verifiable. Settlement references remain tied back to the same ruleset and authority trail. Clean architecture. Sensible separation.
Then support gets the call.
Not a cryptography call. Not some “prove the attestation” call. A human call. Why does my first payment look invisible here, but my second one looks attributable there. Why did one side of the system treat me like a protected case and the other side treat me like an address, a reference, a visible participant in a broader network. Why am I apparently the same beneficiary in policy language, but not in how the system lets me be seen.
That’s the cut.
Sign can keep the architecture unified without keeping the experience unified. The stack remains internally consistent because it was designed that way: private rail for confidentiality-sensitive operations, public rail for transparency or interoperability, shared evidence underneath, auditable links across systems.
But the citizen does not meet “the stack.” The citizen meets consequences.
On one rail, they exist as a protected subject whose case visibility is tightly controlled. On the other, they exist as something closer to a publicly legible participant because that rail is solving a different institutional problem. Same underlying eligibility. Same sovereign program family. Different exposure. Different interpretive weight. Different feeling in the body when you open the app and realize one side of your own case behaves like sealed paperwork and the other behaves like market infrastructure.
I kept wanting to call that inconsistency. Not the right word. Design split, maybe. No. Worse than that. A coherent fragmentation.
Because nobody inside Sign necessarily did anything wrong. The rails are doing their jobs. The policy logic may be perfectly sound. The evidence may line up exactly as intended.
And still the person at the edge walks away with a harder question than the architecture diagram ever has to answer:
if one sovereign system lets the same beneficiary exist privately in one money flow and visibly in another, who is responsible for making that feel like one citizenship experience instead of two incompatible versions of the same life?