I remember the first time I tried to follow a proof across chains and realized I was doing trader math on top of trust assumptions I had not actually checked. The claim looked clean. There was a signed record, a schema, a reference, and a nice story around portability. But once I started asking the annoying questions that matter when real money is involved, things got messier fast. Which chain anchored the attestation? Was the signer still authorized? Had anything been revoked? Was I looking at the source record or just an indexed view of it? That was the moment Sign stopped looking like a tidy infrastructure narrative to me and started looking like a harder, more interesting trade.
That is still how I see it on March 26, 2026. Sign Protocol matters because it is not trying to be another base chain. The docs are pretty clear that it is an evidence and attestation layer, not the ledger itself. Its job is to standardize how claims are structured, signed, stored, queried, and referenced, while using underlying chains and storage systems for anchoring and tamper evidence. Sign also says SignScan unifies querying across supported chains, and the builder docs describe direct reads from contracts and Arweave alongside that indexed view. In plain English, the pitch is simple. Put the proof in a format other apps can read, move the verification logic closer to something reusable, and stop forcing every app to rebuild trust from scratch.
Now here’s the thing. Multi chain proof verification sounds cleaner than it is. A proof is not just a blob you carry from one chain to another like a screenshot. You still have to verify the signer, the schema, the storage reference, the revocation status, and the context in which the claim was made. Sign’s own materials lean into that. The docs frame attestations as signed records that conform to schemas, and the whitepaper talks about verification pathways, revocation infrastructure, expiration management, and selective disclosure. That is exactly why I take it seriously. The protocol understands that a proof is only useful if somebody else can inspect it later and reach the same conclusion. But it is also why I stay cautious. Every extra chain, storage layer, and privacy mode adds one more place where developers can get sloppy or where users assume “verified” means more than it really does.
That is the challenge in one sentence. Sign can standardize the container for trust, but it cannot magically standardize the judgment of every app that reads it.
I think that matters for traders more than the usual product talking points. When a project says it supports fully on chain attestations, off chain payloads with verifiable anchors, hybrid models, and privacy enhanced or ZK modes, I do not hear convenience first. I hear implementation risk first. Hybrid storage is useful because large or sensitive payloads do not belong everywhere. The docs explicitly note on chain references with Arweave or IPFS style payload storage, and they also show cases where zero knowledge validation results can be attested once and then bridged to other chains after the initial attestation. Good. That is practical. But practical systems break in practical ways. Data availability, inconsistent indexing, stale revocation checks, bad schema design, weak permissions. This is not the sexy part of the trade, but it is the real part.
The market is not giving Sign a premium valuation right now. CoinGecko shows SIGN at about $0.03221 today, down 24.2 percent in 24 hours and down 26.8 percent over seven days, with roughly $114.2 million in 24 hour volume, about $52.8 million in market cap, and about $322.1 million in fully diluted valuation. The same page shows 1.6 billion tokens circulating against a 10 billion max supply, with 1.93 billion unlocked and 8.07 billion still locked. That means the FDV is about 6.1 times the current market cap, and roughly 80.7 percent of max supply is still locked. For me, that is the entire setup. The bull case is not hard to see. If Sign becomes one of the default trust rails for cross chain attestations, identity linked proofs, and rules based verification, then a roughly $52.8 million market cap can look light. Especially when the token is already trading more than 2.1 times its market cap in daily volume. That tells you the market is paying attention, even if it is paying attention nervously.
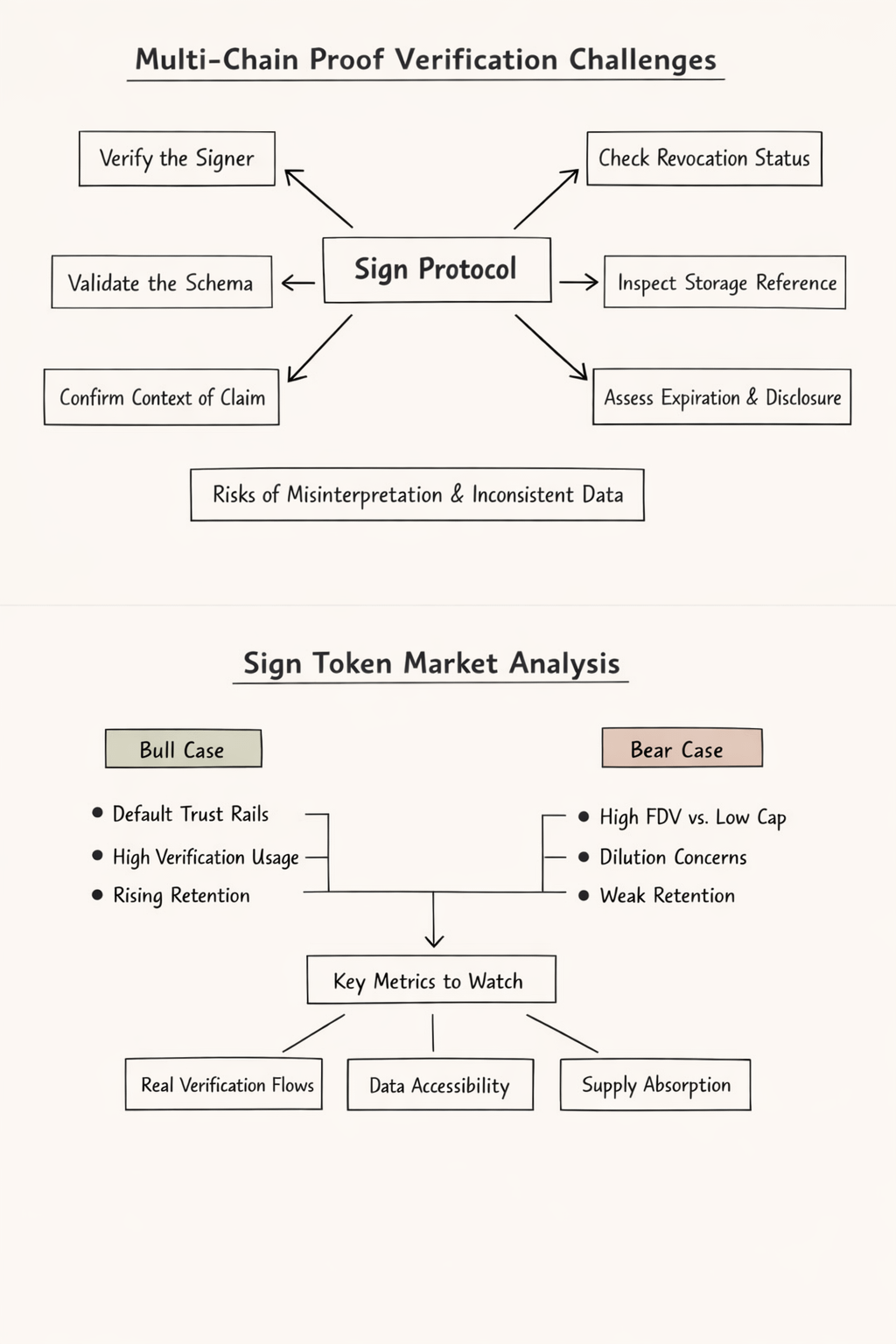
But the bear case is not subtle either. A low market cap with a much larger FDV is only attractive if usage compounds faster than dilution anxiety. Otherwise it is just cheap for a reason. And this is where the Retention Problem hits Sign directly. Anybody can get a burst of attention from airdrops, campaigns, governance experiments, or identity narratives. I do not care. What I care about is whether applications keep coming back to verify claims through the same rails after the first wave of curiosity fades. Do developers keep building around the schema model? Do institutions or operators rely on the same evidence layer for recurring workflows? Do users generate proofs because they need to, not because they were nudged once?
That is my honest frustration with this kind of trade. The product can make perfect sense before the token does. You can believe the architecture is directionally right and still hate the supply profile. You can like the evidence layer and still doubt whether the token captures enough of that value in a durable way. I sit in that tension with Sign. I think the protocol’s multi chain verification model is more serious than most people realize. I also think that “serious” does not automatically convert into sticky token demand.
So here is what I would watch instead of getting lost in slogans. I would watch whether real verification flows keep showing up across different chains and use cases, whether SignScan and direct reads keep the data legible enough for outside developers to trust the stack, and whether the market starts treating unlocked supply as absorbable rather than threatening. If those things improve together, the bull case gets a lot stronger. If they do not, then the project risks becoming one more example of useful infrastructure with a token that traders only visit for brief windows.
If you are looking at SIGN here, do not ask whether multi chain proofs sound important. Ask whether Sign is becoming the place people return to when proof actually needs to survive contact with another chain, another app, and another month of scrutiny. That is the only version of trust that tends to pay.
