Identity doesn’t move. It gets re-proven, every time.
I ran into this inside Sign Protocol while trying to reuse a credential across two chains. Same wallet. Same schema. Same user context. Still had to re-attest, or at least it felt that way.
At first I assumed it was a sync issue. Maybe indexing lag. Maybe I pushed too quickly. But after a few iterations, it became clear the system wasn’t failing. It was being strict. The attestation existed, but on the second chain it wasn’t treated as the same object. It was treated as a claim that needed to be re-validated in that environment.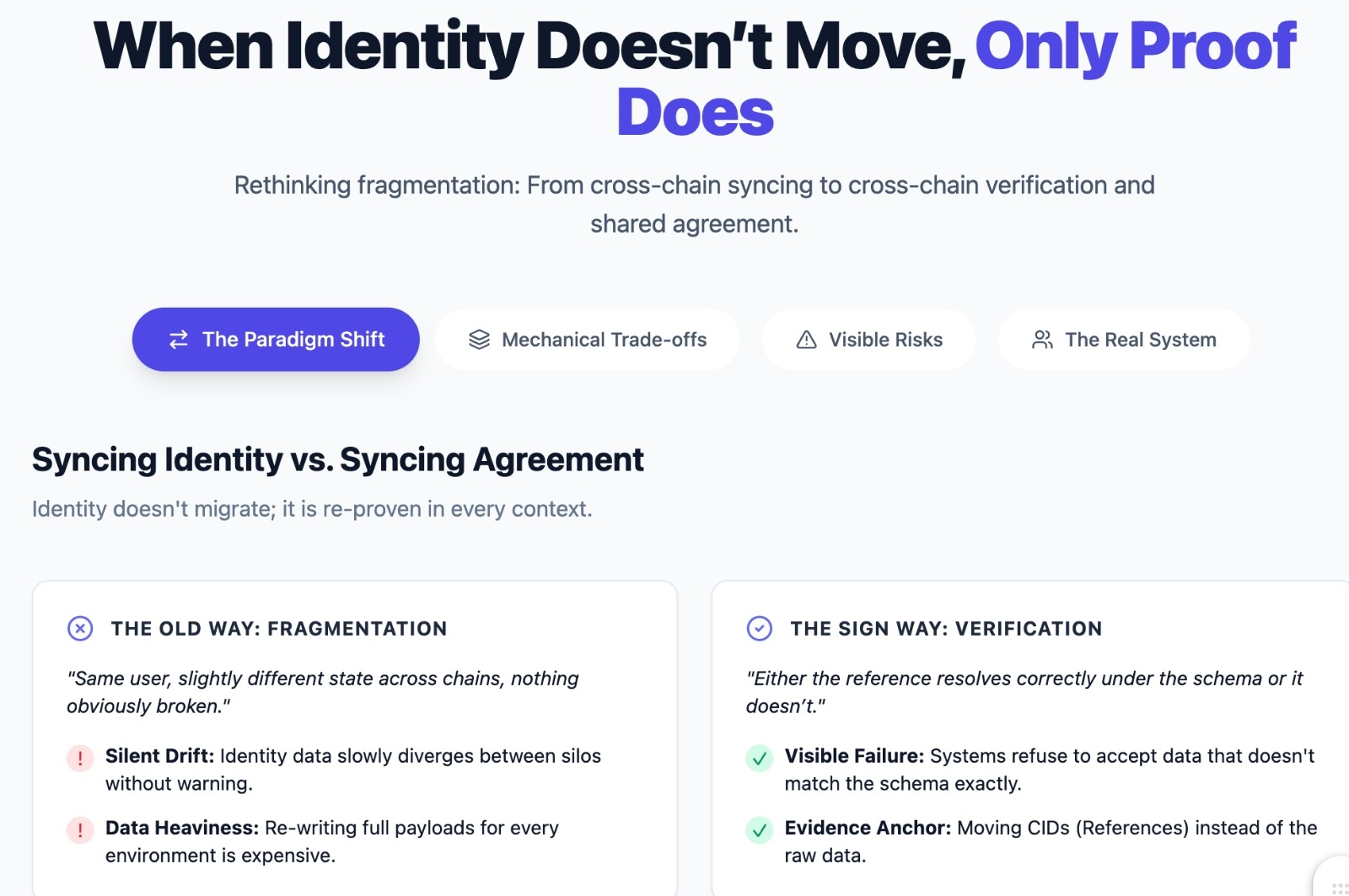
That’s where Sign’s model starts to feel different. It doesn’t try to unify identity across chains. It standardizes how claims about identity are structured and verified. You’re not moving identity. You’re moving evidence.
I tested this using a simple credential stored off-chain on IPFS, referenced on Ethereum through a schema. When I reused it on another chain, I didn’t rewrite the data. Just referenced the same CID. The gas cost dropped significantly. In one case, writing a full on-chain payload would have cost 5 to 10 times more than just anchoring a reference. But the bigger shift wasn’t cost. It was behavior.
Before, identity fragmentation showed up quietly. Same user, slightly different state across chains, nothing obviously broken. After using Sign, the failure becomes visible. Either the reference resolves correctly under the schema or it doesn’t. No silent drift. That removes one class of risk. But it introduces another.
Second test. I pushed around 60 attestations across two chains, all tied to the same schema and off-chain data. About 20 of them didn’t resolve cleanly on the receiving side the first time. Not because the data was wrong, but because the schema interpretation differed slightly between environments. The system didn’t corrupt. It just refused to accept.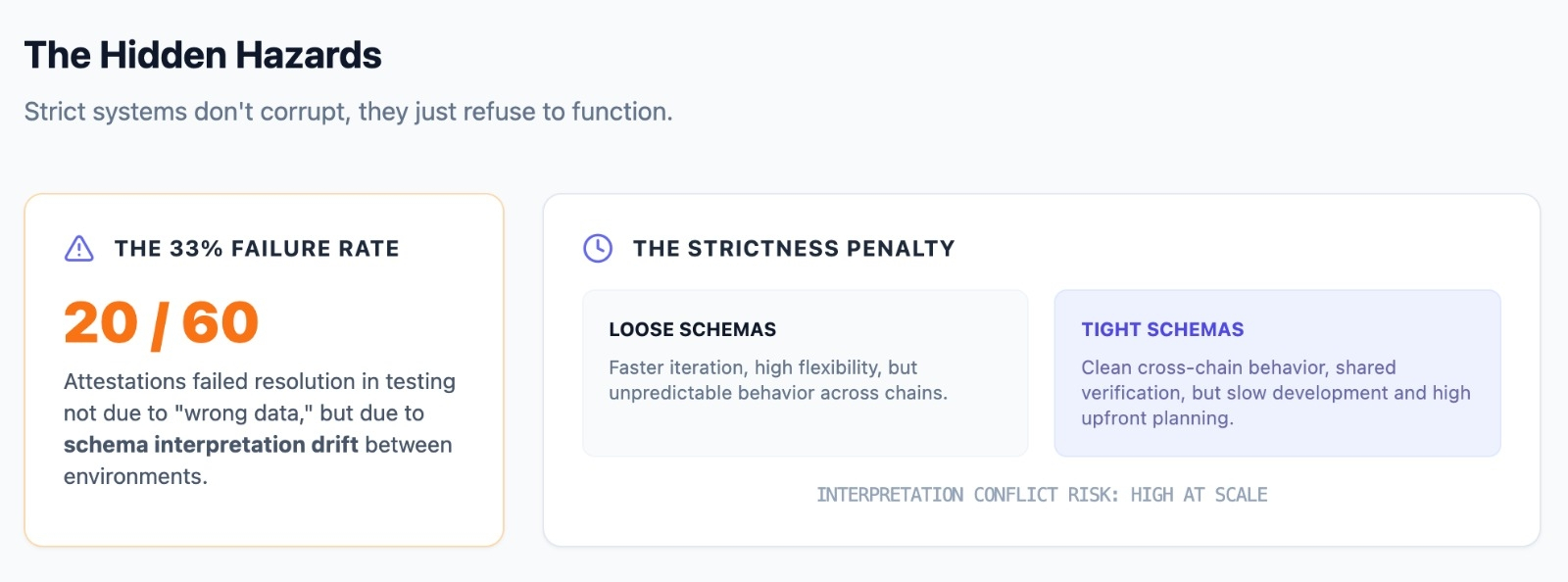
Designing schemas that survive across chains is not forgiving. You need to anticipate how different systems will read the same fields before anything goes live. That slows iteration. It adds friction early. Feels unnecessary until you try scaling identity across three or four environments and realize the alternative is constant duplication. I’m not fully convinced most teams will get this right early on.
There’s also a deeper shift in where the cost sits. Off-chain storage reduces gas usage, especially when you’re dealing with larger payloads. But now coordination becomes the expensive part. Every system consuming that attestation needs to agree on how to interpret it. And that agreement is not enforced by the chain.
It’s enforced socially. Through shared schemas. Through conventions. Through teams deciding, often implicitly, what a field actually means.
Try this. Take one attestation and reuse it across two chains, but change how one field is interpreted on the receiving side. Not the structure, just the meaning. Watch what happens a few steps later when something depends on it. The break won’t be immediate. It’ll show up downstream, where identity is assumed to be consistent.
Or go the other way. Lock the schema tightly. Enforce strict validation everywhere. You’ll get cleaner cross-chain behavior, but you’ll also feel the slowdown in development. More planning. More coordination. Less flexibility.
Somewhere in the middle of this, I stopped thinking about attestations as identity and started seeing them as checkpoints. Not who someone is, but what has been accepted about them at a specific moment, under a specific schema.
That framing made things easier to reason about. You’re not syncing identity across chains. You’re syncing agreement.
Which is why the token starts to make sense later, even if you ignore it at first. You need some way to coordinate participants around shared schemas, resolve disputes in interpretation, and maintain consistency over time. Without that, the system drifts back toward fragmentation, just at a higher layer. Still, I have doubts.
If two applications use the same schema but assign slightly different meaning to one field, is the identity actually shared? Or have we just moved fragmentation from infrastructure into interpretation?
And what happens when scale increases. Not hundreds, but thousands of attestations moving across chains daily. Does schema discipline hold, or does it loosen under pressure?
Try pushing 50 to 100 attestations across multiple chains and watch where alignment starts slipping. It doesn’t break immediately. It degrades slowly. That’s the part I’m still watching.
Sign doesn’t eliminate fragmentation. It makes it visible, structured, and harder to ignore. It replaces silent divergence with explicit verification. But it also introduces a new dependency on coordination that doesn’t live on-chain. And that coordination might end up being the real system.
@SignOfficial #SignDigitalSovereignInfra $SIGN
