The trouble on Sign wasn’t that anyone saw different evidence.
It was worse than that. Everybody saw the same evidence.
Same attestation. Same schema. Same issuer trail. Same quiet, machine-legible proof that a person had qualified, or completed something, or held whatever status the program cared about. Sign is very good at creating that feeling. One evidence layer. One reusable record. One place in the stack where the qualification exists in a form other systems can pull from without rebuilding the fact every time.
That sounds clean until a real team starts touching it.
Product pulls the record because they want to know whether the user should move forward in the flow. Not philosophically. Right now. Button on screen, next step unlocked, eligibility resolved. Support opens the exact same record because the user is already annoyed and wants an answer that sounds final. Compliance looks at it because now the question is not whether the user qualifies but whether the evidence is the kind that can survive review later. Ops comes in from the side, not caring about the narrative at all, just whether the verification state is solid enough for the system to act on.
Nobody is asking Sign for the same thing anymore.
That is where the shared evidence layer starts feeling less like clarity and more like compression. Too many institutional jobs folded into one record because the record is portable enough to travel.
And portability on Sign is exactly what makes this pressure real.
A schema gets defined. An issuer attests. The credential sits there clean enough to be reused across applications, campaigns, distributions, access controls, audits, reviews. That reusability is the whole point. Sign makes evidence durable across contexts. The attestation does not have to become a new object every time a new department wants to ask something of it.
But the meaning attached to the evidence starts drifting the second those departments stop sharing the same operational goal.
Product reads the record as a decision input.
Support reads it as a resolution tool.
Compliance reads it as future-facing documentation.
Ops reads it as a readiness signal.
Same credential. Same proof path. Same underlying Sign infrastructure.
Different jobs pressing on it hard enough that the record starts carrying more than it was ever supposed to carry by itself.
That is the part I keep getting stuck on. People talk about unified evidence like it naturally creates alignment. On Sign, what it often creates first is evidence reuse without purpose alignment. The attestation is shared. The institutional reason for touching it is not. So the record stays stable while the demand around it becomes contradictory.
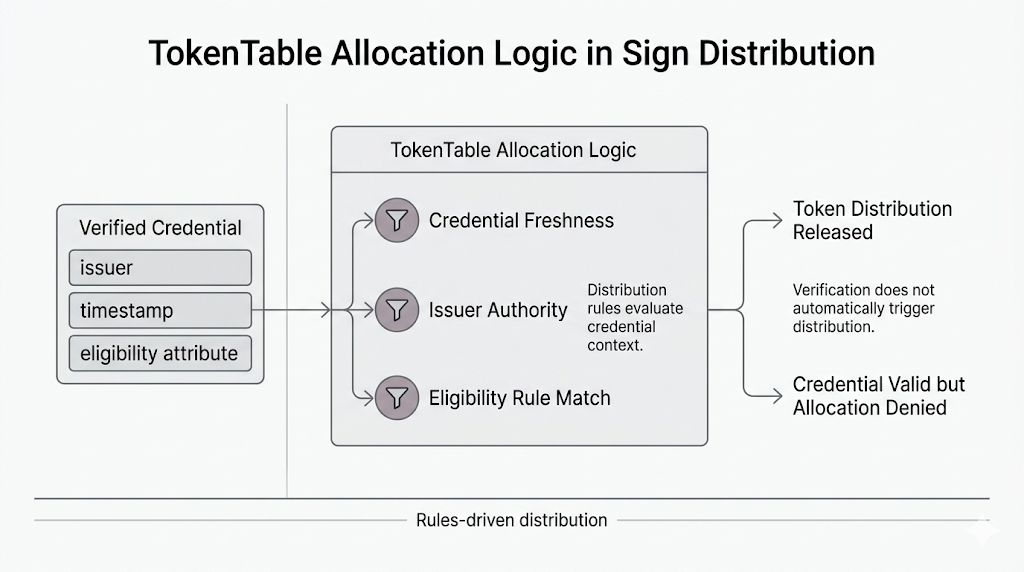
Support wants to say the matter is closed because the credential verifies. Product wants to advance the flow because the eligibility logic is satisfied. On Sign, Compliance wants to slow everything down because a valid record is not automatically an adequate review artifact. Ops does not care that the record exists if acting on it opens a downstream mess nobody wants to own.
And nobody is really wrong.
That’s what makes it difficult.
Sign does the hard infrastructure work of keeping the evidence reusable across contexts. The problem is that once the same record starts serving product, support, compliance, and operational execution at once, the argument is no longer about whether the evidence is real.
It’s about which institutional job gets to define what that evidence is enough for.