The night before last, I was dragged by a friend from the community to rush for a new Web3 project airdrop. As an old player who has been deeply involved in the track for many years, the process of cross-chain transfer, contract authorization, and form submission has long been ingrained in my DNA. But halfway through the operation, when the system popped up the requirement to 're-upload on-chain behavior proof + past contribution records', I was directly stunned in place—on-chain data is obviously publicly available, why does every project seem to have 'trust amnesia' and insists on making users repeatedly prove themselves?
This scene hits the most concealed yet deadly pain point of Web3: there is still no interoperable trust transmission mechanism between different chains and ecosystems, just like there is no universal passport in reality, and every country requires you to reprove 'you are you'. With this question in mind, I dissected the Sign Protocol (SIGN) and the booming sovereign chain logic, and this article will present 3 core conclusions + a selection framework to help you see the true landscape of Web3 trust track.@SignOfficial

Sovereign chains: Project teams' 'exclusive fortresses,' users' 'trust cages'
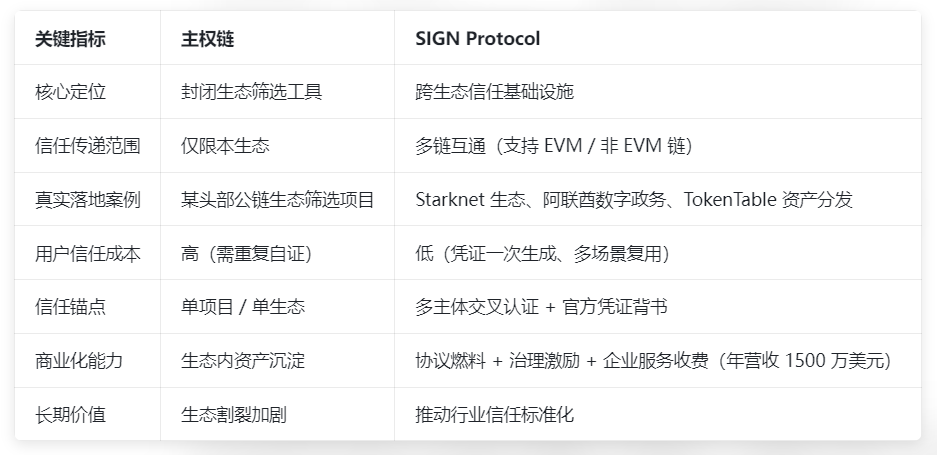
The reason sovereign chains can become the new favorite in the industry is that they accurately grasp the core demands of project teams: autonomously formulating ecosystem rules, controlling validation logic, customizing user access thresholds — wanting to prevent witch attacks means raising interaction thresholds, and wanting precise airdrops means breaking down on-chain behavioral data. This model of 'I control my domain' is a perfect solution for project teams pursuing autonomy and control.
Its advantages are straightforward and hardcore: the flexibility of rules is maximized, allowing rapid iteration of filtering mechanisms based on ecosystem needs; performance can be adjusted as needed, unaffected by congestion or resource limitations in public chains; personalized filtering is precise, capable of accurately identifying target users and avoiding airdrops being snatched by opportunists. However, the extreme autonomy behind it cannot avoid industry fragmentation, as each sovereign chain is building independent user systems, behavioral standards, and credibility models, essentially repeating the construction of 'closed trust loops'.
The most intuitive example is a sovereign chain project in a leading public chain ecosystem, where users completed six months of node staking and community governance within its ecosystem and obtained 'core contributor' certification. However, when switching to another sovereign chain project within the same public chain, they were deemed 'a new address with zero interaction' and needed to complete 30 days of interaction tasks to qualify for airdrops. In simple terms, sovereign chains only solved 'how to filter the users they want' but did not address the core problem of 'how verified users can circulate across ecosystems' — this is not a deliberate hassle from the project team, but rather that they lack trustworthy channels to recognize user data from other ecosystems.
SIGN Protocol: The 'trust router' that breaks down walls, reconstructing cross-chain trust with standards
Unlike the 'building walls logic' of sovereign chains, SIGN's approach can be described as 'anti-involution': it does not build chains or ecosystems but focuses on building 'cross-ecosystem trust infrastructure' — clearly defining 'what constitutes effective contributions' through schema data templates, using Attestation signature verification technology to record 'which entities recognized these contributions', transforming user behaviors scattered across chains into 'on-chain trust certificates' that can circulate across scenarios.
In simple terms, it means: your interactions, contributions, and credibility in any project will be packaged by SIGN into an immutable 'digital passport'. When participating in new projects in the future, there is no need to submit proof again; project teams can directly read this certificate to complete verification, just like presenting a passport at customs instead of having to retake a visa each time you enter a new country.
Real-world scenarios + simulation cases: Efficiency showdown between two models
Real case 1: After multiple projects in the Starknet ecosystem integrated SIGN, users' transaction records on a certain DEX and collection records in the NFT market could directly serve as the basis for airdrop filtering for other projects, without the need to re-upload certificates, resulting in a 70% increase in airdrop participation efficiency;
Real case 2: A certain government department in the UAE, through the SIGN Stack architecture, put citizens' passports and degree certificates on-chain to generate trust certificates, achieving rapid identity verification in cross-border business cooperation, shortening administrative processes by over 50%;
Real case 3: TokenTable, as the asset distribution engine of the SIGN ecosystem, has served over 200 projects, with a total distribution amount exceeding 4 billion USD, covering 40 million on-chain wallet addresses. Its core is the precise distribution based on SIGN's trust certificates.
Simulation case: The little capybara's airdrop adventure
The little capybara is a veteran retail investor deeply engaged in the Layer2 track, holding a 'senior holder' certification for a zkSync ecosystem NFT project and a 'high-quality lending user' label from a certain lending protocol on Arbitrum.
Under the sovereign chain model: When he participated in a new DeFi project airdrop in the Optimism ecosystem, the project team required submission of 'on-chain interaction certificates from the last 3 months'. The little capybara had to export transaction records from zkSync and Arbitrum browsers separately, manually organize them into a spreadsheet for upload, and then wait for 72 hours for manual review by the project team; after finally passing the review, when participating in an NFT project in the Polygon ecosystem, he had to repeat the process of 'export - organize - upload - review' again. The certificate organization alone took 5 hours, and he was rejected twice due to formatting issues.
Under the SIGN model: The little capybara generated a unified trust certificate for his on-chain behaviors in zkSync and Arbitrum through SIGN in advance. The certificate clearly indicated core information such as 'NFT holding duration of 6 months' and 'lending fulfillment rate of 100%'. When participating in the new project in Optimism, he directly authorized the project team to read the SIGN certificate, and the system completed verification in 3 seconds; when participating in the new project in Polygon, the same one-click authorization took place with zero manual operations, and the total time spent on both airdrops was less than 10 minutes.
Returning to the airdrop scenario from the night before, the process reconstructed with SIGN is extremely simple: complete interaction tasks in Project A to obtain a SIGN-certified contribution certificate; Project B verifies the validity of this certificate through SIGN; quickly determine whether you are a real and valid user, directly skipping the duplicate proof stage.
Core comparison: Key indicators for the selection of sovereign chains and SIGN
SIGN's 'growth proposition': How does the roadmap address industry concerns?
The market's concerns about SIGN mainly focus on two points, but the project has already provided a clear solution path:
In response to the issue of 'doubtful sources of trust', SIGN's solution is to build a 'layered trust system': on one hand, incorporating authoritative entities such as government agencies and Sequoia Capital as certification nodes, whose issued certificates automatically enhance trust weight; on the other hand, launching a 'certificate traceability mechanism' through the SignScan indexing tool, allowing users and project teams to query the qualifications and past performance records of the certificate issuers, filtering out invalid certifications from air projects from the source. Currently, countries like the UAE and Thailand have already put official certificates on-chain through SIGN Stack, and the trust endorsement capability of such sovereign-level certificates far exceeds that of ordinary project certifications.$SIGN
In response to the 'weakness in value capture' issue, SIGN's roadmap is clear: in the short term, binding value through SIGN tokens as protocol fuel (certificate generation and verification require consumption of tokens) and governance tokens (participation in protocol parameter adjustments); in the medium term, launching the Sovereign Layer2 solution to build a prototype of 'on-chain nations', accommodating more asset transfer scenarios; in the long term, continuously generating revenue through enterprise-level service fees (e.g., government digital service deployments, large project asset distributions). Currently, it has achieved annual revenue of 15 million USD, becoming one of the few projects in the field with a real income model.$BTC
Endgame thinking: Should trust in Web3 move towards 'building walls' or 'interconnection'?
Currently, the entire Web3 industry is caught in a state of 'involutionary fragmentation': the more sovereign chains there are, the more fragmented the user groups become, and the higher the trust costs across ecosystems; project teams spend a lot of energy fighting witch hunts and filtering, but no one thinks about the core issue of whether 'the filtering results can be reused'.#Sign地缘政治基建
Three core conclusions to help you quickly choose a model:
If you are a project team needing precise user filtering in the short term without cross-ecosystem cooperation, sovereign chains are an efficient tool;
If you are a long-term investor or user, the 'trust standardization' represented by SIGN is an inevitable trend in the industry, with its multi-chain interoperability and national-level landing cases being scarce;
The ultimate outcome of the industry will not be a single model winning, but rather a combination of 'sovereign chains + SIGN' — sovereign chains are responsible for refined operations within the ecosystem, while SIGN is responsible for the flow of trust across ecosystems.
Finally, let me pose a sharp but real question: The core of Web3 is 'user sovereignty', but if we have to prove the on-chain behaviors and contributions accumulated across 50 projects from scratch for the 51st project, do these so-called 'on-chain assets' truly deserve the term 'asset'? Perhaps what the industry really needs is not more complex filtering rules or more closed ecosystem barriers, but a set of 'trust consensus' that allows quality users to be recognized across the entire network. Do you think Web3 will ultimately move towards 'building walls' or 'interconnection'? Feel free to share your thoughts in the comments!