Honestly? I’ve been sitting with $SIGN Protocol’s design, and the more I dig into it, the less it feels like a typical crypto project and more like a backend system you’re not supposed to notice 😂. Most people look at things like airdrops or identity as isolated features, but Sign is clearly trying to unify them under one verification layer.
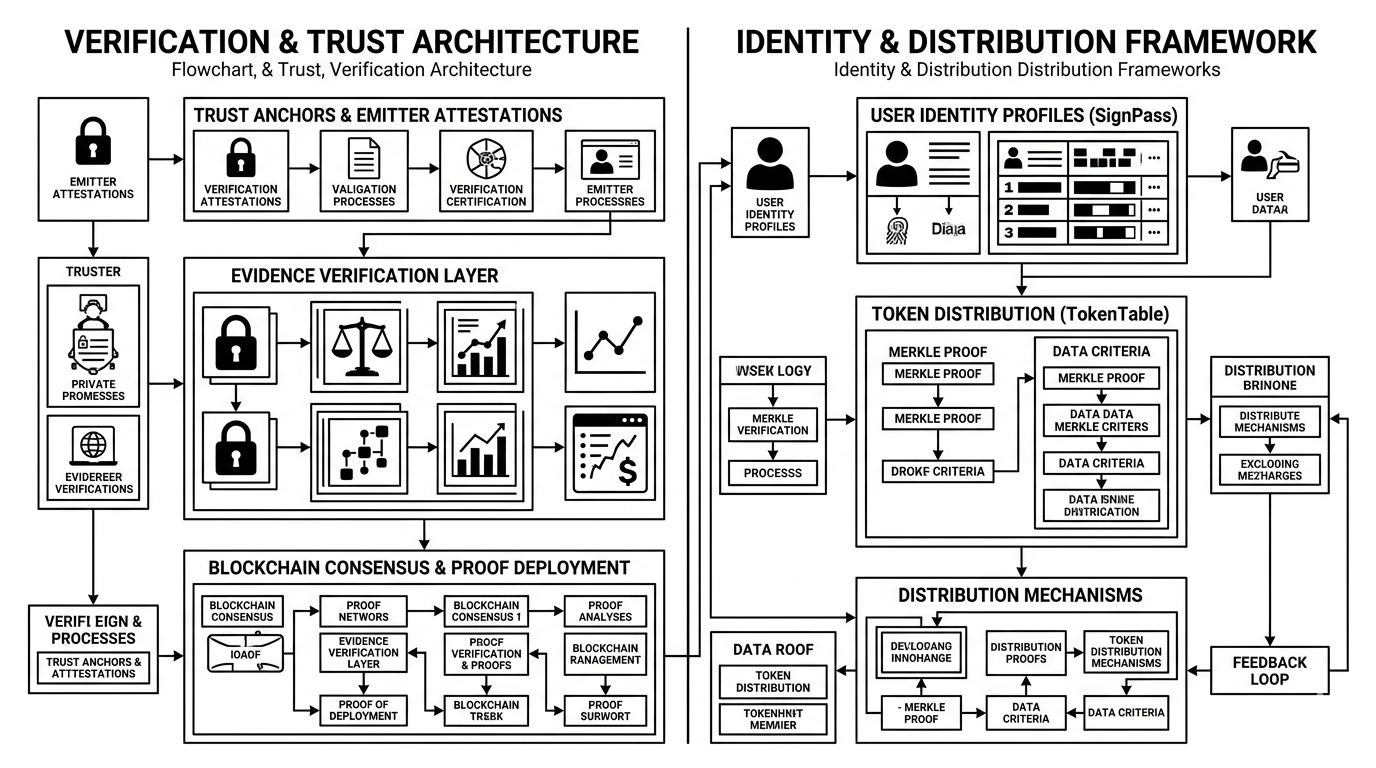
I Take airdrops, for example. On the surface, people think it’s just token distribution. But what Sign actually does is tie distribution to verifiable identity and on chain attestations. That means eligibility isn’t just a wallet address. it’s a condition backed by data, proofs, and rules. TokenTable leverages this by combining Merkle proofs, signatures, and identity-linked criteria, making distributions both scalable and resistant to manipulation. What stands out here is that fairness becomes programmable, not assumed.
I there’s transparency in government systems. Sign flips the model from “trust the institution” to “verify the action.” Every approval, update, or distribution can generate an attestation, creating a record that exists independently of internal databases. That’s powerful because it reduces reliance on centralized narratives. But the tension here is obvious transparency depends not just on data being recorded, but on who controls access to that data layer.
I use Identity management is where Sign feels the most necessary. Fragmentation across platforms, repeated KYC, and lack of portability are real problems. SignPass attempts to solve this by turning identity into reusable, verifiable credentials. Instead of re verifying everything, users carry attestations that can be selectively disclosed. It’s efficient, but what I kept coming back to is issuer trust. If the source of identity is flawed, the entire chain inherits that weakness.
I see Data availability is another subtle but critical piece. Sign doesn’t rely on a single chain or storage layer. It uses a mix of on chain deployments, off chain storage like Arweave, and indexing through SignScan. This layered approach ensures records are accessible even if one component fails. But it also introduces dependencies availability becomes a function of multiple systems staying aligned.
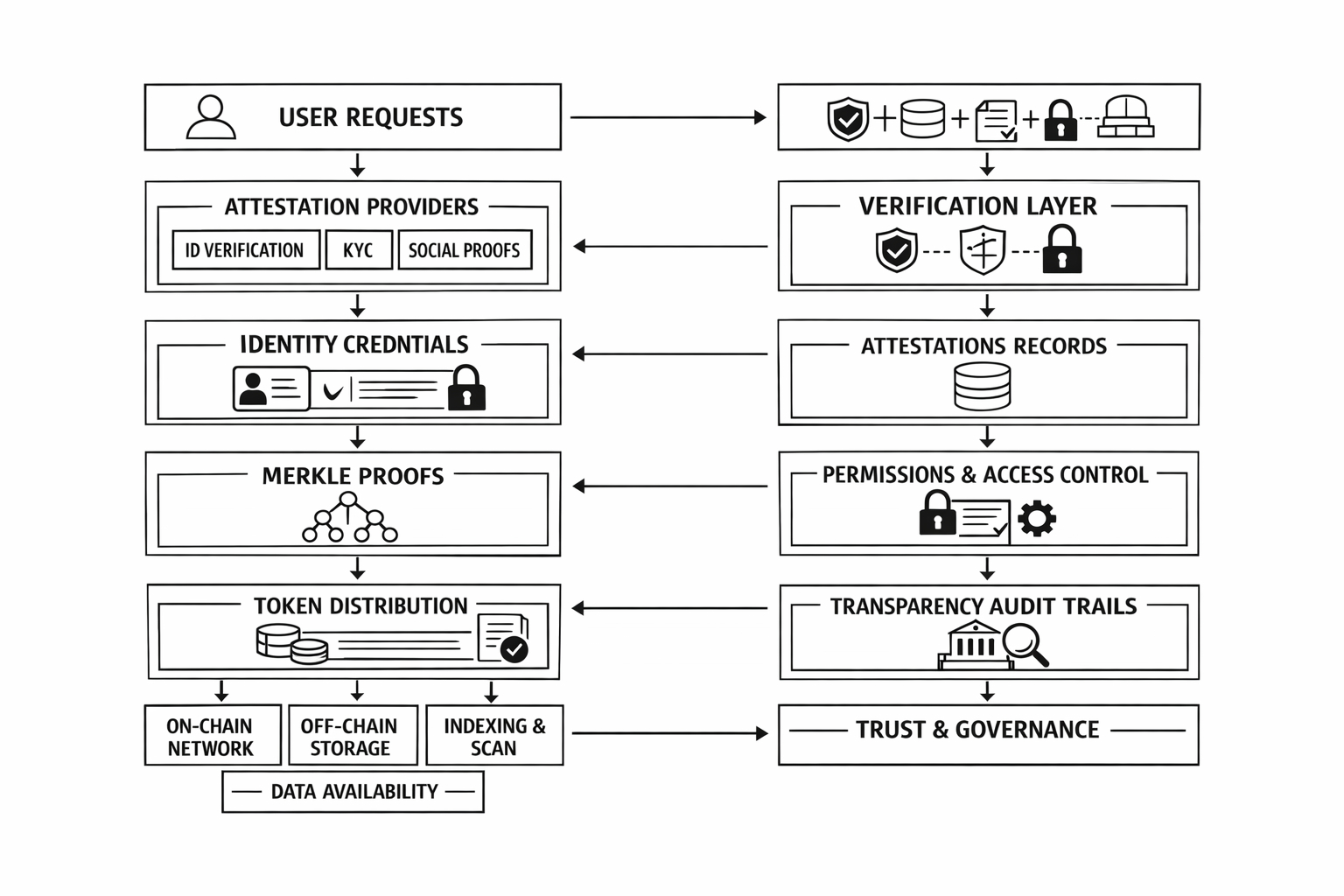
So when you zoom out, Sign isn’t just solving isolated problems it’s trying to standardize how systems prove things. And that’s ambitious. But it raises a deeper question: if verification becomes infrastructure, who ultimately controls the truth that infrastructure enforces?
@SignOfficial $SIGN #SignDigitalSovereignInfra

