i've been thinking about a problem that most web3 identity projects quietly ignore: almost all the data that actually matters about a person lives on web2 servers that blockchain systems can't read.
your bank balance, your salary history, your credit score, your medical records, your employment status — none of it is on-chain. and for the most part, none of it can be brought on-chain without either trusting a centralized intermediary to relay it honestly, or forcing the web2 service to build a custom integration that most of them will never build. this is the fundamental bottleneck in decentralized identity that doesn't get discussed enough.
SIGN's MPC-TLS case study addresses this directly, and the technical approach is genuinely interesting once you understand what it's actually doing.
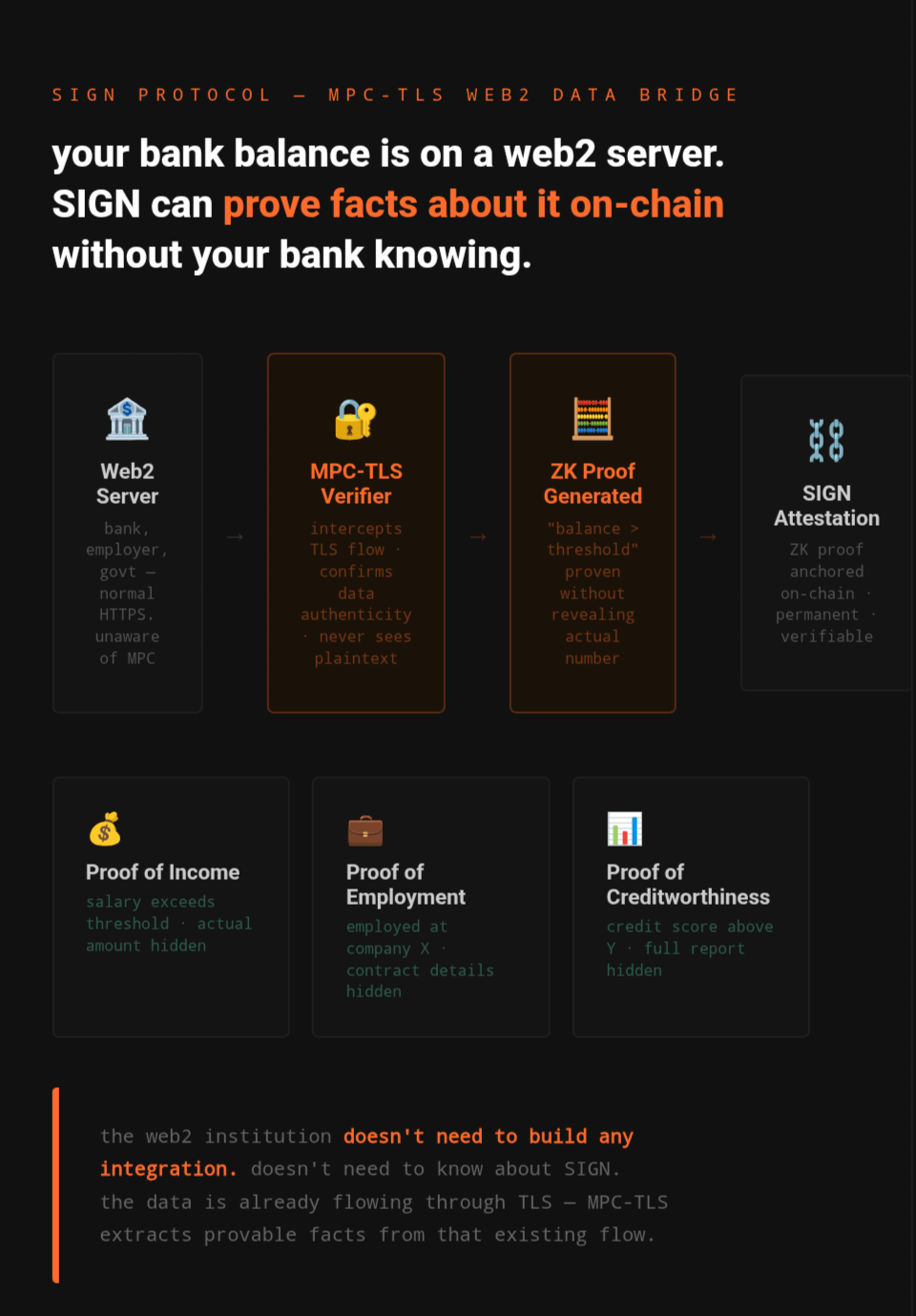
the foundation is TLS, which is the encryption layer behind every HTTPS website. when you visit your bank's website, TLS ensures the traffic between you and the server is encrypted and that nobody in the middle can read it. MPC-TLS takes that standard setup and adds a third-party verifier into the TLS handshake in a very specific way: the verifier can confirm the authenticity of data being transmitted without actually being able to see the data in plaintext. the web2 server doesn't know the MPC mechanism is there at all and doesn't need to cooperate with it.
after the data retrieval completes, the user and the verifier jointly produce a zero-knowledge proof. this ZK proof can convince a downstream system that a certain fact about the encrypted data is true, without revealing the underlying data itself. so if you want to prove your bank account balance exceeds a certain threshold, the ZK proof says 'yes this condition is true' and the SIGN attestation records that proof on-chain. your actual balance number never appears anywhere.
what makes this significant is that it eliminates the need for the web2 institution to participate at all. your bank doesn't need to know about SIGN. your employer doesn't need to build an API. the data is already flowing through TLS connections and MPC-TLS intercepts that flow at the verification layer to extract provable facts from it.
from a practical standpoint this opens up credential types that were previously impossible in decentralized systems. proof of income without revealing your salary. proof of employment at a specific company without exposing your contract. proof that your credit history meets a lending threshold without giving a lender access to your full report. these are credentials that actually matter for real financial and social participation, not just crypto-native use cases.
the tradeoff worth thinking about is the role of the MPC verifier itself. while the verifier can't see your data, you're still relying on that verifier to participate honestly in the protocol. if the verifier is compromised or colluding, the integrity of the proof degrades. this is a different trust model than purely on-chain operations, and it's worth understanding before assuming MPC-TLS attestations carry the same guarantees as a credential issued directly by a known institution.
that said, for bridging the gap between the web2 world where most people's real credentials live and the on-chain world where decentralized applications need to read them, this approach is one of the more technically honest solutions i've seen. it doesn't pretend the web2 data doesn't exist, and it doesn't require the entire financial system to rebuild itself around blockchain-compatible APIs.
i'm curious whether anyone has actually used MPC-TLS to generate a SIGN attestation from a real web2 source, and what the user experience looks like in practice. the technical design is elegant but whether that translates into something normal people can actually run through is a different question entirely.
#SignDigitalSovereignInfra $SIGN @SignOfficial
